The Ansible playbook in this repository configures a SOCKS proxy for NetGuard. The server runs on FreeBSD 13 and uses the Shadowsocks package.
Assumption: The instance runs in Google Cloud using the Terraform script below,
- terraform__gcloud-instance
- GitHub: github.com/k3karthic/ansible__shadowsocks
- Codeberg: codeberg.org/k3karthic/ansible__shadowsocks
Install the following before running the playbook,
$ ansible-galaxy collection install community.general
$ pip install google-auth requests
$ ansible-galaxy collection install google.cloud
The Google Ansible Inventory Plugin populates public FreeBSD instances.
The target FreeBSD instance must have the label shadowsocks_service: yes.
- Create
inventory/google.gcp_compute.ymlbased oninventory/google.gcp_compute.yml.sample,- Specify the project ID
- Specify the zone where you have deployed your server on Google Cloud
- Configure the authentication,
- Application Default Credentials (
auth_kind: application)- Import credentials from the Google Cloud Environment (e.g, Google Cloud Shell)
- Import credentials from Google Cloud SDK if installed
- Service Account (
auth_kind: serviceaccount)- Use a service account for authentication. Refer cloud.google.com/docs/authentication/production#create_service_account.
- Set
service_account_fileto the credential file orservice_account_contentsto the json content
- Machine Account (
auth_kind: machineaccount)- When running on Compute Engine, use the service account attached to the instance
- Application Default Credentials (
- Set username and ssh authentication in
inventory/group_vars/all.yml - Set the password in
files/config.jsonusingfiles/config.json.sample
Run the playbook using the following command,
$ ./bin/apply.sh
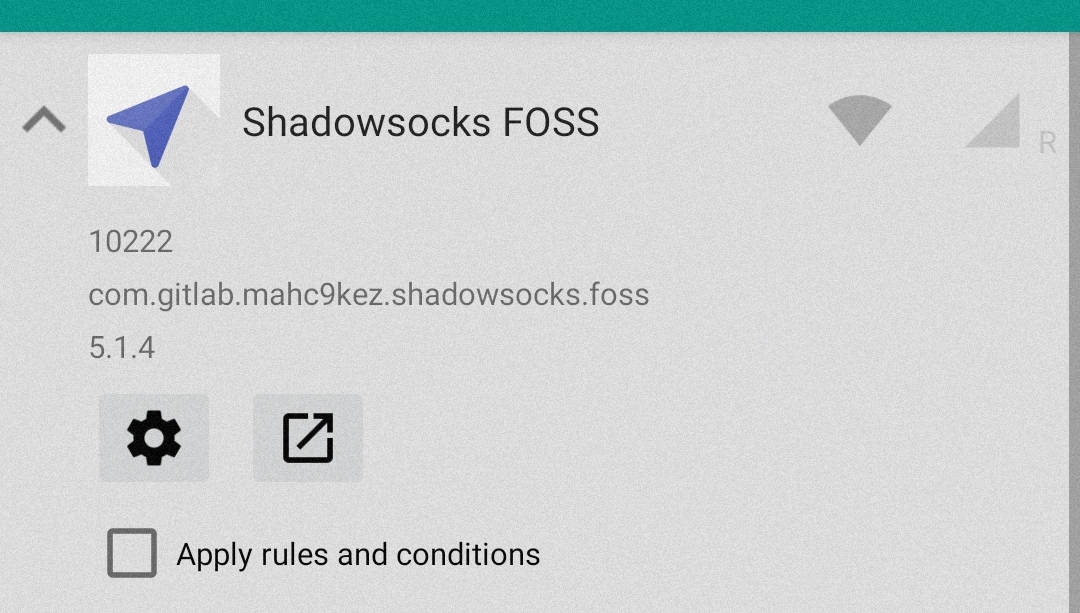
Step 1. Install Shadowsocks FOSS. Exempt it in NetGuard by de-selecting the “Apply rules and conditions” checkbox.
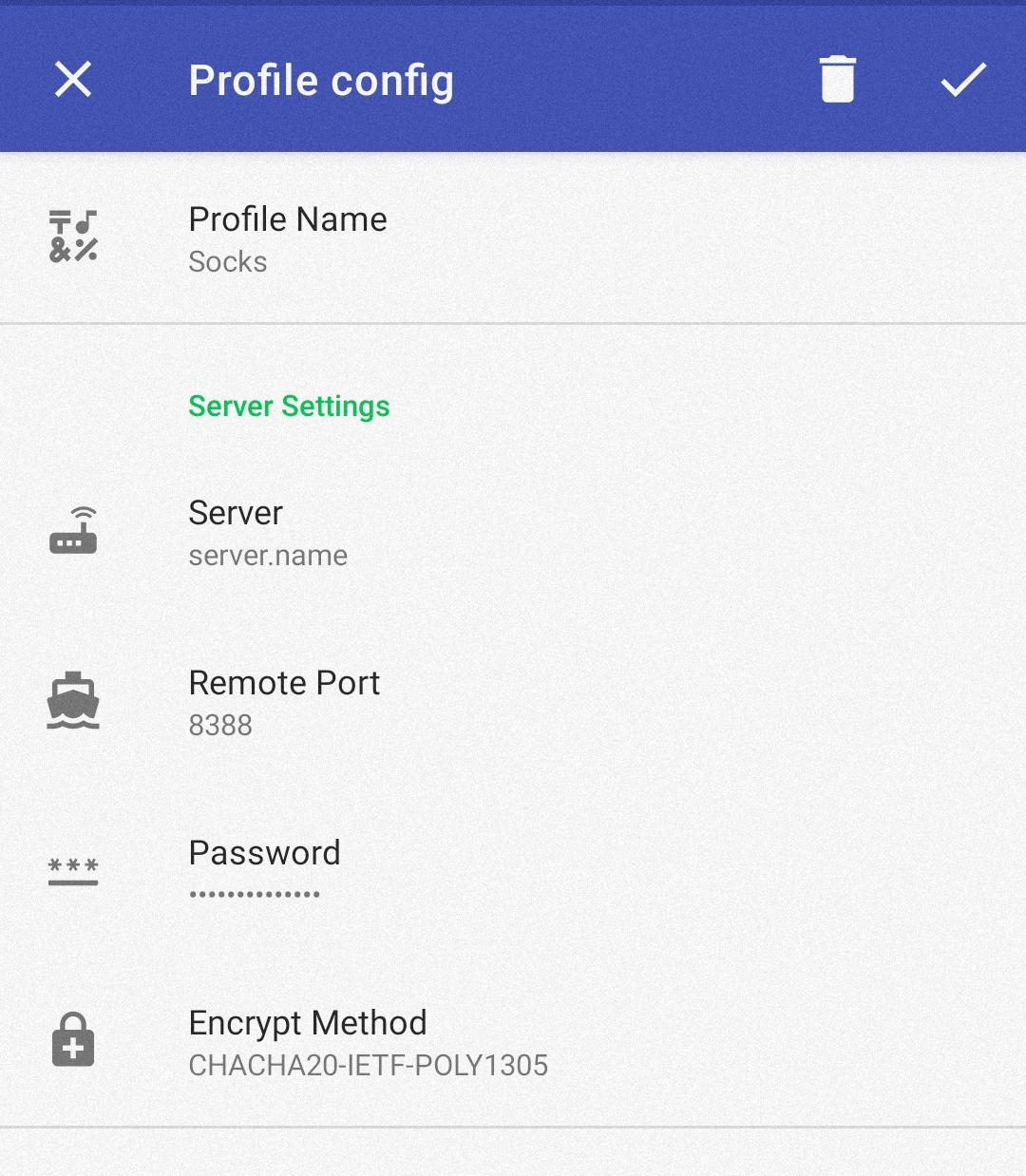
Step 2. Save the server configuration as a profile in Shadowsocks FOSS,
- Server — Instance hostname
- Port — 8388
- Password — Password set in
files/config.json - Encrypt Method — CHACHA20-IETF-POLY1305
Encrypt sensitive files (Shadowsocks config, SSH private keys) before saving them. .gitignore must contain the unencrypted file paths.
Use the following command to decrypt the files after cloning the repository,
$ ./bin/decrypt.sh
Use the following command after running terraform to update the encrypted files,
$ ./bin/encrypt.sh <gpg key id>