- Read Research: https://wildptr.io/winrar-cve-2023-40477-poc-new-vulnerability-winrar-security-research/
- Recvol3.cpp Vulnerability: https://www.rarlab.com/vuln_rev3_names.html, https://www.win-rar.com/
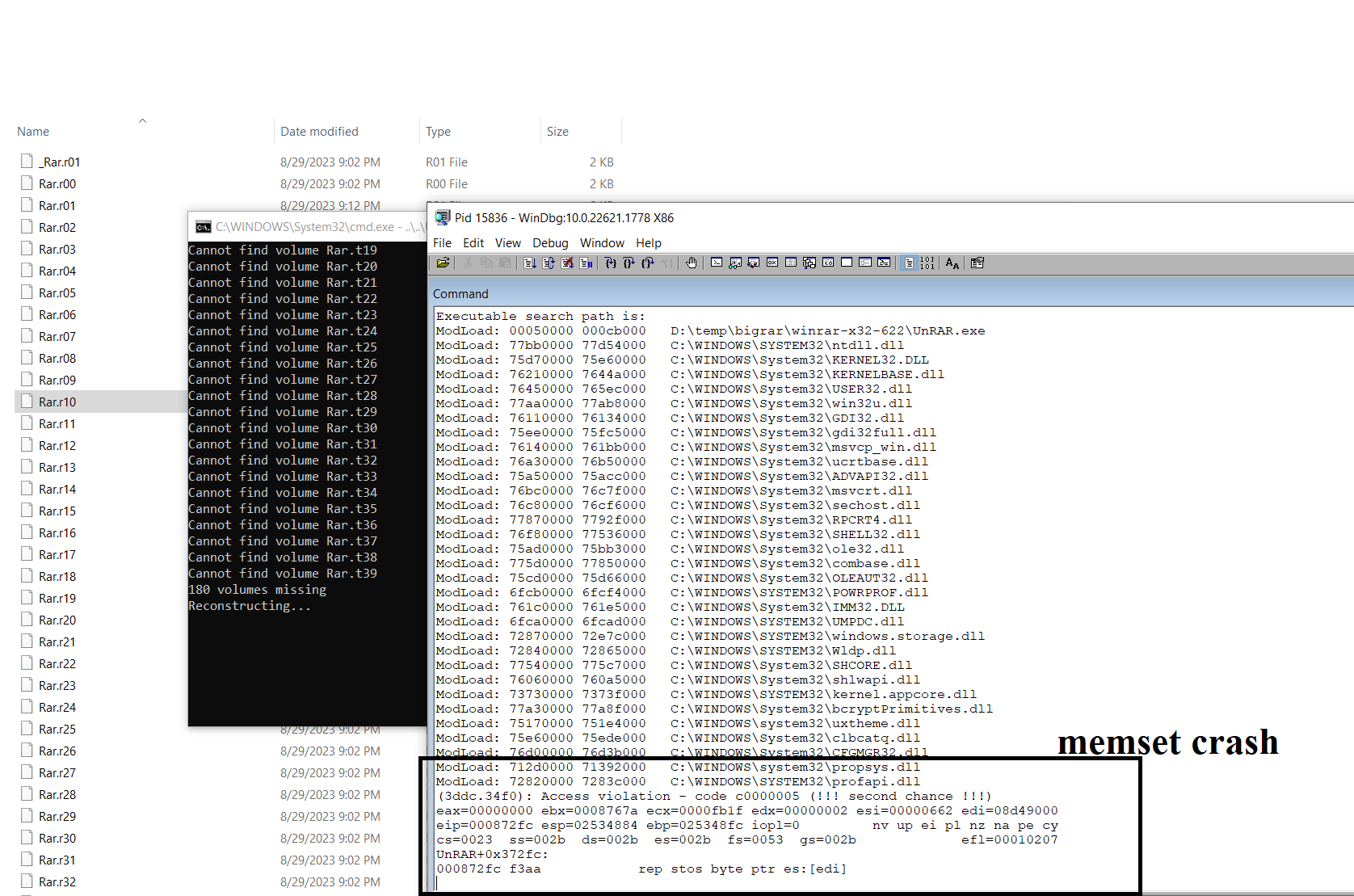
- Vulnerable: WinRAR <= 6.22
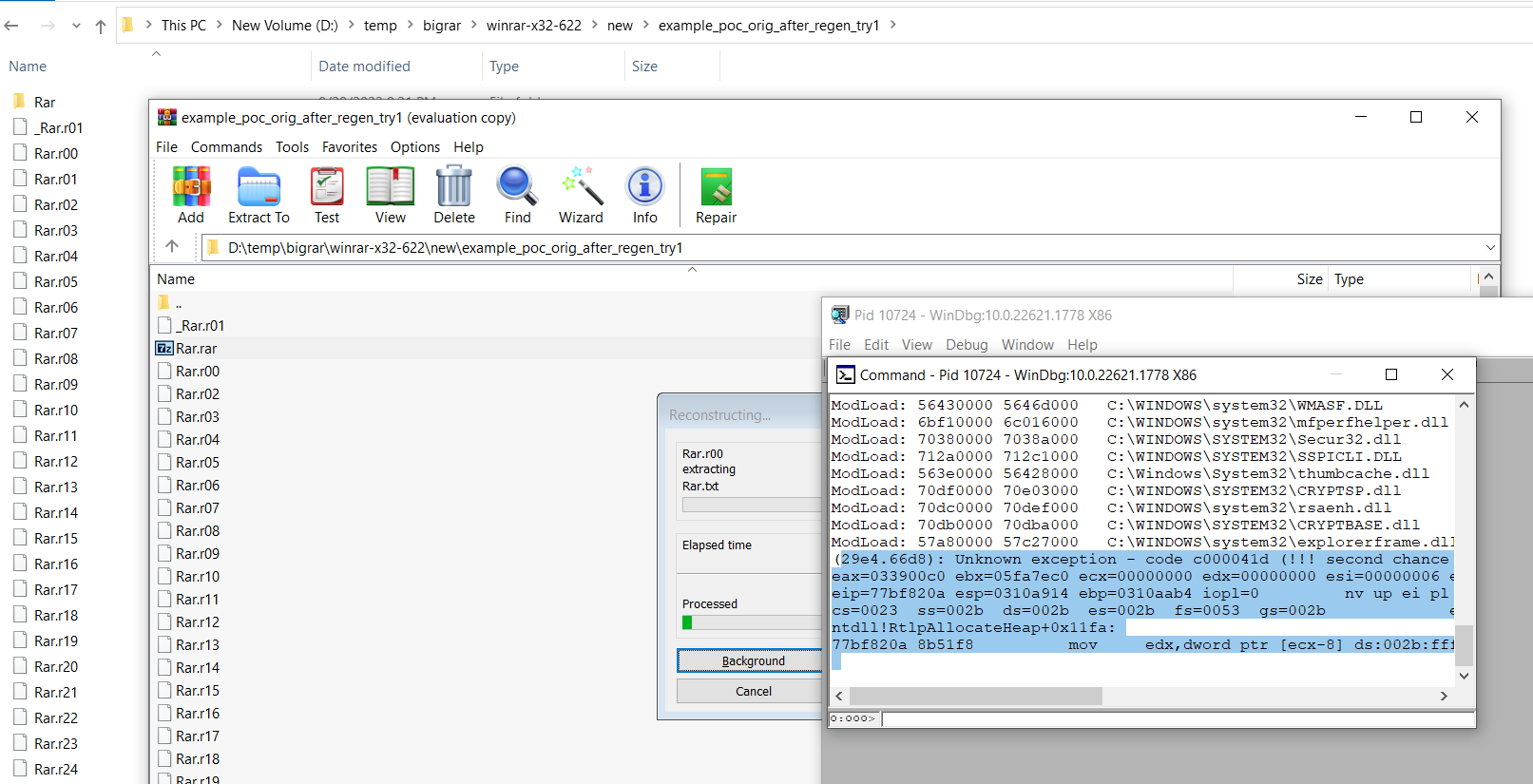
You can generate your own PoC OR just test attached demo RAR file (verified to crash winrar-6.22 upon extraction).
- PoC Generate - follow
cve_2023_40477_poc.py - Demo RAR file - Just extract
Rar.rarfromexample_poc_after_gen.
- Memset Crash-
Use at your own responsibility - The publisher, author or any of its affiliates aren't responsible for any actions caused, made or generated by using this code and/or repository. This is just & solely for educational purposes and includes demo example only, not to harm or cause any impact. Use this for educational purposes only. Do not use this piece of code for any unethical or unintended behaviour.