terraform-aws-cloudtrail-cloudwatch-alarms
Terraform module for creating alarms for tracking important changes and occurances from cloudtrail.
This module creates a set of filter metrics and alarms based on the security best practices covered in the AWS CIS Foundations Benchmark guide.
This project is part of our comprehensive "SweetOps" approach towards DevOps.
It's 100% Open Source and licensed under the APACHE2.
Usage
module "cloudtrail_api_alarms" {
source = "git::https://github.com/cloudposse/terraform-aws-cloudtrail-cloudwatch-alarms.git"
region = "${var.region}"
log_group_name = "${aws_cloudwatch_log_group.default.name}"
}For detailed usage which includes setting up cloudtrail, cloudwatch logs, roles, policies, and the s3 bucket - as well as using this module see the example directory
Examples
Here's a complete example of using this terraform-aws-cloudtrail-cloudwatch-alarms module.
Inputs
| Name | Description | Type | Default | Required |
|---|---|---|---|---|
| add_sns_policy | Attach a policy that allows the notifications through to the SNS topic endpoint | string | false |
no |
| additional_endpoint_arns | Any alert endpoints, such as autoscaling, or app scaling endpoint arns that will respond to an alert | list | <list> |
no |
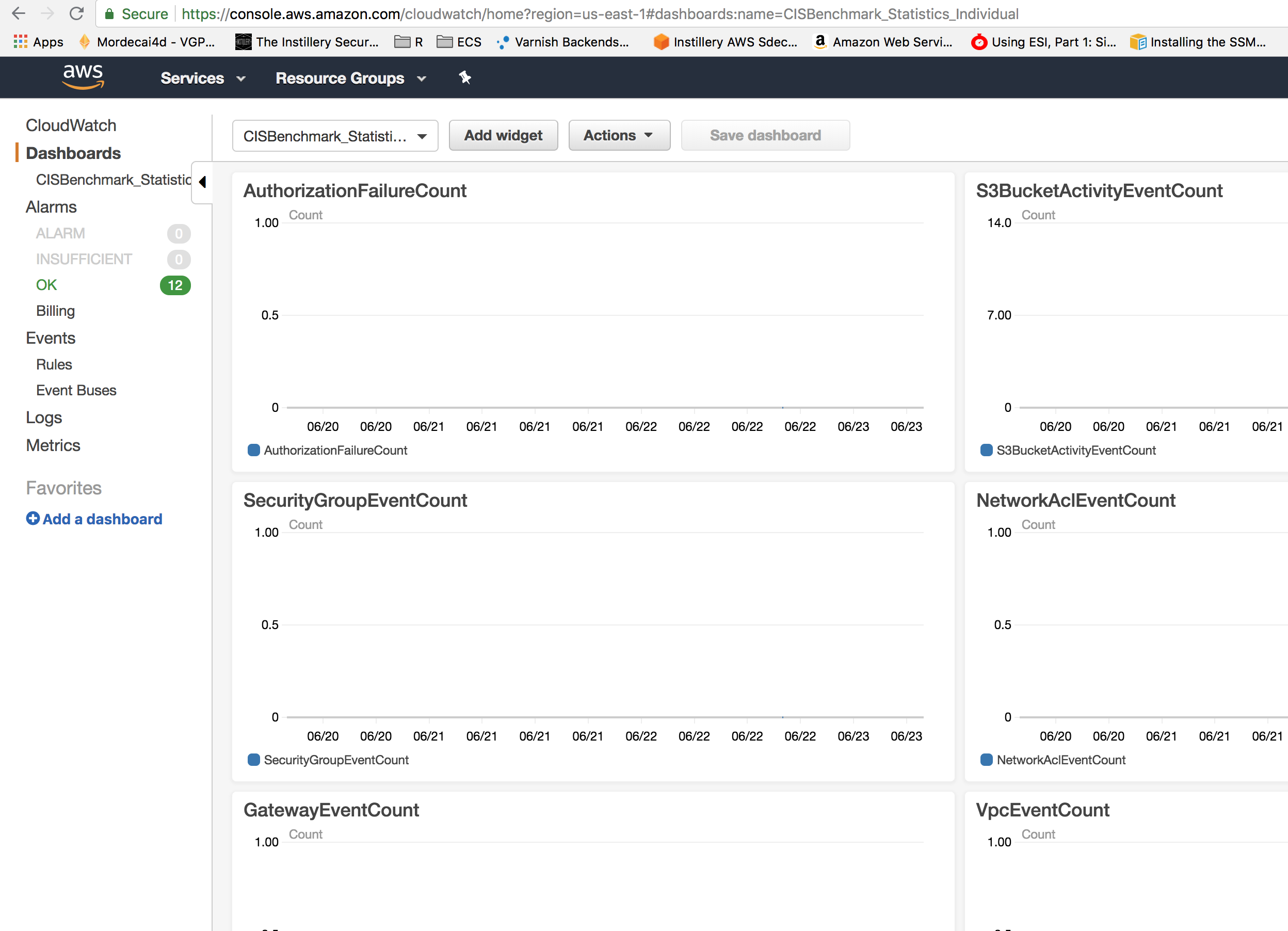
| create_dashboard | When true a dashboard that displays tha statistics as a line graph will be created in CloudWatch | string | true |
no |
| log_group_name | The cloudtrail cloudwatch log group name | string | - | yes |
| metric_namespace | A namespace for grouping all of the metrics together | string | CISBenchmark |
no |
| region | The region that should be monitored for unauthorised AWS API Access. Current region used if none provied. | string | `` | no |
| sns_topic_arn | An SNS topic ARN that has already been created. Its policy must already allow access from CloudWatch Alarms, or set add_sns_policy to true |
string | `` | no |
Outputs
| Name | Description |
|---|---|
| dashboard_combined | URL to CloudWatch Combined Metric Dashboard |
| dashboard_individual | URL to CloudWatch Individual Metric Dashboard |
| sns_topic_arn | The ARN of the SNS topic used |
Metrics Tracked
| Alarm's Name | Description |
|---|---|
AuthorizationFailureCount |
Alarms when an unauthorized API call is made. |
S3BucketActivityEventCount |
Alarms when an API call is made to S3 to put or delete a Bucket, Bucket Policy or Bucket ACL. |
SecurityGroupEventCount |
Alarms when an API call is made to create, update or delete a Security Group. |
NetworkAclEventCount |
Alarms when an API call is made to create, update or delete a Network ACL. |
GatewayEventCount |
Alarms when an API call is made to create, update or delete a Customer or Internet Gateway. |
VpcEventCount |
Alarms when an API call is made to create, update or delete a VPC, VPC peering connection or VPC connection to classic. |
EC2InstanceEventCount |
Alarms when an API call is made to create, terminate, start, stop or reboot an EC2 instance. |
EC2LargeInstanceEventCount |
Alarms when an API call is made to create, terminate, start, stop or reboot a 4x-large or greater EC2 instance. |
CloudTrailEventCount |
Alarms when an API call is made to create, update or delete a .cloudtrail. trail, or to start or stop logging to a trail. |
ConsoleSignInFailureCount |
Alarms when an unauthenticated API call is made to sign into the console. |
IAMPolicyEventCount |
Alarms when an API call is made to change an IAM policy. |
ConsoleSignInWithoutMfaCount |
Alarms when a user logs into the console without MFA. |
RootAccountUsageCount |
Alarms when a root account usage is detected. |
KMSKeyPendingDeletionErrorCount |
Alarms when a customer created KMS key is pending deletion. |
AWSConfigChangeCount |
Alarms when AWS Config changes. |
RouteTableChangesCount |
Alarms when route table changes are detected. |
Dashboard Created
Two CloudWatch Dashboards can be created as well, and will be automatically created by default.
Credits
The alarm metric names, descriptions, and filters from this repository were used.
With many thanks to Anton Babenko for pointing it out and saving us a lot of time scouring reference documents and describing alarms!
Related Projects
Check out these related projects.
- terraform-aws-cloudtrail - Terraform module to provision an AWS CloudTrail and an encrypted S3 bucket with versioning to store CloudTrail logs
- terraform-aws-cloudtrail-s3-bucket - S3 bucket with built in IAM policy to allow CloudTrail logs
- terraform-aws-cloudwatch-logs - Terraform Module to Provide a CloudWatch Logs Endpoint
- terraform-aws-cloudwatch-flow-logs - Terraform module for enabling flow logs for vpc and subnets.
- terraform-aws-ec2-cloudwatch-sns-alarms - Terraform module that configures CloudWatch SNS alerts for EC2 instances
- terraform-aws-ecs-cloudwatch-sns-alarms - Terraform module for creating ECS service level alerts that go to an SNS endpoint
- terraform-aws-efs-cloudwatch-sns-alarms - Terraform module that configures CloudWatch SNS alerts for EFS
- terrform-aws-elasticache-cloudwatch-sns-alarms - Terraform module that configures CloudWatch SNS alerts for ElastiCache
- terraform-aws-lambda-cloudwatch-sns-alarms - Terraform module for creating a set of Lambda alarms and outputting to an endpoint
- terraform-aws-rds-cloudwatch-sns-alarms - Terraform module that configures important RDS alerts using CloudWatch and sends them to an SNS topic
- terraform-aws-sqs-cloudwatch-sns-alarms - Terraform module for creating alarms for SQS and notifying endpoints
Help
Got a question?
File a GitHub issue, send us an email or join our Slack Community.
Commercial Support
Work directly with our team of DevOps experts via email, slack, and video conferencing.
We provide commercial support for all of our Open Source projects. As a Dedicated Support customer, you have access to our team of subject matter experts at a fraction of the cost of a full-time engineer.
- Questions. We'll use a Shared Slack channel between your team and ours.
- Troubleshooting. We'll help you triage why things aren't working.
- Code Reviews. We'll review your Pull Requests and provide constructive feedback.
- Bug Fixes. We'll rapidly work to fix any bugs in our projects.
- Build New Terraform Modules. We'll develop original modules to provision infrastructure.
- Cloud Architecture. We'll assist with your cloud strategy and design.
- Implementation. We'll provide hands-on support to implement our reference architectures.
Community Forum
Get access to our Open Source Community Forum on Slack. It's FREE to join for everyone! Our "SweetOps" community is where you get to talk with others who share a similar vision for how to rollout and manage infrastructure. This is the best place to talk shop, ask questions, solicit feedback, and work together as a community to build sweet infrastructure.
Contributing
Bug Reports & Feature Requests
Please use the issue tracker to report any bugs or file feature requests.
Developing
If you are interested in being a contributor and want to get involved in developing this project or help out with our other projects, we would love to hear from you! Shoot us an email.
In general, PRs are welcome. We follow the typical "fork-and-pull" Git workflow.
- Fork the repo on GitHub
- Clone the project to your own machine
- Commit changes to your own branch
- Push your work back up to your fork
- Submit a Pull Request so that we can review your changes
NOTE: Be sure to merge the latest changes from "upstream" before making a pull request!
Copyright
Copyright © 2017-2018 Cloud Posse, LLC
License
See LICENSE for full details.
Licensed to the Apache Software Foundation (ASF) under one
or more contributor license agreements. See the NOTICE file
distributed with this work for additional information
regarding copyright ownership. The ASF licenses this file
to you under the Apache License, Version 2.0 (the
"License"); you may not use this file except in compliance
with the License. You may obtain a copy of the License at
https://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing,
software distributed under the License is distributed on an
"AS IS" BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY
KIND, either express or implied. See the License for the
specific language governing permissions and limitations
under the License.
Trademarks
All other trademarks referenced herein are the property of their respective owners.
About
This project is maintained and funded by Cloud Posse, LLC. Like it? Please let us know at hello@cloudposse.com
We're a DevOps Professional Services company based in Los Angeles, CA. We love Open Source Software!
We offer paid support on all of our projects.
Check out our other projects, apply for a job, or hire us to help with your cloud strategy and implementation.
Contributors
Erik Osterman |
Jamie Nelson |
Anton Babenko |
|---|