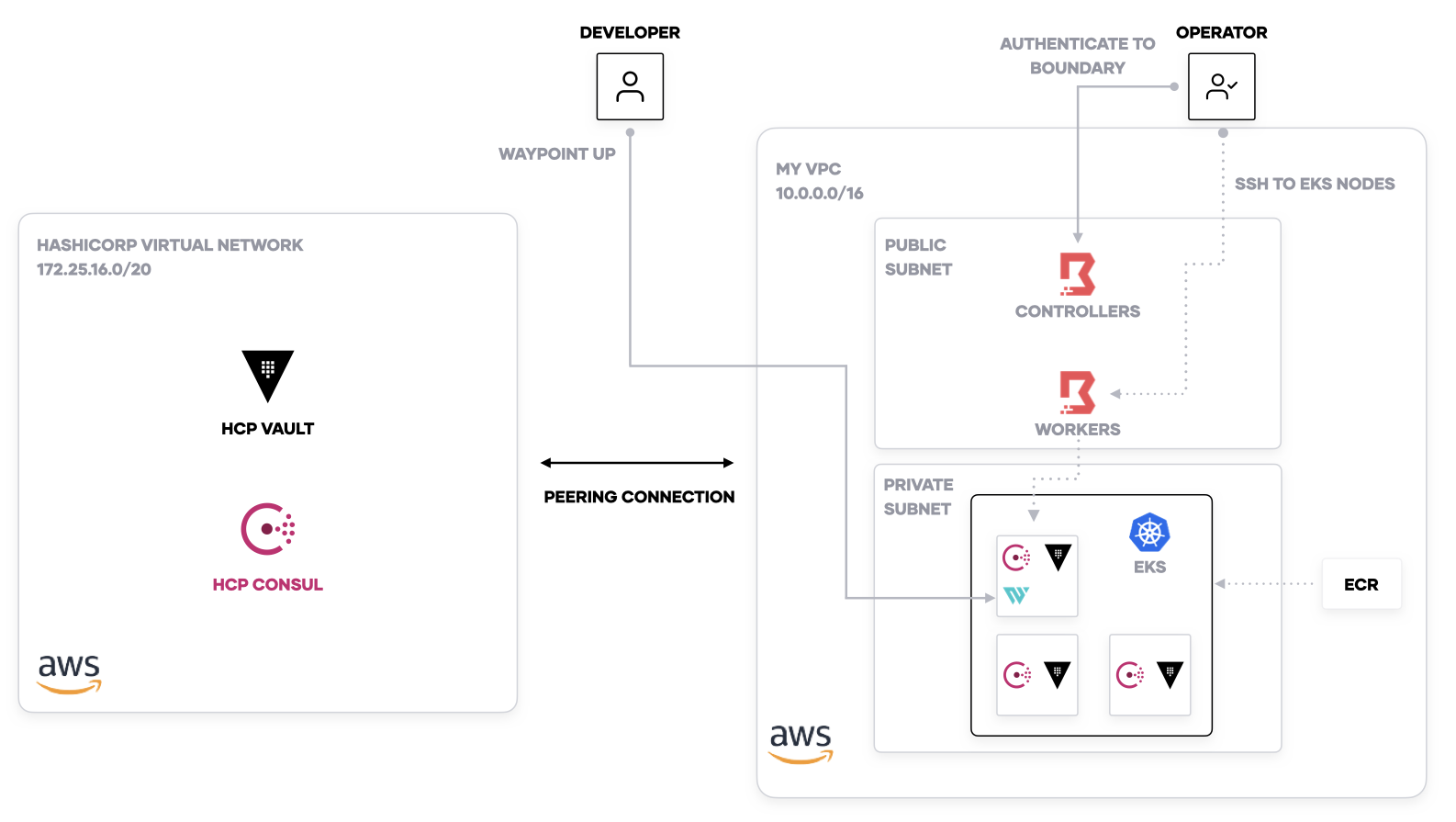
This is the HashiCorp demo application on Amazon EKS. It incorporates the following tools:
- Terraform
- Waypoint
- HCP Consul
- HCP Vault
- Boundary
- Terraform Cloud as Backend, state only (or reconfigure
terraformdirective inproviders.tf) - AWS Account
- HCP Consul (already set up with HVN + Cluster) - you will need the
client_config.jsonandca.pemcopied to thesecretsfolder.- You will need the public URL set as
export CONSUL_HTTP_ADDR=<HCP Consul public URL>. - You will need the bootstrap token set as
export CONSUL_HTTP_TOKEN=<bootstrap token>.
- You will need the public URL set as
- HCP Vault (already set up with HVN + Cluster)
- You will need the private URL set as
export VAULT_ADDR=<HCP Vault public URL>. - You will need the namespace set as
export VAULT_NAMESPACE=admin. - HCP Vault admin token, set as
export VAULT_TOKEN=<Vault token>.
- You will need the private URL set as
jqinstalled- Install HashiCorp Boundary and an SSH key to
~/projects/boundary.- Download Boundary to
~/projects/boundary/bin.mkdir -p ~/projects/boundary/bin cd ~/projects/boundary/bin wget https://releases.hashicorp.com/boundary/0.1.1/boundary_0.1.1_linux_amd64.zip -O boundary.zip unzip boundary.zip rm boundary.zip
- Add an SSH key named
id_rsato~/projects/boundary.
- Download Boundary to
-
Add the Consul and Vault addresses to
terraform.tfvars.name = "hcp-demo" peering_connection_has_been_added_to_hvn = false hcp_vault_private_addr = ${HCP_VAULT_PRIVATE_ADDRESS} hcp_consul_host = ${HCP_CONSUL_PRIVATE_ADDRESS}
-
Run
make setupand enteryesto create the EKS cluster, VPC, and Boundary. -
Set up the peering connection in HVN (do not accept, this configuration will do it for you).
-
In
terraform.tfvars, setpeering_connection_has_been_added_to_hvnto true. This executes the HVN/HCP module to accept the peering connection and add the security groups for HCP Consul.name = "hcp-demo" peering_connection_has_been_added_to_hvn = true hcp_vault_private_addr = ${HCP_VAULT_PRIVATE_ADDRESS} hcp_consul_host = ${HCP_CONSUL_PRIVATE_ADDRESS}
-
Run
make setupand enteryesto configure the HVN peering connection. -
Run
make configure-consulto install the Consul Helm chart to your EKS cluster. -
Run
make configure-vaultto install the Vault Helm chart to your EKS cluster. -
Run
make configure-waypointto install the Waypoint server to your EKS cluster. -
Run
make configure-boundaryto configure the Boundary deployment. -
Run
make configure-consul-intentionsto set up Consul intentions and allow traffic between services.
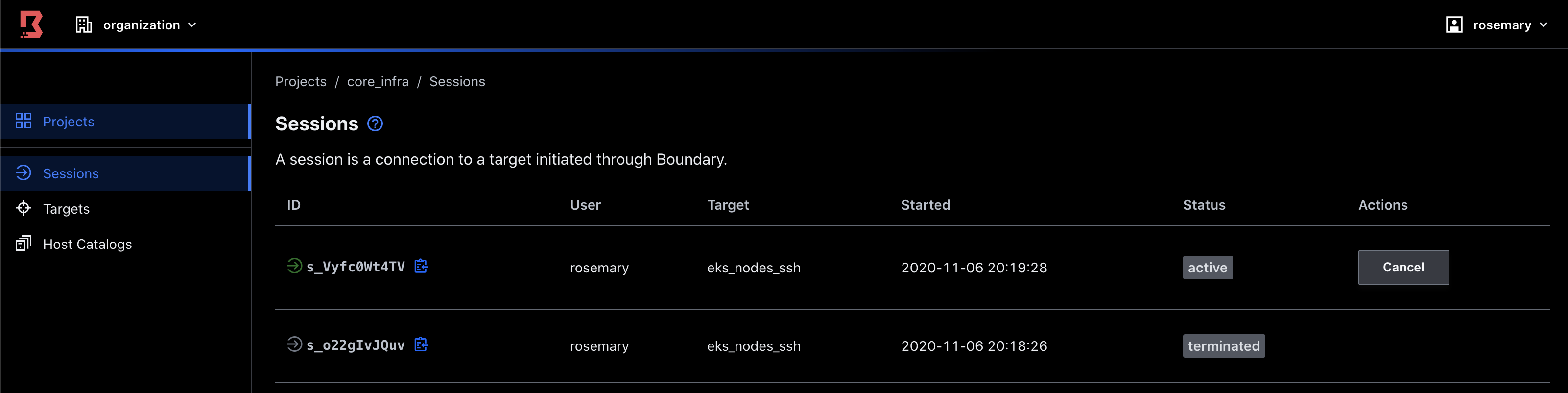
Using Boundary, you can audit and control the SSH sessions to the Kubernetes nodes.
-
Run
make ssh. This will authenticate to Boundary and start an SSH session with the EKS nodes.
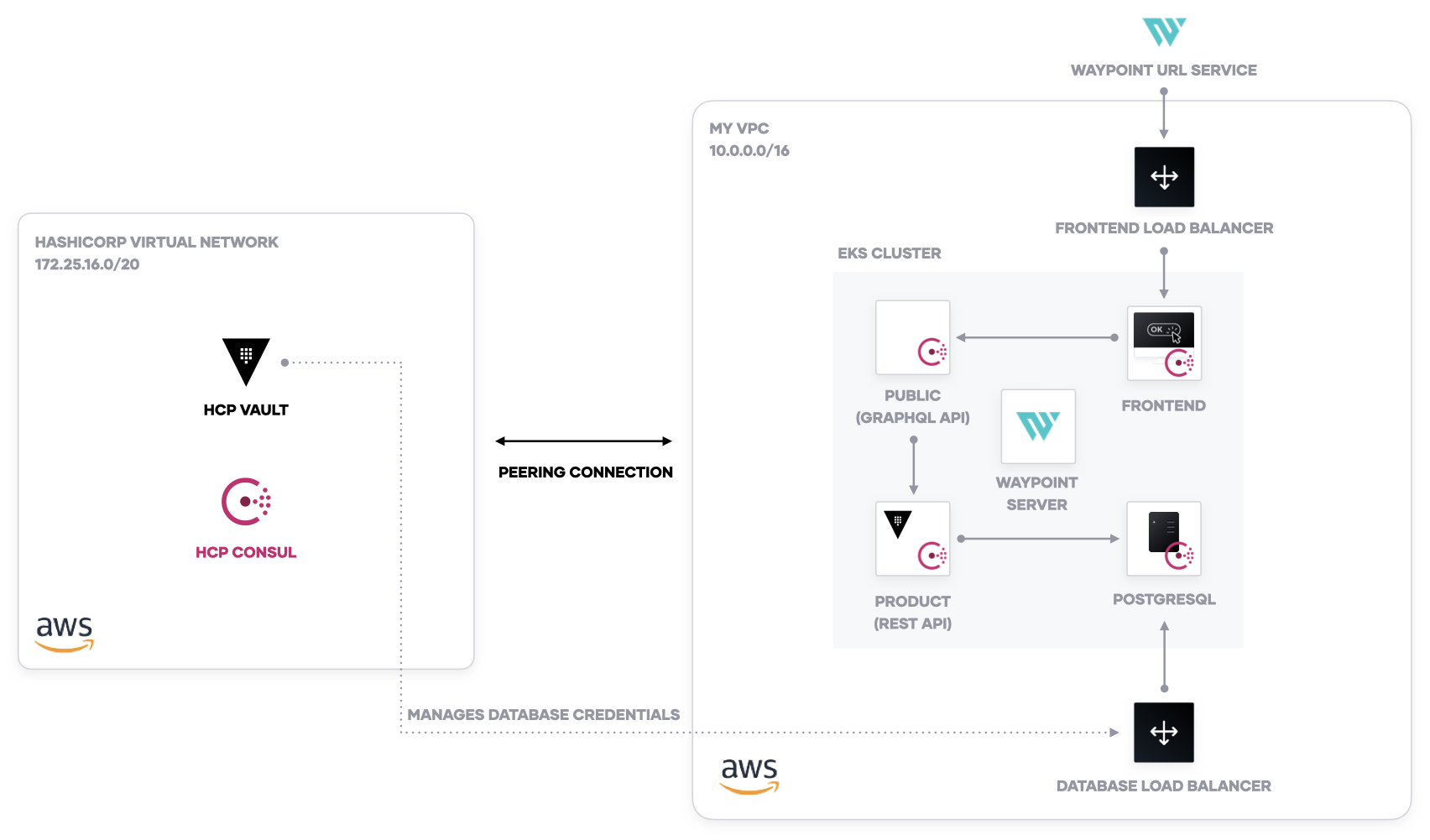
The demo application for a coffee shop uses four services: a frontend, a public API, a products API for a database, and a database.
-
Run
waypoint initto create the Waypoint project. -
Run
waypoint up -app databaseto create a PostgreSQL database. -
Run
make configure-db-credsto configure Vault database secrets engine. -
Run
waypoint up -app productsto create the products API. -
Run
waypoint up -app publicto create the public API endpoint. -
Run
waypoint up -app frontendto create the demo application frontend. Access the URL output by Waypoint.
After you deploy, you will be able to access the deployment URL for the frontend service and examine a product catalog for the coffee shop.
-
The module for Boundary is based on the Boundary AWS Reference Architecture with slight modifications.
-
The demo application comes from the HashiCorp Demo Application.