Rules are code snippets written in JavaScript that are executed as part of the authentication pipeline in Auth0. This happens every time a user authenticates to an application. Rules enable very powerful customizations and extensions to be easily added to Auth0.
An App initiates an authentication request to Auth0 (Step 1), Auth0 routes the request to an Identity Provider through a configured connection (Step 2). The user authenticates successfully (Step3), the user object that represents the logged in user is then passed through the rules pipeline and returned to the app (Step 4).
A rule will run on Step 4 and this is the information each rule will get:
user: user object as it comes from the identity provider. It has the following properties:app_metadata: custom fields that store info about a user that influences the user's access, such as support plan, security roles, or access control groups.created_at: timestamp indicating when the user profile was first createdemail: (unique) user's email addressemail_verified: indicates whether the user has verified their email addressfamily_name: user's family namegiven_name: users's given nameidentities: Contains info retrieved from the identity provider with which the user originally authenticates. Users may also link their profile to multiple identity providers; those identities will then also appear in this array. In some cases, it will also include an API Access Token to be used with the provider. The contents of an individual identity provider object varies by provider, but it will typically include the following:connection: name of the Auth0 connection used to authenticate the userisSocial: indicates whether the connection is a social oneprovider: name of the entity that is authenticating the user, such as Facebook, Google, etc.user_id: user's unique identifier for this connection/providerprofileData: user information associated with the connection. When profiles are linked, it is populated with the associated user info for secondary accounts.
last_password_reset: timestamp indicating the last time the user's password was reset/changed. At user creation, this field does not exist.multifactor: array/list of MFA providers with which the user is enrolled. This array is updated when the user logs in with MFA successfully for the first time, and is not updated when enrollment is completed or when an administrator resets a user's MFA.name: user's full namenickname: user's nicknamepermissions: permissions assigned to the user's ID tokenphone_number: user's phone number. Only valid for users with SMS connections.phone_verified: indicates whether the user has verified their phone number. Only valid for users with SMS connections.picture: URL pointing to the user's profile pictureupdated_at: timestamp indicating when the user's profile was last updated/modified. Changes tolast_loginare considered updates, so most of the time,updated_atwill matchlast_login.user_id: (unique) The user's unique identifieruser_metadata: custom fields that store information about a user that does not impact what they can or cannot access, such as work address, home address, or user preferencesusername: (unique) user's username
context: object containing contextual information of the current authentication transaction. It has the following properties:tenant: string containing the name of the tenantclientID: client id of the application the user is logging in toclientName: name of the application (as defined on the dashboard)client_metadata: object for holding other application properties that are key/value stringsconnection: name of the connection used to authenticate the user (e.g.:twitterorsome-google-apps-domain)connectionID: string containing the connection's unique identifierconnectionStrategy: type of connection. For social connectionconnectionStrategy===connection. For enterprise connections, the strategy will bewaad(Windows Azure AD),ad(Active Directory/LDAP),auth0(database connections), etc.connectionOptions: object representing the options defined on the connection.connectionOptions.tenant_domainis a string containing the domain being used for authentication when using an Enterprise connection.connectionOptions.domain_aliasesis an array containing the optional domains registered as aliases in addition to the primary domain (specified in theconnectionOptions.tenant_domainproperty).connectionMetadata: object representing metadata defined on the connection that are key/value stringsprotocol: authentication protocol. Possible values:oidc-basic-profile(most used, web-based login),oidc-implicit-profile(used on mobile devices and single page apps),oauth2-resource-owner(user/password login typically used on database connections),samlp(SAML protocol used on SaaS apps),wsfed(Ws-Federation used on Microsoft products like Office365),wstrust-usernamemixed(Ws-trust user/password login used on CRM and Office365)),delegation(during the exchange for a delegation token).stats: object containing specific user stats, likestats.loginsCount. Note that any of the counter variables returned as part of thestatsobject do not increase during silent authentication (as whenprompt=none). There are also scenarios where the counter variables might increase yet a rule or set of rules do not execute, as in the case of a successful cross-origin authentication followed by a failed token request.sso: this object will contain information about the Single Sign-on (SSO) transaction (if available). It has the following properties:with_auth0: when a user signs in with SSO to an application where theUse Auth0 instead of the IdP to do Single Sign-Onwith_dbconn: SSO login for a user that logged in through a database connectioncurrent_clients: client IDs using SSO
accessToken: object representing the options defined on the Access Token. You can use this object to add custom namespaced claims to the Access Token.context.accessToken.scopecan be used to change the Access Token's returned scopes. When provided, it is an array containing permissions in string format.idToken: object representing the options defined on the ID Token. Used to add custom namespaced claims to the ID Tokenoriginal_protocol: After a redirect rule has executed and the authentication transaction is resumed, this property will be populated with the original protocol used to initiate the transactionmultifactor: object representing the multifactor settings used in implementing contextual MFAredirect: object used to implement the redirection of a user from a rulesessionID: internal identification for the authentication session. Value is kept only ifprompt=noneis used in the authorization request. Note that the session ID can change after rule execution on other flows, so the value available incontext.sessionIDmight not match the new session ID that the user will receive. This makes this value only meaningful whenprompt=noneis used.request: object containing useful information of the request. It has the following properties:query: querystring properties of the login transaction sent by the applicationbody: body of the POST request on login transactions used onoauth2-resource-ownerorwstrust-usernamemixedprotocols.userAgent: user-agent of the client that is trying to log inip: originating IP address of the user trying to log inhostname: hostname that is being used for the authentication flowgeoip: an object containing geographic IP information. It has the following properties:country_code: two-character code for the country associated with the IP addresscountry_code3: three-character code for the country associated with the IP addresscountry_name: country name associated with the IP addresscity_name: city or town name associated with the IP addresslatitude: latitude associated with the IP addresslongitude: longitude associated with the IP addresstime_zone: timezone associated with the IP addresscontinent_code: two-character code for the continent associated with the IP address
primaryUser: unique user id of the primary account for the user. Used to link user accounts from various identity providersauthentication: object containing information related to the authentication transaction with the following properties:methods: an array of objects containing the authentication methods a user has completed during their session. This opbject contains the following properties:name: a string representing the name of the authentication method that has been completed. It can be one of the following values:federated: social or enterprise connection was used to authenticate the userpwd: database connection was used to authenticate the usersms: SMS connection was used to authenticate the useremail: Passwordless Email connection was used to authenticate the usermfa: the user completed a mulifactor authentication
timestamp: an integer indicating the time in seconds at which the authentication method took place in Unix Epoch time. You can see a sample use case of thecontext.authentication.methodsproperty in the Require MFA once per session Rule.
authorization: object containing information related to the authorization transaction with the following properties:roles: an array of strings containing the names of a user's assigned roles. You can see a sample use case using thecontext.authorization.rolesproperty to add roles to tokens in Sample Use Cases: Rules with Authorization.
samlConfiguration: an object that controls the behavior of the SAML and WS-Fed endpoints. Useful for advanced claims mapping and token enrichment (only available forsamlpandwsfedprotocol).
Note that rules will also have access to several modules defined globally, including auth0, referring to https://github.com/auth0/node-auth0. Other modules available within rules are defined at https://auth0.com/docs/appliance/modules (relevant to both appliance and cloud)
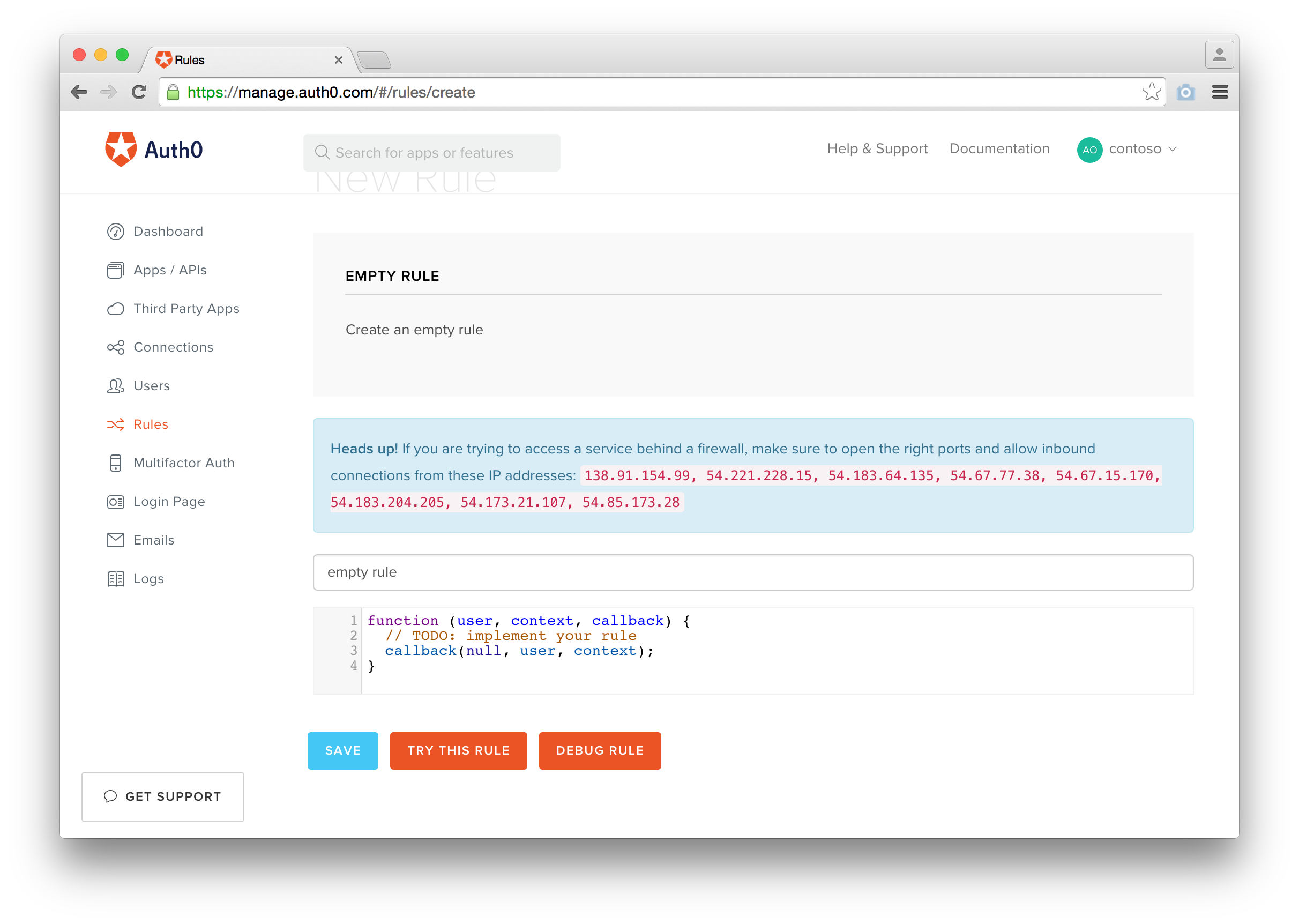
This is the rules editor inside Auth0:
- Update the markdown files to update the rule and commit your changes
- Update the version by executing:
npm version [patch|minor|major]There is a
preversionscript in thepackage.jsonfile that executes the following command:./build && git add rules.json && git commit -m 'update rules.json
- Push your changes to master including the tags
git push origin master --tags- Send events to MixPanel Docs | Rule
- Query User Profile in FullContact Docs | Rule
- Add a Lead in Salesforce Docs | Rule
- Get an Appery Session Token Rule
More information about them here.
If you have found a bug or if you have a feature request, please report them at this repository issues section. Please do not report security vulnerabilities on the public GitHub issue tracker. The Responsible Disclosure Program details the procedure for disclosing security issues.
This project is licensed under the MIT license. See the LICENSE file for more info.