Terraform module for multi-AZ subnets provisioning.
The module creates private and public subnets in the provided Availability Zones.
The public subnets are routed to the Internet Gateway specified by var.igw_id.
nat_gateway_enabled flag controls the creation of NAT Gateways in the public subnets.
The private subnets are routed to the NAT Gateways provided in the var.az_ngw_ids map.
This project is part of our comprehensive "SweetOps" approach towards DevOps.
It's 100% Open Source and licensed under the APACHE2.
 Example of
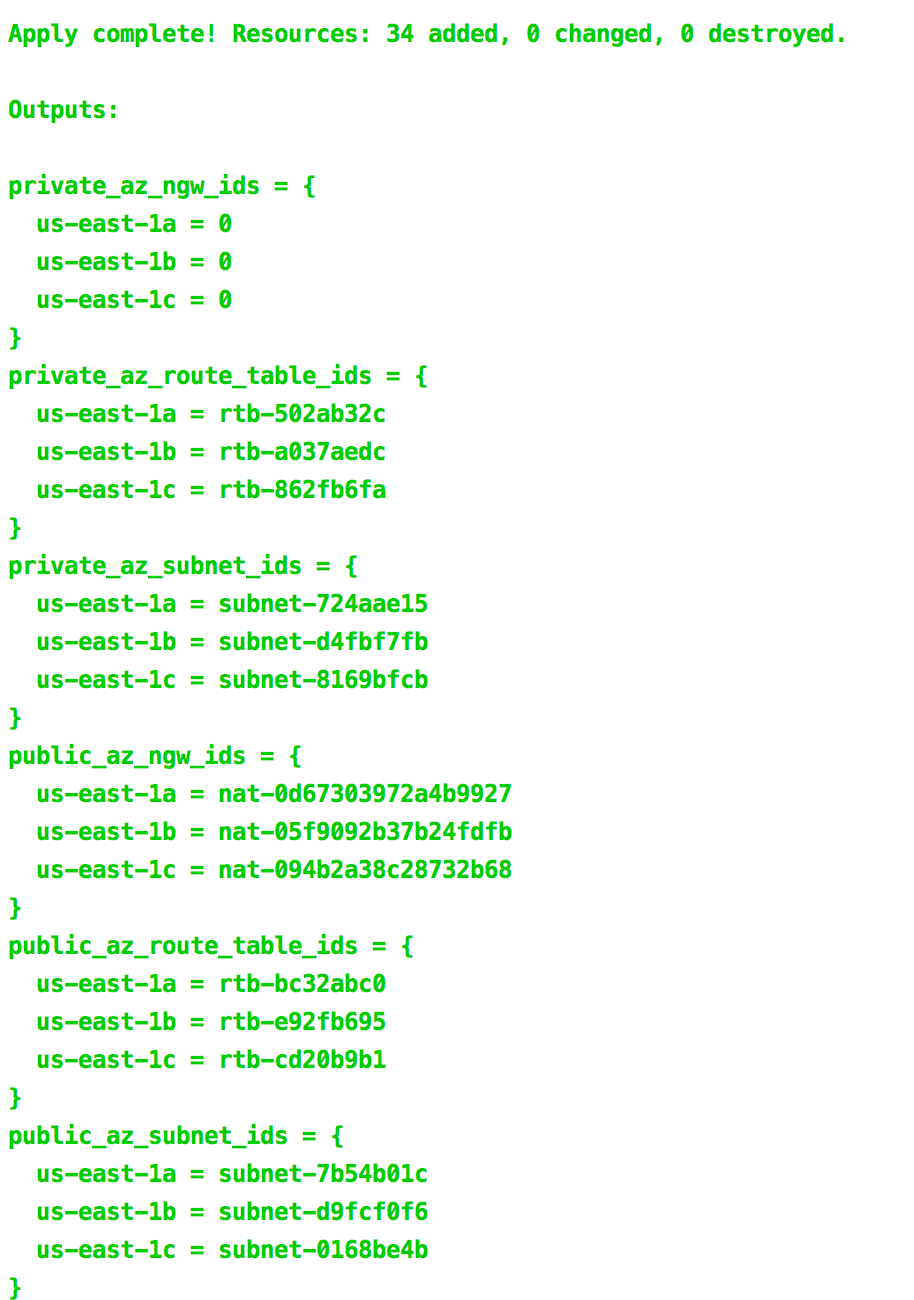
Example of terraform apply outputs
module "vpc" {
source = "git::https://github.com/cloudposse/terraform-aws-vpc.git?ref=master"
namespace = "${var.namespace}"
name = "vpc"
stage = "${var.stage}"
cidr_block = "${var.cidr_block}"
}
locals {
public_cidr_block = "${cidrsubnet(module.vpc.vpc_cidr_block, 1, 0)}"
private_cidr_block = "${cidrsubnet(module.vpc.vpc_cidr_block, 1, 1)}"
}
module "public_subnets" {
source = "git::https://github.com/cloudposse/terraform-aws-multi-az-subnets.git?ref=master"
namespace = "${var.namespace}"
stage = "${var.stage}"
name = "${var.name}"
availability_zones = ["us-east-1a", "us-east-1b", "us-east-1c"]
vpc_id = "${module.vpc.vpc_id}"
cidr_block = "${local.public_cidr_block}"
type = "public"
igw_id = "${module.vpc.igw_id}"
nat_gateway_enabled = "true"
}
module "private_subnets" {
source = "git::https://github.com/cloudposse/terraform-aws-multi-az-subnets.git?ref=master"
namespace = "${var.namespace}"
stage = "${var.stage}"
name = "${var.name}"
availability_zones = ["us-east-1a", "us-east-1b", "us-east-1c"]
vpc_id = "${module.vpc.vpc_id}"
cidr_block = "${local.private_cidr_block}"
type = "private"
# Map of AZ names to NAT Gateway IDs that was created in "public_subnets" module
az_ngw_ids = "${module.public_subnets.az_ngw_ids}"
# Need to explicitly provide the count since Terraform currently can't use dynamic count on computed resources from different modules
# https://github.com/hashicorp/terraform/issues/10857
# https://github.com/hashicorp/terraform/issues/12125
# https://github.com/hashicorp/terraform/issues/4149
az_ngw_count = 3
}Given the following configuration
module "vpc" {
source = "git::https://github.com/cloudposse/terraform-aws-vpc.git?ref=master"
namespace = "${var.namespace}"
name = "vpc"
stage = "${var.stage}"
cidr_block = "${var.cidr_block}"
}
locals {
public_cidr_block = "${cidrsubnet(module.vpc.vpc_cidr_block, 1, 0)}"
private_cidr_block = "${cidrsubnet(module.vpc.vpc_cidr_block, 1, 1)}"
}
module "public_subnets" {
source = "git::https://github.com/cloudposse/terraform-aws-multi-az-subnets.git?ref=master"
namespace = "${var.namespace}"
stage = "${var.stage}"
name = "${var.name}"
availability_zones = ["us-east-1a", "us-east-1b", "us-east-1c"]
vpc_id = "${module.vpc.vpc_id}"
cidr_block = "${local.public_cidr_block}"
type = "public"
igw_id = "${module.vpc.igw_id}"
nat_gateway_enabled = "true"
}
module "private_subnets" {
source = "git::https://github.com/cloudposse/terraform-aws-multi-az-subnets.git?ref=master"
namespace = "${var.namespace}"
stage = "${var.stage}"
name = "${var.name}"
availability_zones = ["us-east-1a", "us-east-1b", "us-east-1c"]
vpc_id = "${module.vpc.vpc_id}"
cidr_block = "${local.private_cidr_block}"
type = "private"
az_ngw_ids = "${module.public_subnets.az_ngw_ids}"
az_ngw_count = 3
}
output "private_az_subnet_ids" {
value = "${module.private_subnets.az_subnet_ids}"
}
output "public_az_subnet_ids" {
value = "${module.public_subnets.az_subnet_ids}"
}the output Maps of AZ names to subnet IDs look like these
public_az_subnet_ids = {
us-east-1a = subnet-ea58d78e
us-east-1b = subnet-556ee131
us-east-1c = subnet-6f54db0b
}
private_az_subnet_ids = {
us-east-1a = subnet-376de253
us-east-1b = subnet-9e53dcfa
us-east-1c = subnet-a86fe0cc
}and the created subnet IDs could be found by the AZ names using map["key"] or lookup(map, key, [default]),
for example:
public_az_subnet_ids["us-east-1a"]
lookup(private_az_subnet_ids, "us-east-1b")
Available targets:
help Help screen
help/all Display help for all targets
help/short This help short screen
lint Lint terraform code
| Name | Description | Type | Default | Required |
|---|---|---|---|---|
| attributes | Additional attributes (e.g. policy or role) |
list | <list> |
no |
| availability_zones | List of Availability Zones (e.g. ['us-east-1a', 'us-east-1b', 'us-east-1c']) |
list | <list> |
no |
| az_ngw_count | Count of items in the az_ngw_ids map. Needs to be explicitly provided since Terraform currently can't use dynamic count on computed resources from different modules. hashicorp/terraform#10857 |
string | 0 |
no |
| az_ngw_ids | Only for private subnets. Map of AZ names to NAT Gateway IDs that are used as default routes when creating private subnets | map | <map> |
no |
| cidr_block | Base CIDR block which is divided into subnet CIDR blocks (e.g. 10.0.0.0/16) |
string | - | yes |
| delimiter | Delimiter to be used between namespace, stage, name and attributes |
string | - |
no |
| enabled | Set to false to prevent the module from creating any resources | string | true |
no |
| igw_id | Internet Gateway ID that is used as a default route when creating public subnets (e.g. igw-9c26a123) |
string | `` | no |
| max_subnets | Maximum number of subnets that can be created. The variable is used for CIDR blocks calculation | string | 6 |
no |
| name | Application or solution name | string | - | yes |
| namespace | Namespace (e.g. cp or cloudposse) |
string | - | yes |
| nat_gateway_enabled | Flag to enable/disable NAT Gateways creation in public subnets | string | true |
no |
| private_network_acl_egress | Egress network ACL rules | list | <list> |
no |
| private_network_acl_id | Network ACL ID that is added to the private subnets. If empty, a new ACL will be created | string | `` | no |
| private_network_acl_ingress | Egress network ACL rules | list | <list> |
no |
| public_network_acl_egress | Egress network ACL rules | list | <list> |
no |
| public_network_acl_id | Network ACL ID that is added to the public subnets. If empty, a new ACL will be created | string | `` | no |
| public_network_acl_ingress | Egress network ACL rules | list | <list> |
no |
| stage | Stage (e.g. prod, dev, staging) |
string | - | yes |
| tags | Additional tags (e.g. map(BusinessUnit,XYZ) |
map | <map> |
no |
| type | Type of subnets to create (private or public) |
string | private |
no |
| vpc_id | VPC ID | string | - | yes |
| Name | Description |
|---|---|
| az_ngw_ids | Map of AZ names to NAT Gateway IDs (only for public subnets) |
| az_route_table_ids | Map of AZ names to Route Table IDs |
| az_subnet_ids | Map of AZ names to subnet IDs |
Check out these related projects.
- terraform-aws-named-subnets - Terraform module for named subnets provisioning.
- terraform-aws-dynamic-subnets - Terraform module for public and private subnets provisioning in existing VPC
- terraform-aws-vpc - Terraform Module that defines a VPC with public/private subnets across multiple AZs with Internet Gateways
- terraform-aws-cloudwatch-flow-logs - Terraform module for enabling flow logs for vpc and subnets.
Got a question?
File a GitHub issue, send us an email or join our Slack Community.
Work directly with our team of DevOps experts via email, slack, and video conferencing.
We provide commercial support for all of our Open Source projects. As a Dedicated Support customer, you have access to our team of subject matter experts at a fraction of the cost of a full-time engineer.
- Questions. We'll use a Shared Slack channel between your team and ours.
- Troubleshooting. We'll help you triage why things aren't working.
- Code Reviews. We'll review your Pull Requests and provide constructive feedback.
- Bug Fixes. We'll rapidly work to fix any bugs in our projects.
- Build New Terraform Modules. We'll develop original modules to provision infrastructure.
- Cloud Architecture. We'll assist with your cloud strategy and design.
- Implementation. We'll provide hands-on support to implement our reference architectures.
Get access to our Open Source Community Forum on Slack. It's FREE to join for everyone! Our "SweetOps" community is where you get to talk with others who share a similar vision for how to rollout and manage infrastructure. This is the best place to talk shop, ask questions, solicit feedback, and work together as a community to build sweet infrastructure.
Please use the issue tracker to report any bugs or file feature requests.
If you are interested in being a contributor and want to get involved in developing this project or help out with our other projects, we would love to hear from you! Shoot us an email.
In general, PRs are welcome. We follow the typical "fork-and-pull" Git workflow.
- Fork the repo on GitHub
- Clone the project to your own machine
- Commit changes to your own branch
- Push your work back up to your fork
- Submit a Pull Request so that we can review your changes
NOTE: Be sure to merge the latest changes from "upstream" before making a pull request!
Copyright © 2017-2018 Cloud Posse, LLC
See LICENSE for full details.
Licensed to the Apache Software Foundation (ASF) under one
or more contributor license agreements. See the NOTICE file
distributed with this work for additional information
regarding copyright ownership. The ASF licenses this file
to you under the Apache License, Version 2.0 (the
"License"); you may not use this file except in compliance
with the License. You may obtain a copy of the License at
https://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing,
software distributed under the License is distributed on an
"AS IS" BASIS, WITHOUT WARRANTIES OR CONDITIONS OF ANY
KIND, either express or implied. See the License for the
specific language governing permissions and limitations
under the License.
All other trademarks referenced herein are the property of their respective owners.
This project is maintained and funded by Cloud Posse, LLC. Like it? Please let us know at hello@cloudposse.com
We're a DevOps Professional Services company based in Los Angeles, CA. We love Open Source Software!
We offer paid support on all of our projects.
Check out our other projects, apply for a job, or hire us to help with your cloud strategy and implementation.
 Andriy Knysh |
|---|


