Detailed description can be found in our blog post about this plugin,
you can also
Note about detection capabilities: this plugin will only supply the built-in active scanner with payloads, thus for optimal coverage vs. performance, you'll have to configure your scan properly – just as with any other built-in or extension-provided scan. See #3 for detailed explanation regarding this matter.
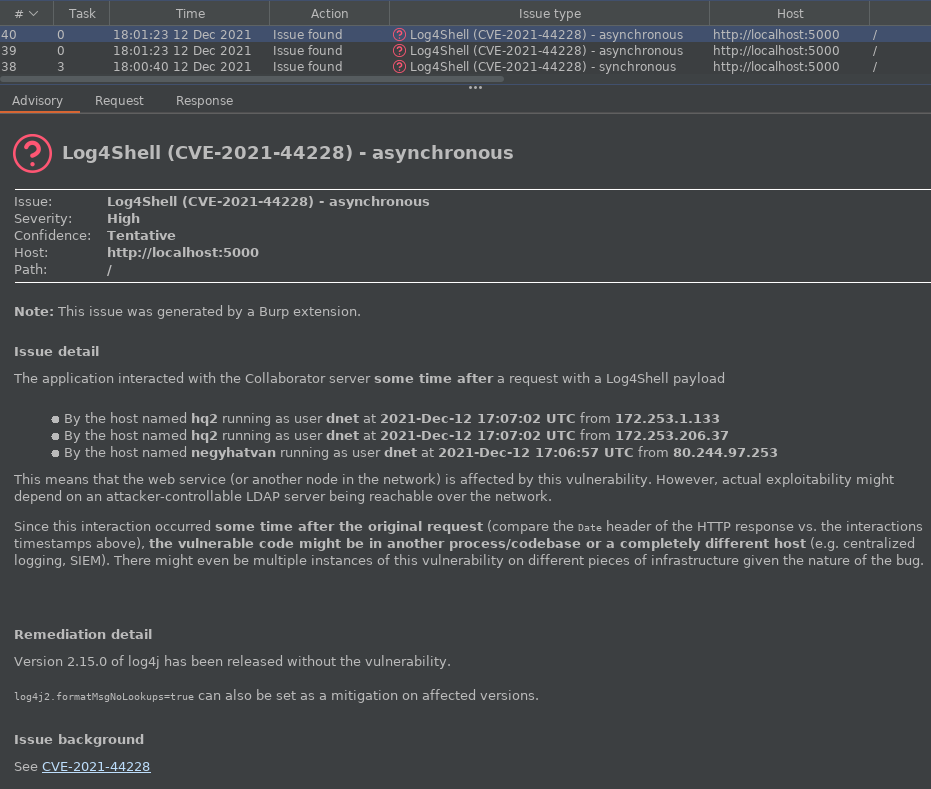
| Feature | Log4Shell scanner (this one) | ActiveScan++ (b485a07) |
|---|---|---|
| Synchronous detection | ✔️ | ✔️ |
| Asynchronous detection | ✔️ | ❌ |
| Hostname detection | ✔️ | ❌ |
| Username detection | ✔️ | ❌ |
| Ability for single-issue scan (see below) | ✔️ | ❌ |
If you'd like to scan only for Log4j (and not other things such as XSS or SQLi), this plugin makes it possible.
By following any of the instruction sets below, the scanner will only perform Log4Shell checks on all insertion points if the scan configuration created as a result is used.
Thanks to Hannah at PortSwigger for bringing this to our attention.
- When creating a new scan, click
Select from libraryon theScan configurationtab - Pick
Audit checks - extensions onlywhich is built into Burp Suite Pro 2.x - Disable every other extension (if applicable) that have an active scan check registered (such as ActiveScan++, Backslash powered scanning, Burp Bounty, etc.) so that only the Log4Shell scanner runs
This is the version that's demonstrated in the above linked video.
- Save
extensions-only.jsonto your machine - From the leftmost
Burpmenu, selectConfiguration library - Click
Importon the right side of the window - Select the location where you save the file in step 1.
- When creating a new scan, click
Select from libraryon theScan configurationtab - Disable every other extension (if applicable) that have an active scan check registered (such as ActiveScan++, Backslash powered scanning, Burp Bounty, etc.) so that only the Log4Shell scanner runs
This one used to be harder, but @alright21 made it much easier.
- Create a new
Scan Configuration - Expand
Issues Reported - Click on one of the issues to move the focus to that list
- Press
Ctrl+A - Right click on the list and click on
Enabled, this will disable all issues - Manually check the box at the last one called
Extension generated issueto enable that - Disable every other extension (if applicable) that have an active scan check registered (such as ActiveScan++, Backslash powered scanning, Burp Bounty, etc.) so that only the Log4Shell scanner runs
Execute ./gradlew build and you'll have the plugin ready in
build/libs/burp-log4shell.jar
The whole project is available under the GNU General Public License v3.0,
see LICENSE.md.