Visual Studio Code Extension for SECBIT Solidity Static Analysis Extension
This is an Visual Studio Code Extension for running SECBIT Solidity Static Analysis over Solidity source code.
Features
This extension is an user interface to the SECBIT Solidity Static Analysis Extension which extended the Solidity compiler to provide additional diagnostics on known issues and violations of best practices.
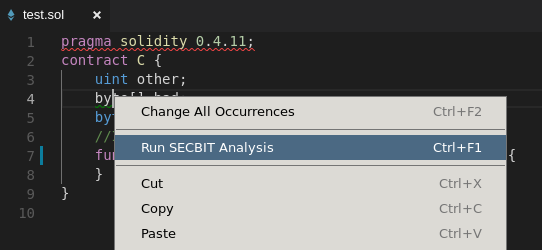
The main functionality is provided via the context menu command Run SECBIT Analysis.
Triggering this command would run the SECBIT-extended solc and report diagnostics generated.
Requirements
This extension does not provide Solidity language support. Some other extension, such as solidity-extended, should be installed for this extension to function properly.
This extension ships with a copy of the soljson.js Solidity compiler with SECBIT extensions.
So no local solc binary is required by default.
But soljson.js does not support SMT-based checks.
If they are needed, a copy of the solc Solidity compiler with SECBIT extensions built with SMT lib is required.
It would be built from source following the same instruction as building a vanilla solc.
Usage
Copy this repository to ~/.vscode/extensions and reload the IDE.
Extension Settings
This extension provides the following settings:
// Run ERC20-specific checks.
"secbit.asERC20": false,
// Only enable the checks in this list. Enable all checks when the list contains no valid entry.
"secbit.enables": [],
// Disable SMT-solver-related checks. This is set to true when using soljson.
"secbit.noSMT": false,
// Run SECBIT static analysis on file save.
"secbit.onSave": false,
// Path to the SECBIT-extended solc. Use soljson by default.
"secbit.solc": ""Currently Supported Checks
ERC20 Specific
approve-no-event
Error
erc20-mintable
Warning
Contract is mintable (The contract, or any of its base contract, contains a function with the name matching /^_?mint.*$/).
erc20-no-decimals
Error
The contract and all of its base contract do not have a decimals ABI.
This error only reports on a contract that is not a base contract of any other contract.
erc20-no-name
Error
The contract and all of its base contract do not have a name ABI.
This error only reports on a contract that is not a base contract of any other contract.
erc20-no-return
Error
SECBIT: transferFrom-no-return
erc20-no-symbol
Error
The contract and all of its base contract do not have a symbol ABI.
This error only reports on a contract that is not a base contract of any other contract.
transfer-no-event
Error
ERC20 transfer functions should emit Transfer event in some cases.
transfer-no-revert
Error
ERC20 transfer functions should revert in some cases.
transferfrom-no-allowed-check
Warning
No check on allowed within a ERC20 transferFrom() function.
approve-with-balance-verify
Warning
SECBIT: approve-with-balance-verify
short-addr
Error
The short-address attack.
Vulnerabilities
blockhash
Warning
The return value of blockhash() could be controlled by miners.
dirty-padding
Error
Be aware of "dirty higher order bits".
Solidity: security considerations
int-div
Warning
Integer division.
forced-ether
Error
Conditions on ether balance are not reliable since ether could be forced into a contract.
ConsenSys: forcibly sending ether to a contract
pull-vs-push
Error
Avoid DoS by using a pull payment system
ConsenSys: DoS with unexpected revert
private-modifier
Information
Data with private modifier is still visible.
redundant-fallback
Warning
Fallback function with a single throw is redundant.
reentrance
Error
The DAO attack.
ConsenSys: avoid state changes after external calls
This check uses SMT solver.
send-vs-transfer
Warning
Preferred transfer() over send() or call.value().
ConsenSys: Be aware of the tradeoffs between send(), transfer(), and call.value()
timestamp
Warning
timestamp could be manipulated by miners.
ConsenSys: Timestamp Dependence
tx-origin
Error
Avoid using tx.origin.
ConsenSys: avoid using tx.origin
unchecked-math
Error
Integer over/underflows.
ConsenSys: integer overflow and underflow
This check uses SMT solver.
Coding style issues
bad-name
Information
Event names should start with upper cases and function names should start with lower cases.
constant-mutability
Information
Using deprecating constant.
delegatecall
Warning
Using delegatecall.
fix-version
Information
It is recommended to use a fixed language version.
hardcode-addr
Warning
Hard-coded address in the contract.
implicit-visibility
Information
Visibility is not specified explicitly.
no-return
Information
No return statement in a function that returns value.
pure-function
Information
Could use a more strict state-mutability specification.
revert-vs-require
Information
Use require instead of revert.
suicide
Information
Using suicide.
sha3
Information
Using sha3.
throw
Information
Using throw.
type-inference
Information
Unsafe type inference.
view-immutable
Information
Could use a more strict state-mutability specification.
Gas optimization
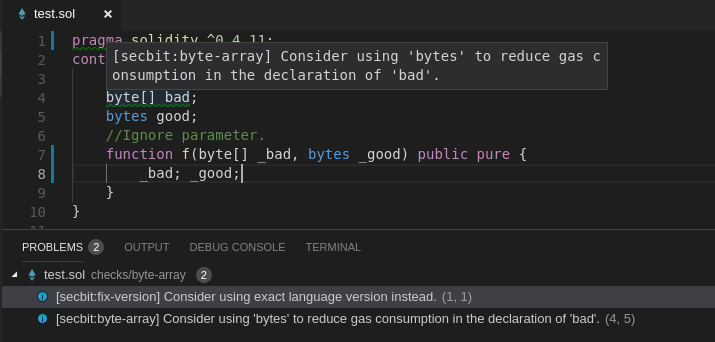
byte-array
gas
Information
Reduce gas consumption by replacing bytes with byte[] when possible.
Known Issues
Being an static analysis tool, false positives and false negatives are unavoidable. Bug reports are welcomed.
Contact Us
If you run into any issues or have suggestions for us, feel free to create issues and pull requests.
Related Projects
-
Awesome Buggy ERC20 Tokens - A Collection of Vulnerabilities in ERC20 Smart Contracts With Tokens Affected
-
adelaide - The SECBIT Static Analysis Extension to Solidity Compiler
-
Token Libraries with Proofs - Contains correctness proofs of token contracts wrt. given specifications and high-level properties
License
This extension is open-sourced under the MIT license in the LICENSE file of this repository.