Kubescape is the first tool for testing if Kubernetes is deployed securely as defined in Kubernetes Hardening Guidance by NSA and CISA
Use Kubescape to test clusters or scan single YAML files and integrate it to your processes.
curl -s https://raw.githubusercontent.com/armosec/kubescape/master/install.sh | /bin/bash
kubescape scan framework nsa --exclude-namespaces kube-system,kube-public
If you wish to scan all namespaces in your cluster, remove the --exclude-namespaces flag.
Check your YAML files before you're deploying, simply add them at the end of command line:
kubescape scan framework nsa *.yaml
Kubescape can produce output fitting for later processing:
- JSON (
-f json) - JUnit XML (
-f junit)
- Scan a running Kubernetes cluster with
nsaframework
kubescape scan framework nsa --exclude-namespaces kube-system,kube-public
- Scan local
yaml/jsonfiles
kubescape scan framework nsa examples/online-boutique/*
- Scan
yaml/jsonfiles from url
kubescape scan framework nsa https://raw.githubusercontent.com/GoogleCloudPlatform/microservices-demo/master/release/kubernetes-manifests.yaml
- Output in
jsonformat
kubescape scan framework nsa --exclude-namespaces kube-system,kube-public --format json --output results.json
- Output in
junit xmlformat
kubescape scan framework nsa --exclude-namespaces kube-system,kube-public --format junit --output results.xml
Render the helm template and pass as stdout
helm template [CHART] [flags] --generate-name --dry-run | kubescape scan framework nsa -
for example:
helm template bitnami/mysql --generate-name --dry-run | kubescape scan framework nsa -
Note: development (and the release process) is done with Go 1.16
- Clone Project
git clone git@github.com:armosec/kubescape.git kubescape && cd "$_"
- Build
go mod tidy && go build -o kubescape .
- Run
./kubescape scan framework nsa --exclude-namespaces kube-system,kube-public
- Enjoy 🤪
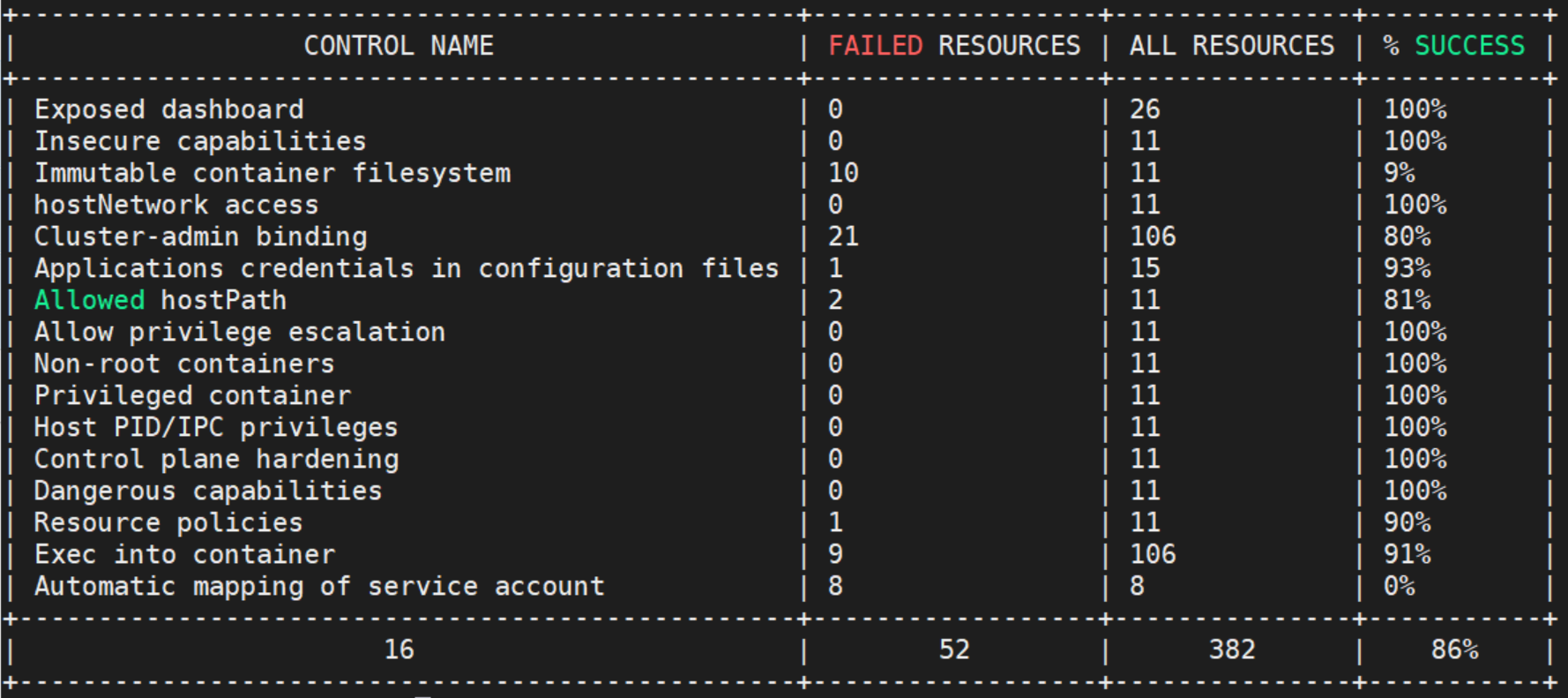
Kubescape is running the following tests according to what is defined by Kubernetes Hardening Guidance by NSA and CISA
- Non-root containers
- Immutable container filesystem
- Privileged containers
- hostPID, hostIPC privileges
- hostNetwork access
- allowedHostPaths field
- Protecting pod service account tokens
- Resource policies
- Control plane hardening
- Exposed dashboard
- Allow privilege escalation
- Applications credentials in configuration files
- Cluster-admin binding
- Exec into container
- Dangerous capabilities
- Insecure capabilities
- Linux hardening
Kubescape based on OPA engine: https://github.com/open-policy-agent/opa and ARMO's posture controls.
The tools retrieves Kubernetes objects from the API server and runs a set of regos snippets developed by ARMO.
The results by default printed in a pretty "console friendly" manner, but they can be retrieved in JSON format for further processing.
Kubescape is an open source project, we welcome your feedback and ideas for improvement. We’re also aiming to collaborate with the Kubernetes community to help make the tests themselves more robust and complete as Kubernetes develops.