Sharingan is a recon multitool for offensive security / bug bounty
This is very much a work in progress and I'm relatively new to offensive security in general so if you see something that can be improved please open an issue or PR with suggested changes.
Outside of your gopath
git clone https://github.com/leobeosab/sharingan
go get github.com/leobeosab/sharingan/cmd/sharingancli
- NMap
- Go
Order matters when it comes to flags it must be sharingancli [globalflags] command [commandflags] if this isn't a wanted feature I can change it but I like how clean it is
DNS busts the target with a wordlist you provide
sharingancli --target targetname dns --dns-wordlist ~/path/to/wordlist --root-domain target.com
Adds subdomains to the program's storage from stdin using pipes
cat subs | sharingancli --target targetname dns addsubs
Scans all hosts available that were stored in target using nmap
sharingancli --target target scan
Scan a single host from list of subdomains stored in target
sharingancli --target target scan interactive
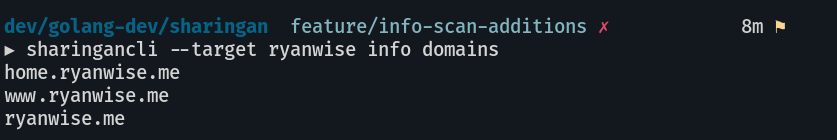
Outputs all domains as a list in stdout
sharingancli --target target info domains
- Dir brute forcing -- Currently being worked on
- JSON and regular file exports
- Automated scans through a daemon?
- add a way to do SYN / -sS scanning [ must be root so it presents a challenge ]
- Possible Web ui / html export