The landing zone module can be used to create a fully customizable VPC environment within a single region. The three following patterns are starting templates that can be used to get started quickly with Landing Zone. These patterns are located in the patterns directory.
Each of these patterns creates the following infrastructure:
- A resource group for cloud services and for each VPC.
- Cloud Object Storage instances for flow logs and Activity Tracker
- Encryption keys in either a Key Protect or Hyper Protect Crypto Services instance
- A management and workload VPC connected by a transit gateway
- A flow log collector for each VPC
- All necessary networking rules to allow communication
- Virtual Private Endpoint (VPE) for Cloud Object Storage in each VPC
- A VPN gateway in the management VPC
Each pattern creates the following infrastructure on the VPC:
- The virtual server (VSI) pattern deploys identical virtual servers across the VSI subnet tier in each VPC
- The Red Hat OpenShift Kubernetes (ROKS) pattern deploys identical clusters across the VSI subnet tier in each VPC
- The mixed pattern provisions both of these elements
For more information about the default configuration, see Default Secure Landing Zone configuration.
| Virtual server pattern | Red Hat OpenShift pattern | Mixed pattern |
|---|---|---|
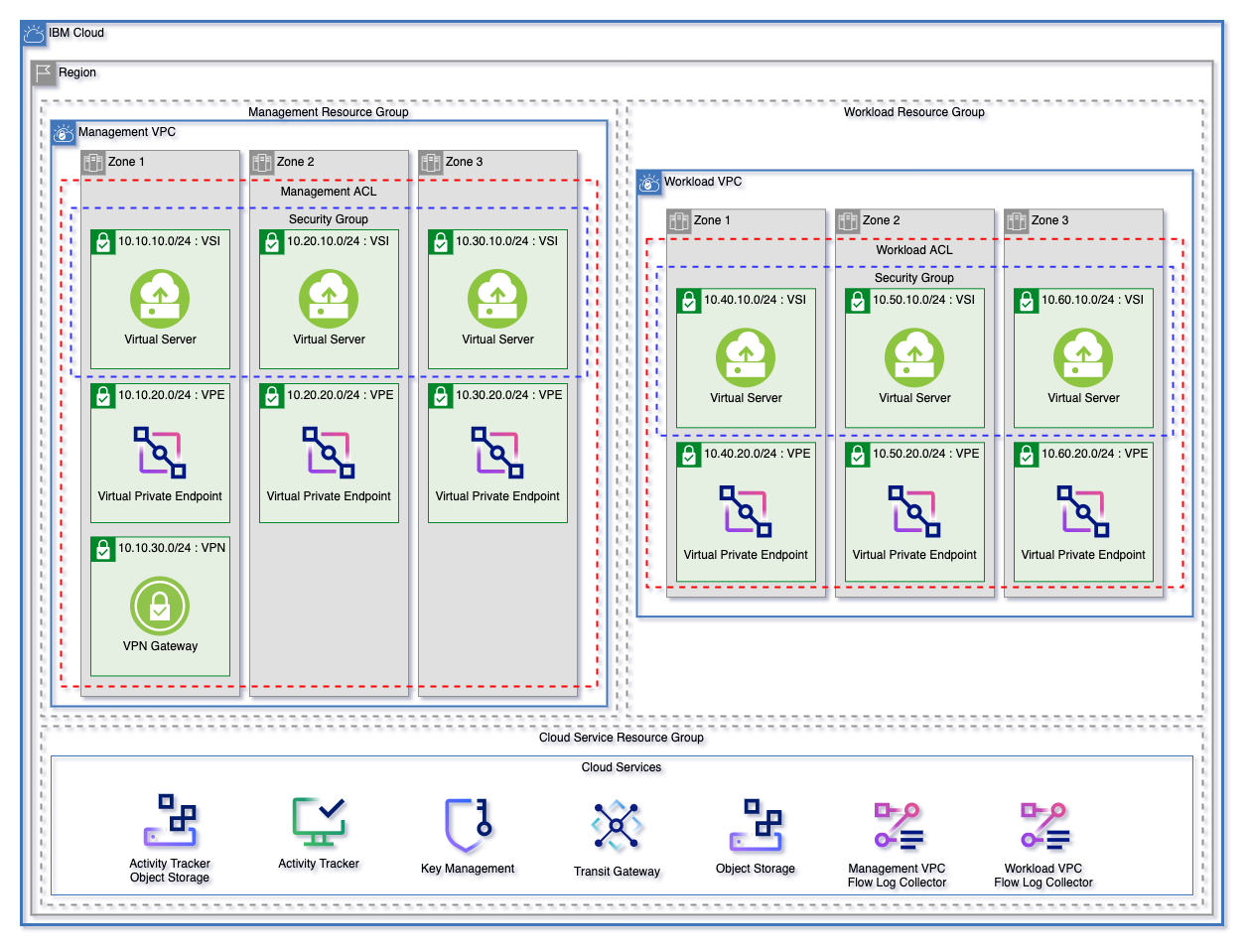 |
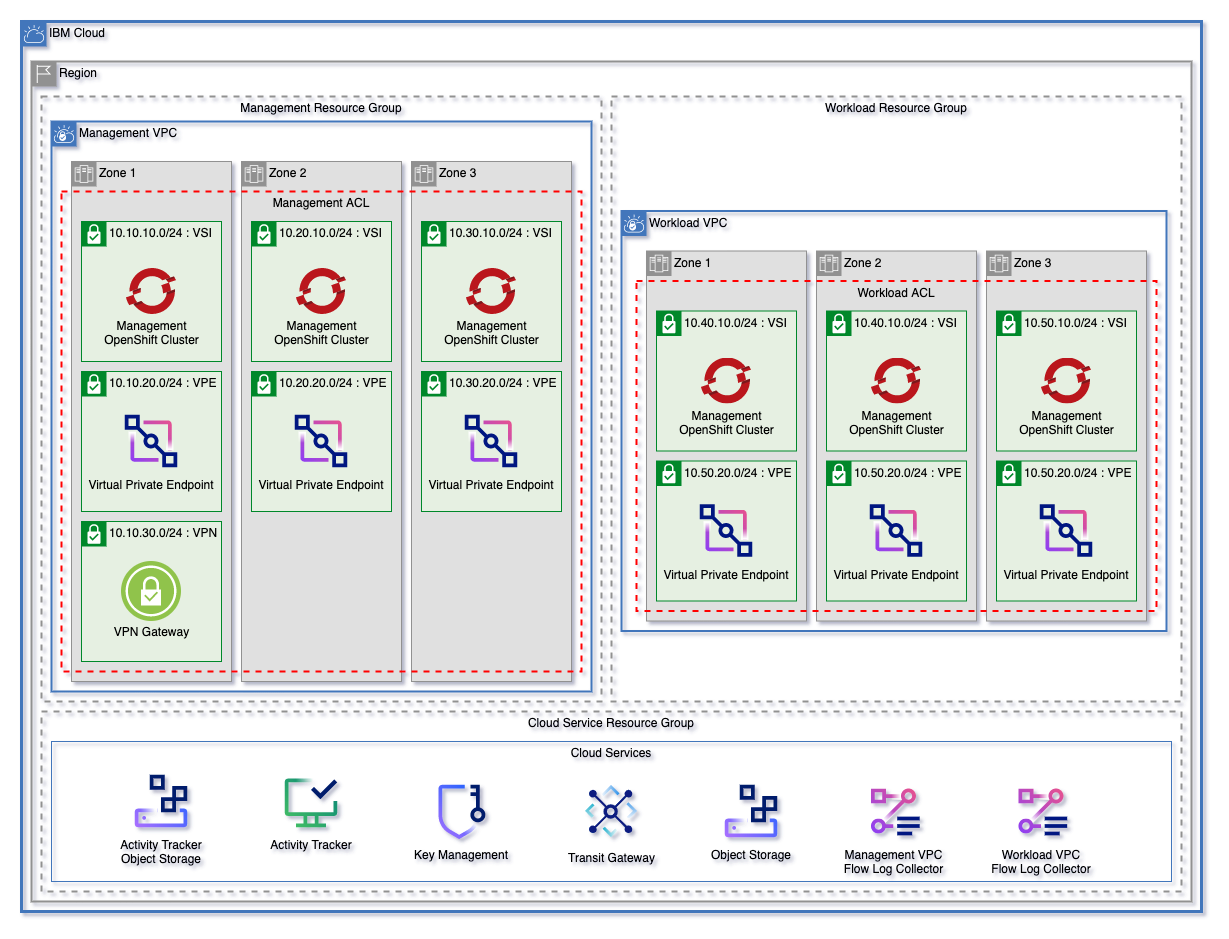 |
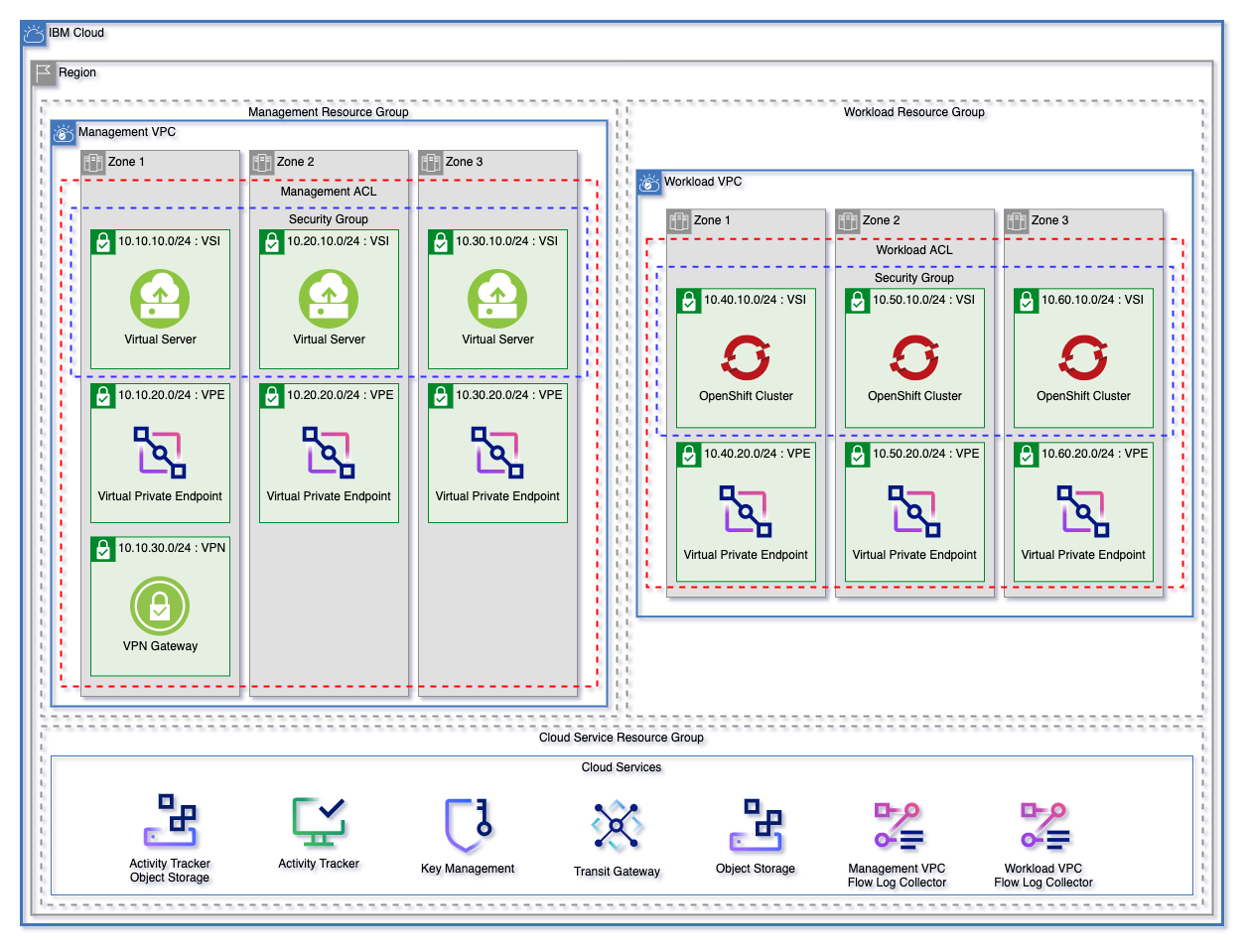 |
Complete the following steps before you deploy the Secure Landing Zone module.
-
Make sure that you have an IBM Cloud Pay-As-You-Go or Subscription account:
- If you don't have an IBM Cloud account, create one.
- If you have a Trial or Lite account, upgrade your account.
- Log in to IBM Cloud with the IBMid you used to set up the account. This IBMid user is the account owner and has full IAM access.
- Complete the company profile and contact information for the account. This profile is required to stay in compliance with IBM Cloud Financial Service profile.
- Enable the Financial Services Validated option for your account.
- Enable virtual routing and forwarding (VRF) and service endpoints by creating a support case. Follow the instructions in enabling VRF and service endpoints.
-
Create an IBM Cloud API key. The user who owns this key must have the Administrator role.
-
Require users in your account to use multifactor authentication (MFA).
-
Set up access groups. User access to IBM Cloud resources is controlled by using the access policies that are assigned to access groups. For IBM Cloud Financial Services validation, all IAM users must not be assigned direct access to any IBM Cloud resources.
Select All Identity and Access enabled services when you assign access to the group.
For Key Management services, you can use IBM Cloud Hyper Protect Crypto Services. Create an instance before you create the Secure Landing Zone.
-
Create the service instance:
- (Optional) Create a resource group for your instance.
- On the Hyper Protect Crypto Services (https://cloud.ibm.com/catalog/services/hyper-protect-crypto-services) details page, select a plan.
- Complete the required details that are required and click Create.
-
Initialize Hyper Protect Crypto Services:
To initialize the provisioned Hyper Protect Crypto Service instance, follow the steps in Getting started with IBM Cloud Hyper Protect Crypto Services.
For proof-of-technology environments, use the
auto-initflag. For more information, see Initializing service instances using recovery crypto units.
You can customize your environment with Secure Landing Zone in two ways: by using Terraform input variables or by using the override.json file.
In the first method, you set a couple of required input variables of your respective pattern, and then provision the environment.
You can find the list of input variables in the variables.tf file of the pattern directory:
Terraform supports multiple ways to set input variables. For more information, see Input Variables in the Terraform language documentation.
For example, you can add more VPCs by adding the name of the new VPC to the vpcs variable in the variables.tf file in your patterns directory.
vpcs = ["management", "workload", "<ADDITIONAL VPC>"]
You can get more specific after you use this method. Running the Terraform outputs a JSON-based file that you can use in override.json.
The second route is to use the override.json to create a fully customized environment based on the starting template. By default, each pattern's override.json is set to contain the default environment configuration. You can use the override.json in the respective pattern directory by setting the template input override variable to true. Each value in override.json corresponds directly to a variable value from this root module, which each pattern uses to create your environment.
Through the override.json, you can pass any variable or supported optional variable attributes from this root module, which each pattern uses to provision infrastructure. For a complete list of supported variables and attributes, see the variables.tf file.
After every execution of terraform apply, a JSON-encoded definition is output. This definition of your environment is based on the defaults for the Landing Zone and any variables that are changed in the override.json file. You can then use the output in the override.json file.
You can redirect the contents between the output lines by running the following commands:
config = <<EOT
EOTAfter you replace the contents of the override.json file with your configuration, you can edit the resources within. Make use that you set the template override variable to true as an input variable. For example, within the variables.tf file.
Locally run configurations do not require a Terraform apply command to generate the override.json. To view your current configuration, run the terraform refresh command.
The override.json file does not need to contain all elements. For example,
{
"enable_transit_gateway": false
}The F5 BIG-IP Virtual Edition supports setting up a client-to-site full tunnel VPN to connect to your management or edge VPC or a web application firewall (WAF). With this configuration, you can connect to your workload VPC over the public internet.
Through Secure Landing Zone, you can optionally provision the F5 BIG-IP so that you can set up the implemented solution of a client-to-site VPN or web application firewall (WAF). For more information, see Provisioning a F5 BIG-IP host by using Secure Landing Zone.
With Teleport, you can configure a virtual server instance in a VPC as a bastion host. Some of Teleport features include single sign-on to access the SSH server, auditing, and recording of your interactive sessions. For more information about Teleport, see the Teleport documentation.
Secure Landing Zone can set up a bastion host that uses Teleport. For more information, see Provisioning a bastion host by using Teleport with Secure Landing Zone.
| Feature | Description | Module | Version |
|---|---|---|---|
| Logging and Monitoring | Configure logging or monitoring for an existing Red Hat OpenShift cluster | slzone/terraform-logmon-module | v1.0.0 |
This template supports creating any number of VPCs in a single region. The VPC network and components are created by the Secure Landing Zone VPC module. The VPC components are described in the main.tf file.
The list of VPCs from the vpcs variable is converted to a map, which supports adding and deleting resources without the need for an update. The VPC network includes the following aspects:
- VPC
- Subnets
- Network ACLs
- Public gateways
- VPN gateway and gateway connections
The following example shows the vpc variable type.
type = list(
object({
prefix = string # A unique prefix that will prepend all components in the VPC
resource_group = optional(string) # Name of the resource group to use for VPC. Must by in `var.resource_groups`
use_manual_address_prefixes = optional(bool) # Optionally assign prefixes to VPC manually. By default this is false, and prefixes will be created along with subnets
classic_access = optional(bool) # Optionally allow VPC to access classic infrastructure network
default_network_acl_name = optional(string) # Override default ACL name
default_security_group_name = optional(string) # Override default VPC security group name
default_routing_table_name = optional(string) # Override default VPC routing table name
flow_logs_bucket_name = optional(string) # Name of COS bucket to use with flowlogs. Must be created by this template
##############################################################################
# Use `address_prefixes` only if `use_manual_address_prefixes` is true
# otherwise prefixes will not be created. Use only if you need to manage
# prefixes manually.
##############################################################################
address_prefixes = optional(
object({
zone-1 = optional(list(string))
zone-2 = optional(list(string))
zone-3 = optional(list(string))
})
)
##############################################################################
##############################################################################
# List of network ACLs to create with VPC
##############################################################################
network_acls = list(
object({
name = string # Name of ACL, this can be referenced by subnets to be connected on creation
add_cluster_rules = optional(bool) # Automatically add to ACL rules needed to allow cluster provisioning from private service endpoints
##############################################################################
# List of rules to add to the ACL, by default all inbound and outbound traffic
# will be allowed. By default, ACLs have a limit of 50 rules.
##############################################################################
rules = list(
object({
name = string # Name of ACL rule
action = string # Allow or deny traffic
direction = string # Inbound or outbound
destination = string # Destination CIDR block
source = string # Source CIDR block
##############################################################################
# Optionally the rule can be created for TCP, UDP, or ICMP traffic.
# Only ONE of the following blocks can be used in a single ACL rule
##############################################################################
tcp = optional(
object({
port_max = optional(number)
port_min = optional(number)
source_port_max = optional(number)
source_port_min = optional(number)
})
)
udp = optional(
object({
port_max = optional(number)
port_min = optional(number)
source_port_max = optional(number)
source_port_min = optional(number)
})
)
icmp = optional(
object({
type = optional(number)
code = optional(number)
})
)
})
##############################################################################
)
})
)
##############################################################################
##############################################################################
# Public Gateways
# For each `zone` that is set to `true`, a public gateway will be created in
# That zone
##############################################################################
use_public_gateways = object({
zone-1 = optional(bool)
zone-2 = optional(bool)
zone-3 = optional(bool)
})
##############################################################################
##############################################################################
# Object for subnets to be created in each zone, each zone can have any number
# of subnets
#
# Each subnet accepts the four following arguments:
# * name - Name of the subnet
# * cidr - CIDR block for the subnet
# * public_gateway - Optionally add a public gateway. This works only if the zone
# for `use_public_gateway` is set to `true`
# * acl_name - Name of ACL to be attached. Name must be found in
# `network_acl` object
##############################################################################
subnets = object({
zone-1 = list(object({
name = string
cidr = string
public_gateway = optional(bool)
acl_name = string
}))
zone-2 = list(object({
name = string
cidr = string
public_gateway = optional(bool)
acl_name = string
}))
zone-3 = list(object({
name = string
cidr = string
public_gateway = optional(bool)
acl_name = string
}))
})
##############################################################################
})
)
##############################################################################You can add flow log collectors to a VPC by adding the flow_logs_bucket_name parameter to the vpc object. You declare each bucket in the cos variable that manages Cloud Object Storage. For more information about provisioning Cloud Object Storage with this template, see the Cloud Object Storage section.
You can create a transit gateway that connects any number of VPCs in the same network by setting the enable_transit_gateway variable to true. A connection is created for each VPC that you specify in the transit_gateway_connections variable. You configure the transit gateway resource in the transit_gateway.tf file.
You can provision multiple security groups within any of the provisioned VPCs. You configure security group components in the security_groups.tf file.
The security_group variable supports creating security groups dynamically. The list of groups is converted to a map to ensure that changes, updates, and deletions don't affect other resources.
The following example shows the security_group variable type.
list(
object({
name = string # Name for each security group
vpc_name = string # The group will be created. Only VPCs from `var.vpc` can be used
##############################################################################
# List of rules to be added to the security group
##############################################################################
rules = list(
object({
name = string # Name of the rule
direction = string # Inbound or outbound
source = string # Source CIDR to allow
##############################################################################
# Optionally, security groups can allow ONE of the following blocks
# additional rules will have to be created for different types of traffic
##############################################################################
tcp = optional(
object({
port_max = number
port_min = number
})
)
udp = optional(
object({
port_max = number
port_min = number
})
)
icmp = optional(
object({
type = number
code = number
})
)
})
##############################################################################
)
##############################################################################
})
)This module uses the Cloud Schematics VSI Module to support multiple VSI workloads. The VSI submodule covers the following resources:
- Virtual server instances
- Block storage for those instances
- VPC load balancers for those instances
Virtual server components can be found in virtual_servers.tf
You can use this template to create or return multiple VPC SSH keys by using the ssh_keys variable. For more information about how to locate an SSH key or create one, see SSH keys in the IBM Cloud docs.
Users can add a name and optionally a public key. If public_key is not provided, the SSH key is retrieved by using a data block
type = list(
object({
name = string
public_key = optional(string)
resource_group = optional(string) # Must be in var.resource_groups
})
)The following example shows the vsi virtual server variable type.
list(
object({
name = string # Name to be used for each VSI created
vpc_name = string # Name of VPC from `vpcs` variable
subnet_names = list(string) # Names of subnets where VSI will be provisioned
ssh_keys = list(string) # List of SSH Keys from `var.ssh_keys` to use when provisioning.
image_name = string # Name of the image for VSI, use `ibmcloud is images` to view
machine_type = string # Name of machine type. Use `ibmcloud is in-prs` to view
vsi_per_subnet = number # Number of identical VSI to be created on each subnet
user_data = optional(string) # User data to initialize instance
resource_group = optional(string) # Name of resource group where VSI will be provisioned, must be in `var.resource_groups`
security_groups = optional(list(string)) # Optional Name of additional security groups from `var.security groups` to add to VSI
##############################################################################
# When creating VSI, users can optionally create a new security group for
# those instances. These fields function the same as in `var.security_groups`
##############################################################################
security_group = optional(
object({
name = string
rules = list(
object({
name = string
direction = string
source = string
tcp = optional(
object({
port_max = number
port_min = number
})
)
udp = optional(
object({
port_max = number
port_min = number
})
)
icmp = optional(
object({
type = number
code = number
})
)
})
)
})
)
##############################################################################
##############################################################################
# Optionally block storage volumes can be created. A volume from this list
# will be created and attached to each VSI
##############################################################################
block_storage_volumes = optional(list(
object({
name = string # Volume name
profile = string # Profile
capacity = optional(number) # Capacity
iops = optional(number) # IOPs
encryption_key = optional(string) # Optionally provide kms key
})
))
##############################################################################
##############################################################################
# Any number of VPC Load Balancers
##############################################################################
load_balancers = list(
object({
name = string # Name of the load balancer
type = string # Can be public or private
listener_port = number # Port for front end listener
listener_protocol = string # Protocol for listener. Can be `tcp`, `http`, or `https`
connection_limit = number # Connection limit
algorithm = string # Back end Pool algorithm can only be `round_robin`, `weighted_round_robin`, or `least_connections`.
protocol = string # Back End Pool Protocol can only be `http`, `https`, or `tcp`
health_delay = number # Health delay for back end pool
health_retries = number # Health retries for back end pool
health_timeout = number # Health timeout for back end pool
health_type = string # Load Balancer Pool Health Check Type can only be `http`, `https`, or `tcp`.
pool_member_port = string # Listener port
##############################################################################
# A security group can optionally be created and attached to each load
# balancer
##############################################################################
security_group = optional(
object({
name = string
rules = list(
object({
name = string
direction = string
source = string
tcp = optional(
object({
port_max = number
port_min = number
})
)
udp = optional(
object({
port_max = number
port_min = number
})
)
icmp = optional(
object({
type = number
code = number
})
)
})
)
})
)
##############################################################################
})
)
##############################################################################
})
)You can provision a bastion host that uses Teleport. App ID is used to authenticate users to Teleport. Teleport session recordings are stored in a Cloud Object Storage bucket. You configure the bastion host components in the bastion_host.tf file.
To use the bastion host, either create an App ID instance or use an existing one. If the use_data variable is set to true, an existing App ID instance is used. Set the variable to false create an App ID instance.
object(
{
name = optional(string) # Name of existing or to be created APP ID instance
resource_group = optional(string) # The resource group of the existing or to be created APP ID instance
use_data = optional(bool) # Bool specifying to use existing or to be created APP ID instance
keys = optional(list(string)) # List of App ID resource keys
use_appid = bool # Bool specifying to connect App ID to bastion host or not
}
)
The teleport_config block creates a single template for all teleport instances. By using a single template, the values remain hidden.
object(
{
teleport_license = optional(string) # The PEM license file
https_cert = optional(string) # The https certificate used by bastion host for teleport
https_key = optional(string) # The https private key used by bastion host for teleport
domain = optional(string) # The domain of the bastion host
cos_bucket_name = optional(string) # Name of the COS bucket to store the session recordings
cos_key_name = optional(string) # Name of the COS instance resource key. Must be HMAC credentials
teleport_version = optional(string) # Version of Teleport Enterprise to use
message_of_the_day = optional(string) # Banner message the is exposed to the user at authentication time
hostname = optional(string) # The hostname of the bastion host
app_id_key_name = optional(string) # Name of APP ID key
##############################################################################
# A list of maps that contain the user email and the role you want to
# associate with them
##############################################################################
claims_to_roles = optional(
list(
object({
email = string
roles = list(string)
})
)
)
}
)The following example shows the teleport_vsi variable type.
list(
object(
{
name = string # Name to be used for each teleport VSI created
vpc_name = string # Name of VPC from `vpcs` variable
resource_group = optional(string) # Name of resource group where the teleport VSI will be provisioned, must be in `var.resource_groups`
subnet_name = string # Name of the subnet where the teleport VSI will be provisioned
ssh_keys = list(string) # List of SSH Keys from `var.ssh_keys` to use when provisioning.
boot_volume_encryption_key_name = string # Name of boot_volume_encryption_key
image_name = string # Name of the image for the teleport VSI, use `ibmcloud is images` to view
machine_type = string # Name of machine type. Use `ibmcloud is in-prs` to view
##############################################################################
# When creating VSI, users can optionally create a new security group for
# those instances. These fields function the same as in `var.security_groups`
##############################################################################
security_groups = optional(list(string))
security_group = optional(
object({
name = string
rules = list(
object({
name = string
direction = string
source = string
tcp = optional(
object({
port_max = number
port_min = number
})
)
udp = optional(
object({
port_max = number
port_min = number
})
)
icmp = optional(
object({
type = number
code = number
})
)
})
)
})
)
##############################################################################
}
)
)You can create as many iks or openshift clusters and worker pools on VPC. For ROKS clusters, make sure to enable public gateways to allow your cluster to correctly provision ingress application load balancers.
The following example shows the cluster variable type.
list(
object({
name = string # Name of Cluster
vpc_name = string # Name of VPC
subnet_names = list(string) # List of vpc subnets for cluster
workers_per_subnet = number # Worker nodes per subnet.
machine_type = string # Worker node flavor
kube_type = string # iks or openshift
kube_version = optional(string) # Can be a version from `ibmcloud ks versions` or `default`. `null` will use the
update_all_workers = optional(bool) # if true, force all workers to update
entitlement = optional(string) # entitlement option for openshift
pod_subnet = optional(string) # Portable subnet for pods
service_subnet = optional(string) # Portable subnet for services
resource_group = string # Resource Group used for cluster
cos_name = optional(string) # Name of COS instance Required only for OpenShift clusters
kms_config = optional(
object({
crk_name = string # Name of key
private_endpoint = optional(bool) # Private endpoint
})
)
worker_pools = optional(
list(
object({
name = string # Worker pool name
vpc_name = string # VPC name
workers_per_subnet = number # Worker nodes per subnet
flavor = string # Worker node flavor
subnet_names = list(string) # List of vpc subnets for worker pool
entitlement = optional(string) # entitlement option for openshift
})
)
)
})
)Virtual private endpoints can be created for any number of services. Virtual private endpoint components are defined in the vpe.tf file.
You can configure the following IBM Cloud services from this module.
This module can provision a Cloud Object Storage instance or retrieve an existing one, and then create any number of buckets within the instance.
You define Cloud Object Storage components in the cos.tf file.
You create credentials from the patterns by using an IBM Cloud API key for the scc.tf file to create a scope. You define the components, account_settings, collector, and scope for IBM Cloud Security and Compliance Center in the scc.tf file. You configure credentials in a main.tf file in the patterns directory.
The location_id variable represents the geographic area where Posture Management requests are handled and processed. When is_public is set to true, the collector connects to resources in your account over a public network. When set to false, the collector connects to resources by using a private IP address that is accessible only through IBM Cloud Private network. The collector_passphrase is necessary only if credential passphrase is enabled.
object(
{
enable_scc = bool
location_id = optional(string)
is_public = optional(bool)
collector_passphrase = optional(string)
collector_description = optional(string)
credential_id = optional(string)
scope_name = optional(string)
scope_description = optional(string)
}
)You can create multiple VPC placement groups in the vpc_placement_groups.tf file. For more information about VPC placement groups, see About placement groups in the IBM Cloud Docs.
You can use the modular design of this module to provision architectures for VSI, clusters, or a combination of both. Include a provider block and a copy of the variables.tf file. By referencing this template as a module, you support users who want to add clusters or a vsi by adding the relevant variable block.
module "vsi_pattern" {
# Replace "main" with a GIT release version to lock into a specific release
source = "git::https://github.com/terraform-ibm-modules/terraform-ibm-landing-zone.git?ref=main"
prefix = var.prefix
region = var.region
tags = var.tags
resource_groups = var.resource_groups
vpcs = var.vpcs
flow_logs = var.flow_logs
enable_transit_gateway = var.enable_transit_gateway
transit_gateway_resource_group = var.transit_gateway_resource_group
transit_gateway_connections = var.transit_gateway_connections
ssh_keys = var.ssh_keys
vsi = var.vsi
security_groups = var.security_groups
virtual_private_endpoints = var.virtual_private_endpoints
cos = var.cos
service_endpoints = var.service_endpoints
key_protect = var.key_protect
atracker = var.atracker
}module "cluster_vsi_pattern" {
# Replace "main" with a GIT release version to lock into a specific release
source = "git::https://github.com/terraform-ibm-modules/terraform-ibm-landing-zone.git?ref=main"
prefix = var.prefix
region = var.region
tags = var.tags
resource_groups = var.resource_groups
vpcs = var.vpcs
flow_logs = var.flow_logs
enable_transit_gateway = var.enable_transit_gateway
transit_gateway_resource_group = var.transit_gateway_resource_group
transit_gateway_connections = var.transit_gateway_connections
ssh_keys = var.ssh_keys
vsi = var.vsi
security_groups = var.security_groups
virtual_private_endpoints = var.virtual_private_endpoints
cos = var.cos
service_endpoints = var.service_endpoints
key_protect = var.key_protect
atracker = var.atracker
clusters = var.clusters
wait_till = var.wait_till
}module "cluster_pattern" {
# Replace "main" with a GIT release version to lock into a specific release
source = "git::https://github.com/terraform-ibm-modules/terraform-ibm-landing-zone.git?ref=main"
prefix = var.prefix
region = var.region
tags = var.tags
resource_groups = var.resource_groups
vpcs = var.vpcs
flow_logs = var.flow_logs
enable_transit_gateway = var.enable_transit_gateway
transit_gateway_resource_group = var.transit_gateway_resource_group
transit_gateway_connections = var.transit_gateway_connections
ssh_keys = var.ssh_keys
security_groups = var.security_groups
virtual_private_endpoints = var.virtual_private_endpoints
cos = var.cos
service_endpoints = var.service_endpoints
key_protect = var.key_protect
atracker = var.atracker
clusters = var.clusters
wait_till = var.wait_till
}| Name | Version |
|---|---|
| terraform | >= 1.0.0 |
| ibm | >= 1.45.0 |
| random | >= 3.4.2 |
| Name | Source | Version |
|---|---|---|
| bastion_host | git::https://github.com/terraform-ibm-modules/terraform-ibm-landing-zone-vsi.git | v1.1.5 |
| dynamic_values | ./dynamic_values | n/a |
| f5_vsi | git::https://github.com/terraform-ibm-modules/terraform-ibm-landing-zone-vsi.git | v1.1.5 |
| key_management | ./kms | n/a |
| placement_group_map | ./dynamic_values/config_modules/list_to_map | n/a |
| ssh_keys | ./ssh_key | n/a |
| teleport_config | ./teleport_config | n/a |
| vpc | git::https://github.com/terraform-ibm-modules/terraform-ibm-landing-zone-vpc.git | v2.3.3 |
| vsi | git::https://github.com/terraform-ibm-modules/terraform-ibm-landing-zone-vsi.git | v1.1.5 |
| Name | Description | Type | Default | Required |
|---|---|---|---|---|
| access_groups | A list of access groups to create | list( |
[] |
no |
| add_kms_block_storage_s2s | add kms to block storage s2s authorization | bool |
true |
no |
| appid | The App ID instance to be used for the teleport vsi deployments | object({ |
{ |
no |
| atracker | atracker variables | object({ |
n/a | yes |
| clusters | A list describing clusters workloads to create | list( |
n/a | yes |
| cos | Object describing the cloud object storage instance, buckets, and keys. Set use_data to false to create instance |
list( |
n/a | yes |
| enable_transit_gateway | Create transit gateway | bool |
true |
no |
| f5_template_data | Data for all f5 templates | object({ |
{ |
no |
| f5_vsi | A list describing F5 VSI workloads to create | list( |
[] |
no |
| iam_account_settings | IAM Account Settings. | object({ |
{ |
no |
| key_management | Key Protect instance variables | object({ |
n/a | yes |
| network_cidr | Network CIDR for the VPC. This is used to manage network ACL rules for cluster provisioning. | string |
"10.0.0.0/8" |
no |
| prefix | A unique identifier for resources. Must begin with a letter and end with a letter or number. This prefix will be prepended to any resources provisioned by this template. Prefixes must be 16 or fewer characters. | string |
n/a | yes |
| region | Region where VPC will be created. To find your VPC region, use ibmcloud is regions command to find available regions. |
string |
n/a | yes |
| resource_groups | Object describing resource groups to create or reference | list( |
n/a | yes |
| secrets_manager | Map describing an optional secrets manager deployment | object({ |
{ |
no |
| security_compliance_center | Security and Compliance Center Variables | object({ |
{ |
no |
| security_groups | Security groups for VPC | list( |
[] |
no |
| service_endpoints | Service endpoints. Can be public, private, or public-and-private |
string |
"private" |
no |
| ssh_keys | SSH keys to use to provision a VSI. Must be an RSA key with a key size of either 2048 bits or 4096 bits (recommended). If public_key is not provided, the named key will be looked up from data. If a resource group name is added, it must be included in var.resource_groups. See https://cloud.ibm.com/docs/vpc?topic=vpc-ssh-keys. |
list( |
n/a | yes |
| tags | List of tags to apply to resources created by this module. | list(string) |
[] |
no |
| teleport_config_data | Teleport config data. This is used to create a single template for all teleport instances to use. Creating a single template allows for values to remain sensitive | object({ |
null |
no |
| teleport_vsi | A list of teleport vsi deployments | list( |
[] |
no |
| transit_gateway_connections | Transit gateway vpc connections. Will only be used if transit gateway is enabled. | list(string) |
n/a | yes |
| transit_gateway_resource_group | Name of resource group to use for transit gateway. Must be included in var.resource_group |
string |
n/a | yes |
| virtual_private_endpoints | Object describing VPE to be created | list( |
n/a | yes |
| vpc_placement_groups | List of VPC placement groups to create | list( |
[] |
no |
| vpcs | A map describing VPCs to be created in this repo. | list( |
n/a | yes |
| vpn_gateways | List of VPN Gateways to create. | list( |
n/a | yes |
| vsi | A list describing VSI workloads to create | list( |
n/a | yes |
| wait_till | To avoid long wait times when you run your Terraform code, you can specify the stage when you want Terraform to mark the cluster resource creation as completed. Depending on what stage you choose, the cluster creation might not be fully completed and continues to run in the background. However, your Terraform code can continue to run without waiting for the cluster to be fully created. Supported args are MasterNodeReady, OneWorkerNodeReady, and IngressReady |
string |
"IngressReady" |
no |
| Name | Description |
|---|---|
| appid_key_names | List of appid key names created |
| appid_name | Name of the appid instance used. |
| appid_redirect_urls | List of appid redirect urls |
| atracker_route_name | Name of atracker route |
| atracker_target_name | Name of atracker target |
| bastion_host_names | List of bastion host names |
| cluster_names | List of create cluster names |
| cos_bucket_names | List of names for COS buckets creaed |
| cos_key_names | List of names for created COS keys |
| cos_names | List of Cloud Object Storage instance names |
| f5_host_names | List of bastion host names |
| fip_vsi_data | A list of VSI with name, id, zone, and primary ipv4 address, VPC Name, and floating IP. This list only contains instances with a floating IP attached. |
| resource_group_names | List of resource groups names used within landing zone. |
| secrets_manager_name | Name of secrets manager instance |
| security_group_names | List of security group names |
| service_authorization_names | List of service authorization names |
| ssh_key_names | List of SSH key names |
| subnet_names | List of Subnet names created |
| transit_gateway_name | Name of created transit gateway |
| vpc_names | List of VPC names |
| vpe_gateway_names | VPE gateway names |
| vpn_names | List of VPN names |
| vsi_data | A list of VSI with name, id, zone, and primary ipv4 address, VPC Name, and floating IP. |
| vsi_names | List of VSI names |
You can report issues and request features for this module in GitHub issues in the module repo. See Report an issue or request a feature.
To set up your local development environment, see Local development setup in the project documentation.
-brightgreen?style=plastic)




