This project is motivated by the need of an easy setup for a DSLR-timelaps using existing tools.
I'm using Tailscale (because of it's incredible easy setup) to keep the communication secure.
Of course you set up laps without a vpn in place, but it is not recommended cause:
- vpn adds an additional layer of security around all networking (including the setup via ansible)
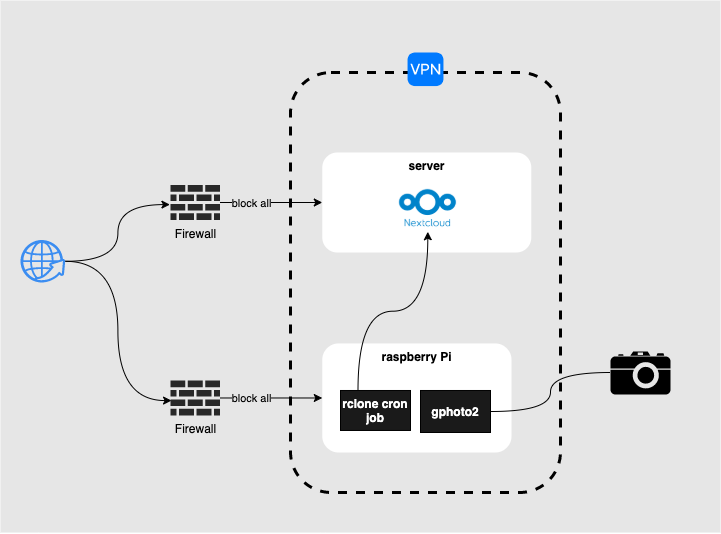
The architecture is composed of:
-
a client (in my case a raspberryPi)
- running a tailscale client
- with a connected DSLR camera
- running gphoto2 for DSLR remote control
- running an rclone cron job: uploading the photos to my nextcloud (via webDAV)
-
a server (in my case hosted on hetzner.de)
- hosting a nextcloud instance (not part of this repository)
As mentioned above I rely on an already set up network connection via Tailscale VPN.
As a prerequisite you need:
installed on your local machine.
The central place of configuration lives in ansible/inventory.yml. This file is the single source of thruth and all other files are populated with values from ansible/inventory.yml during provisioning.
The only mandatory configuration you have to make is the client's and server's IP adress for ansible to connect to:
all:
hosts:
children:
client:
hosts:
100.95.134.119: # client's IP address (within the tailscale vpn)For the rclone role the server-credentials are expected in a [gitignored] text file:
./secrets
LAPS_RCLONE_URL="https://your-nextcloud-server/remote.php/dav/files/<user>/"
LAPS_RCLONE_USER="user"
LAPS_RCLONE_PASS="base64 encoded password"
To provision the client run:
task clientFor monitoring the client, I use prometheus installing node_exporter with some custom extensions (e.g. monitoring the number of pictures on the device):
task metrics- (use ansible instead of scripts)
- (introduce lockfile for rclone cron job, preventing parallel upload processes)
SSH setup
ssh-keygen -f ./client.key -t ecdsa -b 521
ssh-copy-id -i ./client.key user@host
mv client.key ansible/Tailscale Installation
sudo apt-get install apt-transport-https
curl -fsSL https://pkgs.tailscale.com/stable/raspbian/buster.gpg | sudo apt-key add -
curl -fsSL https://pkgs.tailscale.com/stable/raspbian/buster.list | sudo tee /etc/apt/sources.list.d/tailscale.list
sudo apt-get update
sudo apt-get install tailscale
sudo tailscale upTailscale Logging
For practical reasons I completely turned off the tailscale logs in the service:
# /usr/lib/systemd/system/tailscaled.service
[Service]
StandardOutput=null
StandardError=null