Protects your data by inspecting incoming queries from your application server and rejecting abnormal ones.
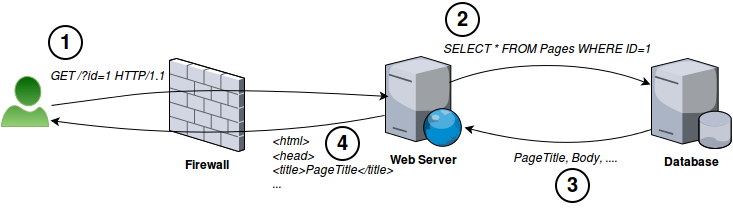
For example, this is how web server normally interacts with database server:
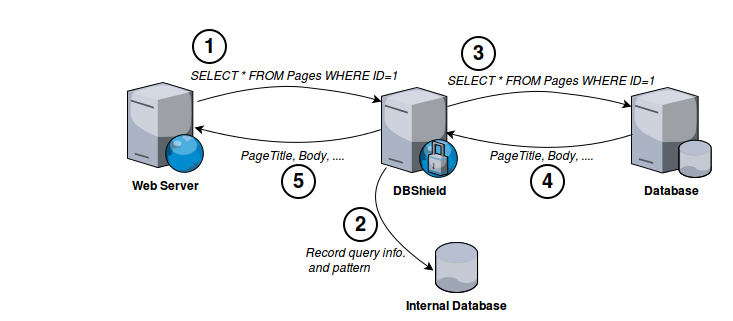
By adding DBShield in front of database server we can protect it against abnormal queries. To detect abnormal queries we first run DBShield in learning mode. Learning mode lets any query pass but it records information about it (pattern, username, time and source) into internal database.
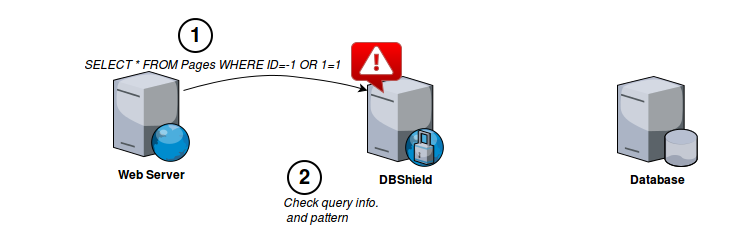
After collecting enough patterns we can run DBShield in protect mode. Protect mode can distinguish abnormal query patterns, user and source and take action based on configurations.
Sample Output:
$ go run main.go
2016/10/15 16:25:31 [INFO] Config file: /etc/dbshield.yml
2016/10/15 16:25:31 [INFO] Internal DB: /tmp/model/127.0.0.1_postgres.db
2016/10/15 16:25:31 [INFO] Listening: 0.0.0.0:5000 (Threads: 5)
2016/10/15 16:25:31 [INFO] Backend: postgres (127.0.0.1:5432)
2016/10/15 16:25:31 [INFO] Protect: true
2016/10/15 16:25:33 [INFO] Connected from: 127.0.0.1:35910
2016/10/15 16:25:33 [INFO] Connected to: 127.0.0.1:5432
2016/10/15 16:25:33 [INFO] SSL connection
2016/10/15 16:25:34 [DEBUG] Client handshake done
2016/10/15 16:25:34 [DEBUG] Server handshake done
2016/10/15 16:25:34 [INFO] User: postgres
2016/10/15 16:25:34 [INFO] Database: test
2016/10/15 16:25:34 [INFO] Query: SELECT * FROM stocks where id=-1 or 1=1
2016/10/15 16:25:34 [WARN] Pattern not found: [53 55 51 52 55 52 50 53 55 51 53 49 115 116 111 99 107 115 53 55 51 53 50 105 100 54 49 52 53 53 55 51 55 57 53 55 52 48 52 53 55 51 55 57 54 49 53 55 51 55 57] (SELECT * FROM stocks where id=-1 or 1=1)
2016/10/15 16:25:34 [WARN] Dropping connection
$ go get -u github.com/nim4/DBShield
then you can execute it like:
$ $GOPATH/bin/DBShield -c $GOPATH/src/github.com/nim4/DBShield/conf/dbshield.yml
| Database | Protect | SSL |
|---|---|---|
| MariaDB |  |
 |
| MySQL |  |
 |
| Oracle |  |
 |
| Postgres |  |
 |
- Add Microsoft SQL Server
- Add more command-line arguments
- Improve documentation