mainRecon for bugbounty hunter is an image with a bash script with some of the tools used at recon workflow.
- Table of Contents
- About mainRecon
- Features
- Flow
- mainRecon.sh
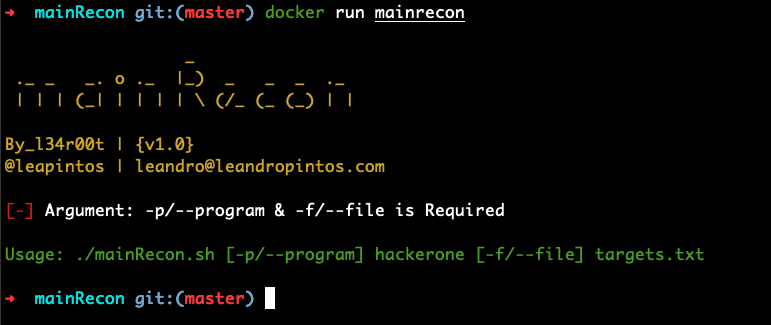
- Usage
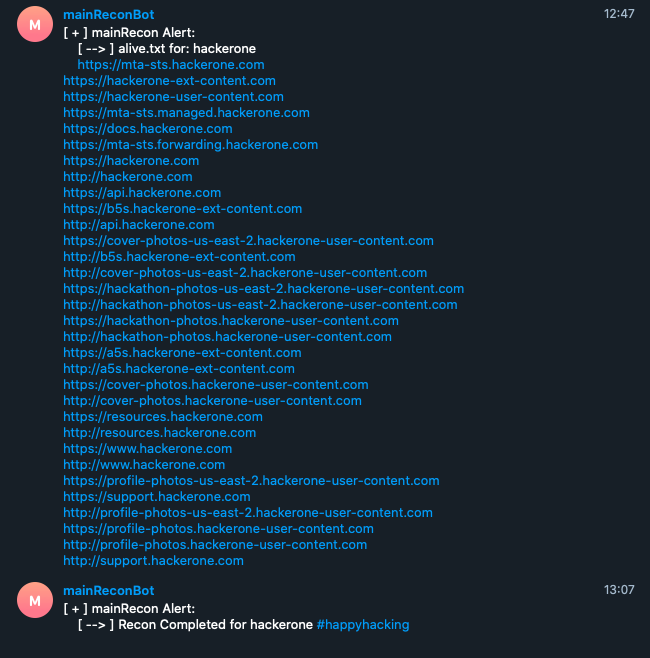
- mainRecon scan results
- Environment tested
- Coffee Time
- Contributing
- Stargazers over time
- Credits
- Disclaimer
- License
mainRecon is an automated reconnaissance docker image for bug bounty hunter write in bash script. This image has the basic tools used in the recon workflow. The purpose is to simplify the recon workflow in a simple way.
You can run the docker image in your PC o VPS.
- Subdomain Enumeration
- Checks alive subdomain
- Finds URLs at Wayback Machine
- Screenshots of the subdomains
- Headers responses files
- Finds js files
- Search tokes in js files
- Search endpoints in js files
- Finds parameters
- Finds directories
- Telegram notifications
| Name | Repository |
|---|---|
| findomain | https://github.com/Edu4rdSHL/findomain |
| assetfinder | https://github.com/tomnomnom/assetfinder |
| Amass | https://github.com/OWASP/Amass |
| subfinder | https://github.com/projectdiscovery/subfinder |
| httprobe | https://github.com/tomnomnom/httprobe |
| waybackurls | https://github.com/tomnomnom/waybackurls |
| aquatone | https://github.com/michenriksen/aquatone |
| subjs | https://github.com/lc/subjs |
| new-zile | https://github.com/bonino97/new-zile |
| LinkFinder | https://github.com/GerbenJavado/LinkFinder |
| paramspider | https://github.com/devanshbatham/ParamSpider |
| dirsearch | https://github.com/maurosoria/dirsearch |
| TelegramBot | https://core.telegram.org/bots |
- Docker service installed
You can use the docker image by the next two options:
If you want to build the container yourself manually, git clone the repo, then build and run the following commands
git clone --depth 1 https://github.com/l34r00t/mainRecon.git
cd mainRecon
If you want Telegram Alert, you must modify the telegram bot_token and telegram chat_ID in mainRecon.sh
Also, you can configure access token for run findomain. You must configure the Dockerfile ("ENTER_TOKEN_HERE").
Build your docker container
linux/amd64:
docker build -t mainrecon-master .
Others (including Apple silicon):
docker build --platform=linux/amd64 -t mainrecon .
After building the container using either way, run the following:
linux/amd64:
docker run --rm -it -v /path/to/local/directory:/mainData mainrecon -p [--program] <hackerone> -f [--file] targets.txt
Others (including Apple silicon):
docker run --platform linux/amd64 --rm -it -v /path/to/local/directory:/mainData mainrecon -p [--program] <hackerone> -f [--file] targets.txt
Use image from docker hub: l34r00t/mainrecon
docker pull l34r00t/mainrecon
docker run --rm -it --env chat_ID="your_chat_ID" --env token="your_token" \
--env findomain_fb_token="fb_token" \
--env findomain_spyse_token="spyse_token" \
--env findomain_virustotal="virustotal_token" \
--env findomain_securitytrails_token="securitytrails_token" \
-v /path/to/local/directory:/mainData --name mainrecon l34r00t/mainrecon -p [--program] <hackerone> -f [--file] targets.txt
There are differents use cases for use the image and you should know how to run the container properly.
Share information from your local directory to container directory and save information on your local directory. You should save information under /mainData directory.
linux/amd64:
docker run --rm -it -v /path/to/local/directory:/mainData --name mainrecon l34r00t/mainrecon -p [--program] <hackerone> -f [--file] targets.txt
Others (including Apple silicon):
docker run --platform linux/amd64 --rm -it -v /path/to/local/directory:/mainData --name mainrecon l34r00t/mainrecon -p [--program] <hackerone> -f [--file] targets.txt
Your targets.txt should include a list of domains you're checking and should look something like:
hackerone.com
hackerone-ext-content.com
hackerone-user-content.com
Thank you Edu4rdSHL for you telegram webhook write-up.
In the following repository you will obtain all h1 recon results
The image was tested in the following environments:
-
Docker service for Mac: Docker version 19.02.7, build afacb8b
-
Docker service for Ubuntu 19.20 in Digital Ocean VPS: Docker version 18.09.7, build build 2d0083d
If you like my content, please consider inviting me to a coffee. Thank you for your support!
mainRecon has been possible thank you to the following projects.
- Edu4rdSHL
- tomnomnom
- OWASP
- michenriksen
- bonino97
- GerbenJavado
- devanshbatham
- subjs
- maurosoria
- Telegram BOT
- LazyRecon
- SubEnum
- aaaguirre
- mainRecon was written for education purposes only.
MIT Copyright (c) 2020, L34r00t