wmiexec2.0is the samewmiexecthat everyone knows and loves (debatable).- This 2.0 version is obfuscated to avoid well known signatures from various AV engines.
- It also has a handful of additional built in modules to help automate some common tasks on Red team engagements.
- This script is under active development and will improve with time.
- If you find an issue or want a specific module throw me a PR.
- Enjoy
- Do not
wgetthis file withGitHubs Rawfeature, it will break the Ghost emoji. Git clone the repo and it will all work.
git clone https://github.com/ice-wzl/wmiexec2.git
cd wmiexec2/
pip3 install -r requirements.txt
- Tested on:
#Windows Server 2022 Updated Febuary Defender Sigs
All modules working, no module flags
#Windows 10 Pro Defender Virus + Spyware Definition Version: 1.381.3595.0 2/14/2023
All modules working, no module flags
#Windows 10 Pro Kaspersky Standard App Version 21.8.5.452, Definitions 2/15/23
All modules working, no module flags
#Windows 8 Defender Virus and Spyware Definition Version: 1.383.35.0 2/15/2023
All modules working, no module flags
#Windows 7 Pro Defender Antispyware Definitions: v1.95.191.0 11/18/2010
Reg module not working, no module flags
- To view the help and available modules:
C:\>help
- You can still connect to the remote machine the exact same way.
- Recommend you use
-shell-type powershelluntil I have had further time to test all the modules on bothcmdandpowershell - In the meantime if you are worried about
powershelllogging just downgrade topowershell 2.0 - Password auth + NT Hash auth still both apply
python3 wmiexec2.0.py DOMAIN/USERNAME:PASSWORD@10.0.0.2 -shell-type powershell
python3 wmiexec2.0.py WORKGROUP/Administrator:'Password123!@#'@10.0.0.4 -shell-type powershell
lcd {path}change directory on your local machineexityou should know this onelput {src_file} {dst_file}upload local file to remote machine pathlget {file}download remote file to your local machine! {cmd}execute local system command -->!lslists your current directory on your local machine
- Everything else from here and below is additional features added into
wmiexecto make itwmiexec2.0 cat- just to make this more unix friendly simply usestypeon the remote machine to view a file....just an alias you can usels||ls C:\Users- allows you to view your current target directory. Its executing thedir /acommand so you will see hidden files by default without any other special options
- View some well known security products running on the target system.
- Enumerates the process list to see if they are running.
- Attempts to detect if you are in a virtual machine (So far works for ESXi/VMWare Workstation and QEMU)
- Performs three checks
- Looks for
C:\Program Files\VMWare - Looks for common running executables in a proccess list
- Pulls the
System Manufactuerfrom host 
- There are 11 files (that I know of) part of the
unattendgroup in Windows that have the potential to have base64 encoded credentials in them. Find them all in one command 
- Save off the
SAM,SecurityandSystemhives to your local machines. Defender blocks this by default, so I had to find a bypass working as of 2/7/23. Try to not get this signatured, thanks in advance. 
- Leverage Windows built in
netshtunneling without having to type the whole thing out - See picture for usage options

- Download log file of your choice
- Will download any file in
C:\windows\system32\winevt\logs - Use:
loggrab Security.evtx 
- under active development
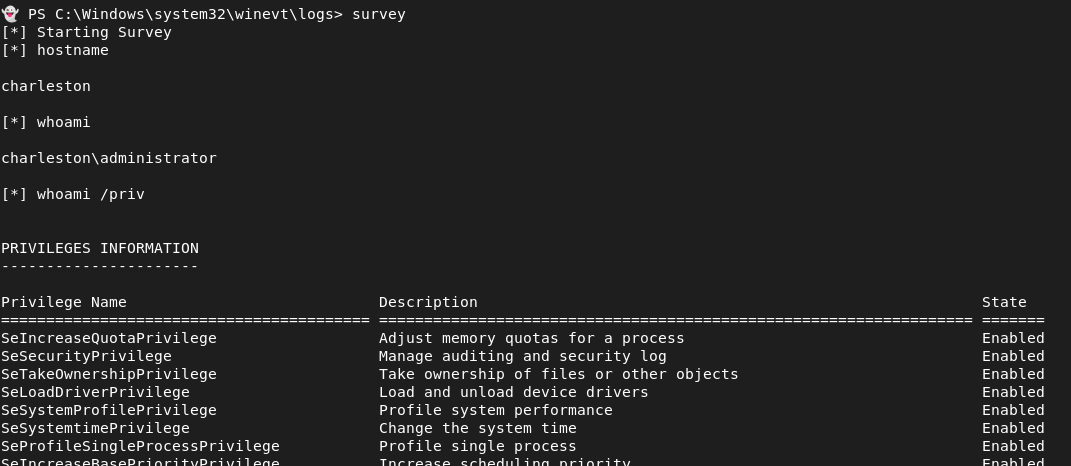
- Input your own custom commands into
survey.conffile seperated by a new line, or use the basic one that I have provided - There are two options with this module:
- run module with
surveywhich will print out the command you ran plus the output of that command - Or run with
survey savethis will return none of the commands to stdout, but will save all commands run and their output intosurvey.txtlocated in your local pwd.