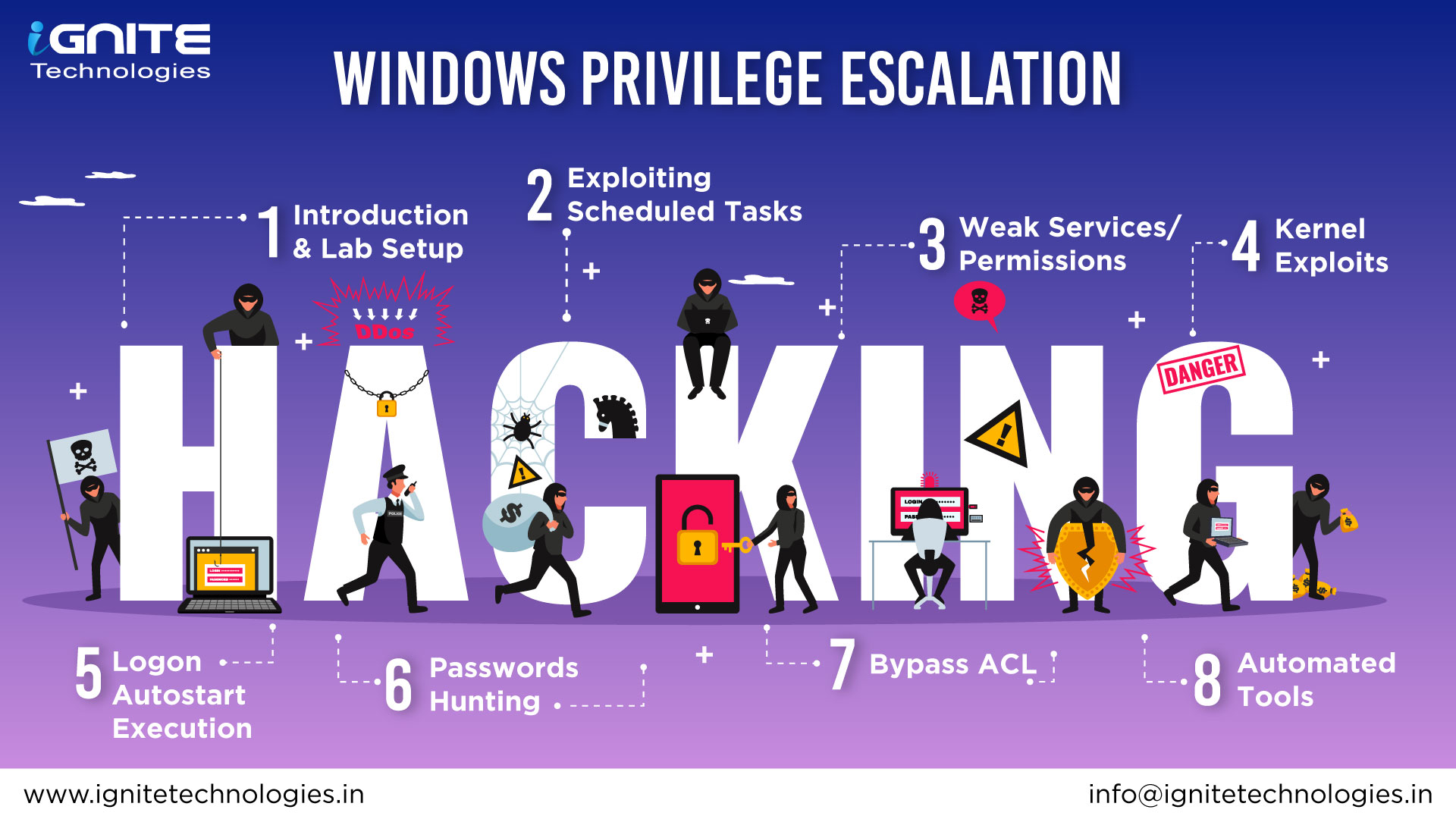
This cheatsheet is aimed at OSCP aspirants to help them understand the various methods of escalating privilege on Windows-based machines and CTFs with examples. There are multiple ways to perform the same task. We have performed and compiled this list based on our experience. Please share this with your connections and direct queries and feedback to Hacking Articles.
- AlwaysInstallElevated
- SeBackupPrivilege
- DnsAdmins to DomainAdmin
- SeImpersonatePrivilege
- HiveNightmare
- Logon Autostart Execution (Registry Run Keys)
- Boot Logon Autostart Execution (Startup Folder)
- Stored Credentials (Runas)
- Weak Registry Permission
- Unquoted Service Path
- Insecure GUI Application
- Weak Service Permissions
- Scheduled Task/Job (T1573.005)
- Kernel Exploit
- SamAccountSpoofing (CVE-2021–42278)
- SpoolFool
- PrintNightmare
- Server Operator Group