- OSX Mojave with Homebrew, Latest Updates
- Raspbian Stretch/Stretch-Lite, Latest Updates
- Ubuntu 16.04+, Latest Updates
General discussion mailllist: deployment, tweaks and tuning:
- mailto:eotk-users+subscribe@googlegroups.com (via email)
- https://groups.google.com/group/eotk-users/subscribe (via web)
NB: bugs are still best reported through Issues, above.
- new features
- auto-generate (
eotk make-scripts) wrapper scripts for:- installation into "init" startup
eotk-init.sh - log rotation / housekeeping via installation into eotk-user cronjob (
eotk-housekeeping.sh)
- installation into "init" startup
- stricter enforcement of onionification
- by default will drop compressed, non-onionifiable content with error code
520 - if this is a problem (why?) use
set drop_unrewritable_content 0to disable
- by default will drop compressed, non-onionifiable content with error code
- validate worker onion addresses upon creation
- works around issue logged with tor
eotk spotpushnow permits pushing explicitly named scripts from$EOTK_HOME, as well as hunting inprojects.dset hard_mode 1is now default and onionifies bothfoo.comANDfoo\.com(regexp-style)- use
set hard_mode 2to further onionifyfoo\\.comandfoo\\\.comat slight performance cost
- use
set ssl_mkcert 1to use mkcert by @FiloSottile for certificate generation, if you have installed it- refactor nonces used in rewriting preserved strings
- improvements to
set debug_trap pattern [...]logging - support for OpenResty LuaJIT in Raspbian build scripts
- update code version for Raspbian builds scripts
- tor HiddenServiceVersion nits
- dead code removal
- deprecate support for Raspbian Jessie
- auto-generate (
- new features
- "Runbook" has been moved to the documentation directory
- tor2web has been blocked-by-default
- since the reason for EOTK is to provide Clearnet websites with an Onion presence, Tor2web is not necessary
- the
FORCE_HTTPSfeature has been added and made default- if your site is 100% HTTPS then you do not need to do anything,
- however sites which require insecure
HTTPmay have to useset force_https 0in configurations.
- new features:
- optional blocks to methods other than GET/HEAD
- optional 403/Forbidden blocks for accesses to certain Locations or Hosts, including as regexps
- nb: all blocks/block-patterns are global and apply to all servers in a project
- optional time-based caching of static content for
Nseconds, with selectable cache size (def: 16Mb)
- new How To Install guide
- custom install process for Ubuntu, tested on Ubuntu Server 16.04.2-LTS
- renaming / factor-out of Raspbian install code
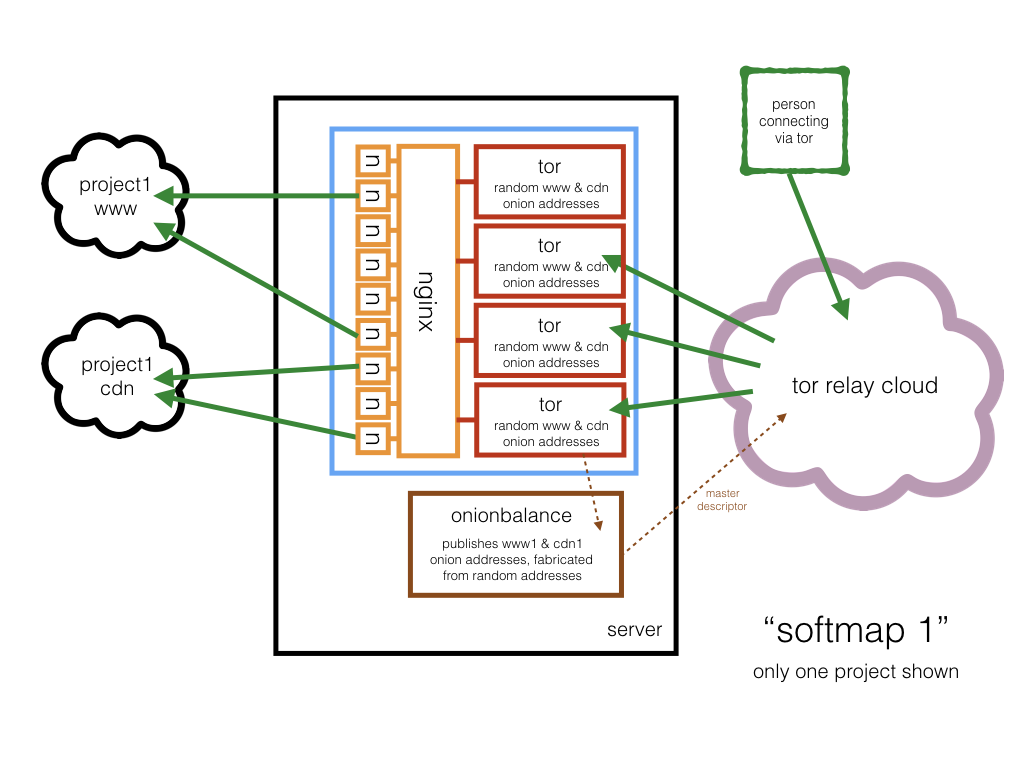
- fixes to onionbalance support
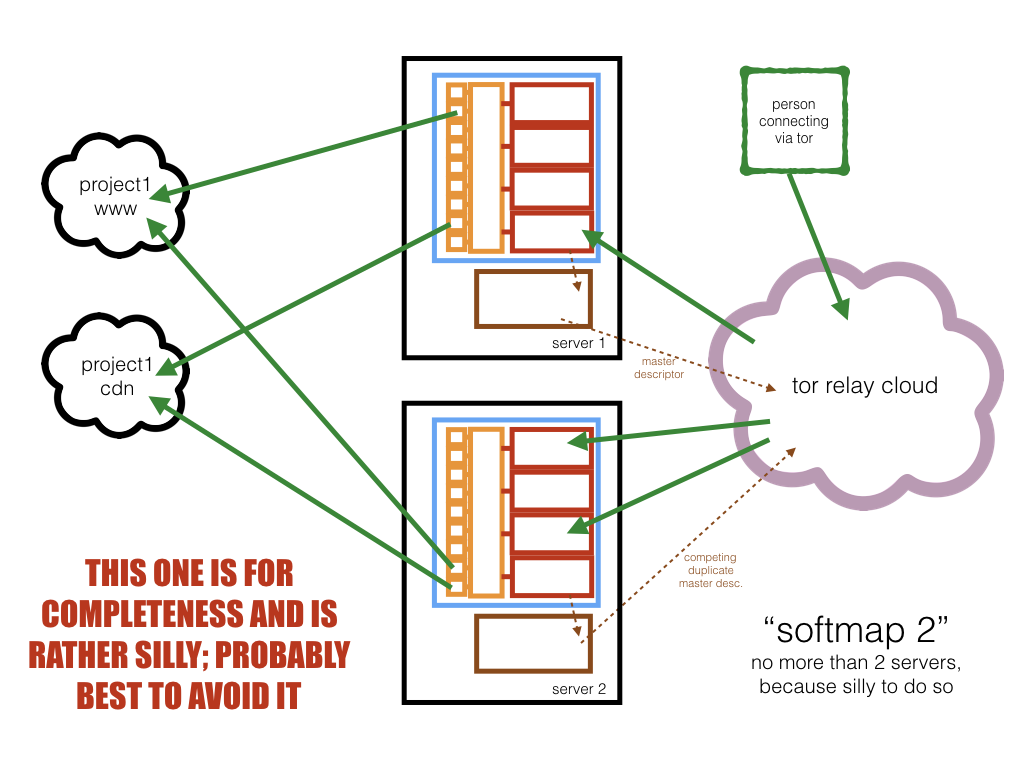
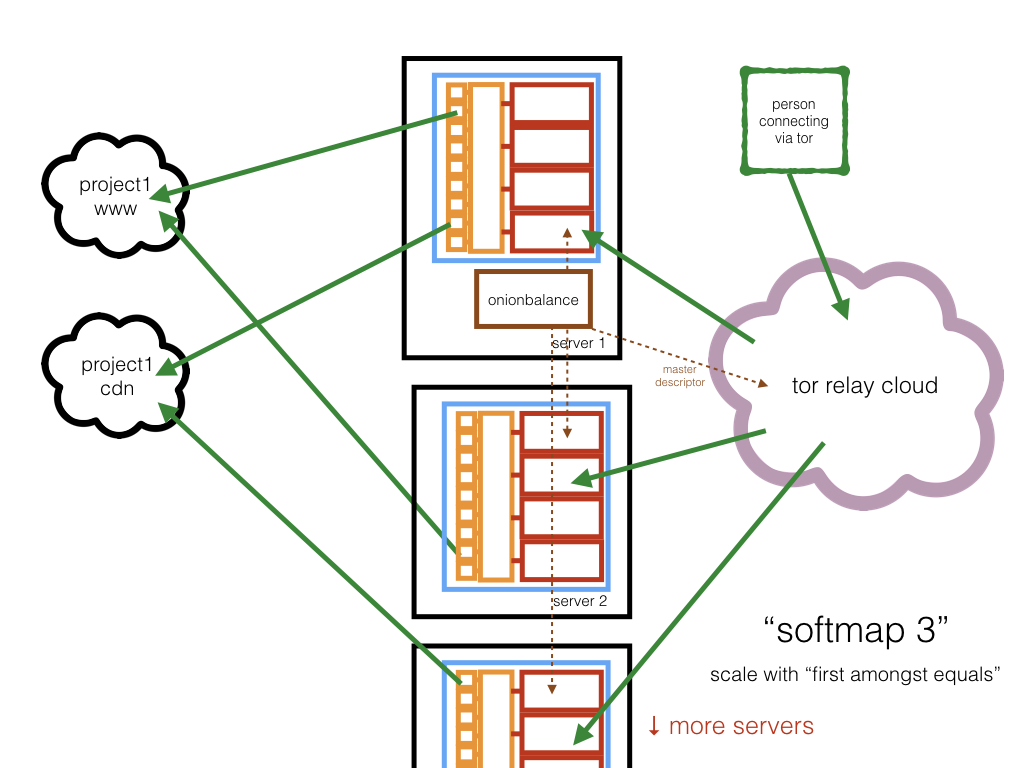
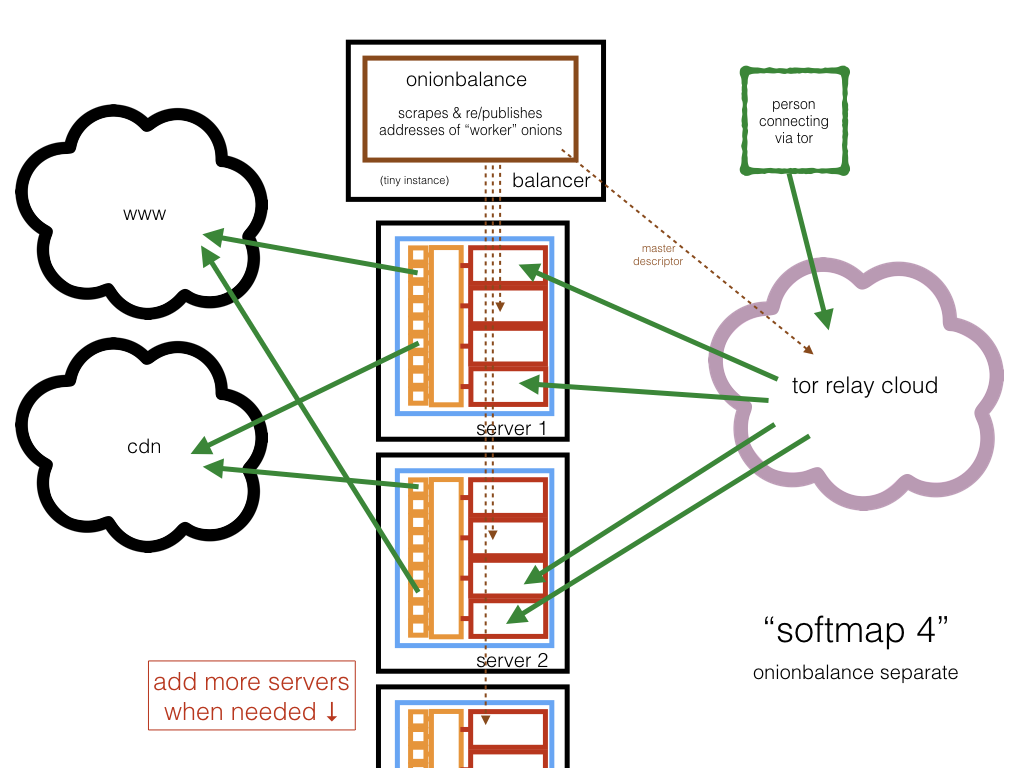
- first cut of onionbalance / softmap
- have declared a stable alpha release
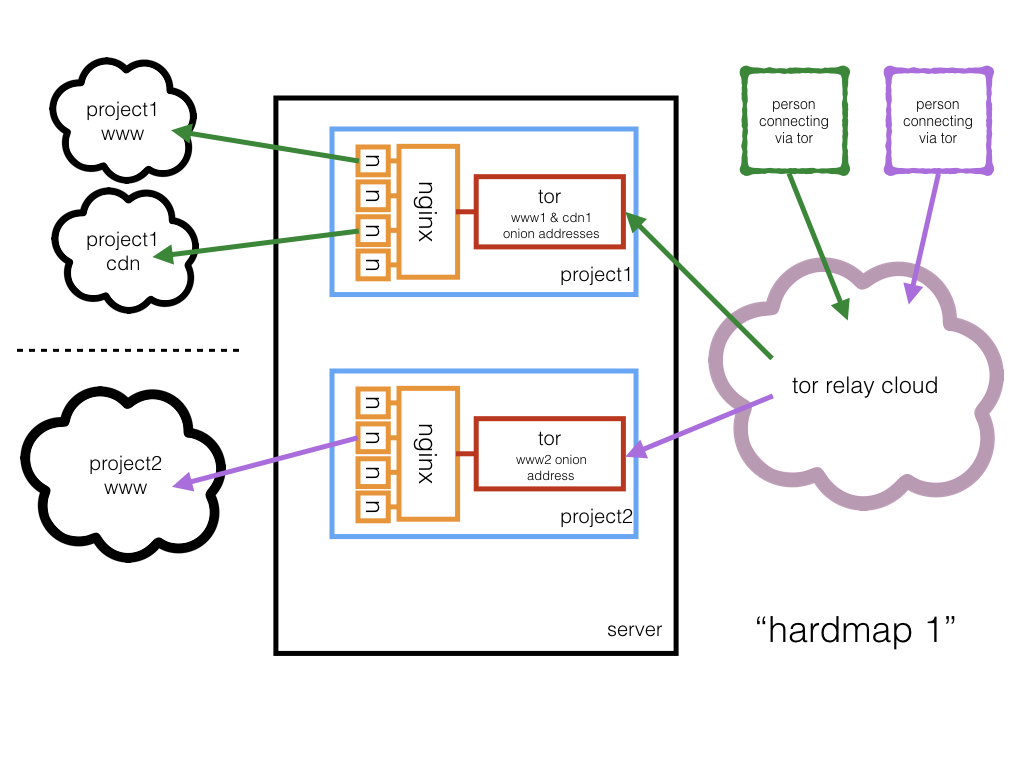
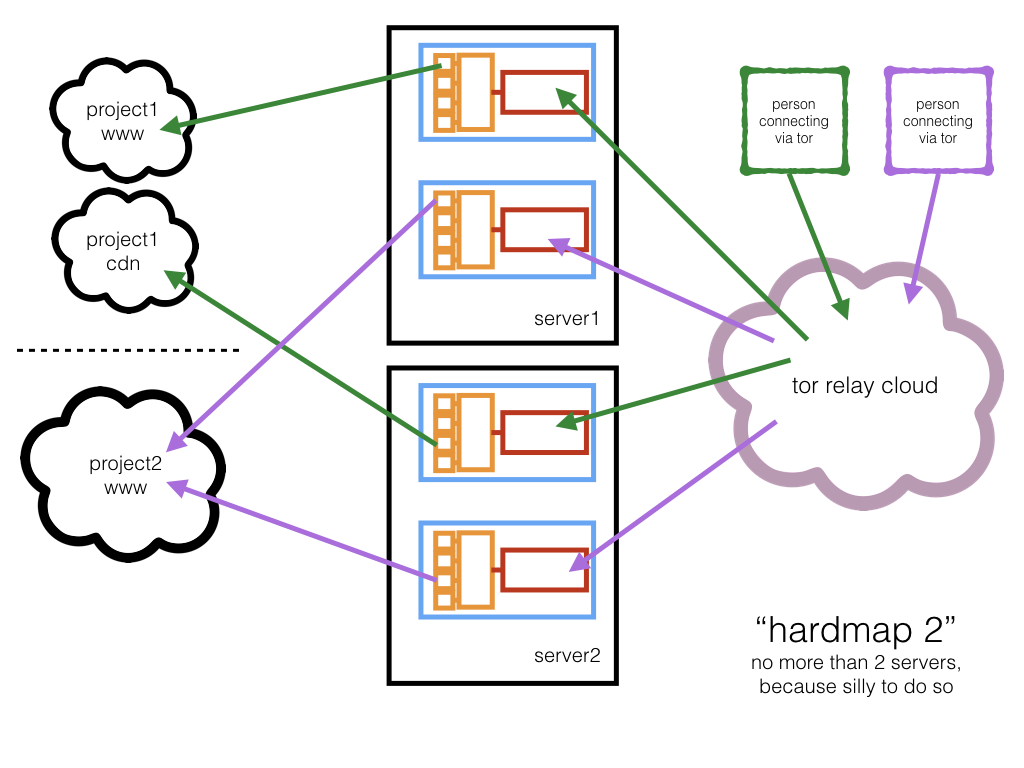
- architecture images, at bottom of this page
- all of CSP, HSTS and HPKP are suppressed by default; onion networking mitigates much of this
- "tunables" documentation for template content
troubleshootingsection near the bottom of this page- See project activity for information
- Jan 2018 Volunteer Spotlight: Alec Helps Companies Activate Onion Services
- Nov 2017 Un service Wikipedia pour le Dark Web a été lancé par un ingénieur en sécurité
- Nov 2017 Δημιουργήθηκε σκοτεινή έκδοση της Βικιπαίδειας για ανθρώπους σε λογοκριμένα καθεστώτα
- Nov 2017 A security expert built an unofficial Wikipedia for the dark web
- Nov 2017 There’s Now a Dark Web Version of Wikipedia
- Oct 2017 The New York Times is Now Available as a Tor Onion Service
- Apr 2017 This Company Will Create Your Own Tor Hidden Service
- Feb 2017 New Tool Takes Mere Minutes to Create Dark Web Version of Any Site
The goal of EOTK is to provide a tool for prototyping, and deploying at scale, HTTP and HTTPS onion sites to provide official presence for popular websites.
The results are essentially a "man in the middle" proxy; set them up only for your own sites or for sites which do not require login credentials of any kind.
The resulting NGINX configs are probably not terribly well tuned; please review for your own consideration. I shall try not to modify the configuration file format.
The presumed use-case of EOTK is that you have an already-public website and that you wish to give it a corresponding Onion address.
A lot of people mistakenly believe that Tor Onion Networking is "all about anonymity" - which is incorrect, since it also includes:
- extra privacy
- identity/surety of to whom you are connected
- freedom from oversight/network surveillance
- anti-blocking, and...
- enhanced integrity/tamperproofing
...none of which are the same as "anonymity", but all of which are valuable qualities to add to communications.
Also: setting up an Onion address can provide less contention, more speed & more bandwidth to people accessing your site than they would get by using Tor "Exit Nodes".
If you set up EOTK in its intended mode then your resulting site is almost certainly not going to be anonymous; for one thing your brand name (etc) will likely be plastered all over it.
If you want to set up a server which includes anonymity as well as all of the aforementioned qualities, you want to be reading an entirely different document, instead.
When connecting to the resulting onions over HTTP/SSL, you will be using wildcard self-signed SSL certificates - you will encounter many "broken links" which are due to the SSL certificate not being valid. This is expected and proper behaviour.
To help cope with this, for any domain (eg: www.a2s3c4d5e6f7g8h9.onion) the EOTK provides a fixed url:
https://www.a2s3c4d5e6f7g8h9.onion/hello-onion/
...which (/hello-onion/) is internally served by the NGINX proxy and
provides a stable, fixed URL for SSL certificate acceptance; inside
TorBrowser another effective solution is to open all the broken links,
images and resources "in a new Tab" and accept the certificate there.
In production, of course, one would expect to use an SSL EV certificate to provide identity and assurance to an onion site, rendering these issues moot.
--local: ignore the presence ofeotk-workers.confand operate upon local projects; used to administer projects running locally on a machine which might also be running onionbalance.--remote: functionally the same as--localbut denotes remote execution on a worker; used to inhibit recursion and loops amongst worker machines, of A calls B calls A calls B ...
eotk config [filename]# defaultonions.conf- synonyms:
conf,configure - parses the config file and sets up and populates the projects
- synonyms:
eotk maps projectname ...# or:-afor all- prints which onions correspond to which dns domains
- for softmap, this list may not show until after
ob-configandob-start
eotk harvest projectname ...# or:-afor all- synonyms:
onions - prints list of onions used by projects
- synonyms:
eotk genkey- synonyms:
gen - generate an onion key and stash it in
secrets.d
- synonyms:
eotk status projectname ...# or:-afor all- active per-project status
eotk ps- do a basic grep for possibly-orphaned processes
eotk debugon projectname ...# or:-afor all- enable verbose tor logs
eotk debugoff projectname ...# or:-afor all- disable verbose tor logs
eotk start projectname ...# or:-afor all- start projects
eotk stop projectname ...# or:-afor all- stop projects
eotk restart projectname ...# or:-afor all- synonyms:
bounce,reload - stop, and restart, projects
- synonyms:
eotk nxreload projectname ...# or:-afor all- politely ask NGINX to reload its config files
eotk ob-start projectname ...# or:-afor all, if applicable- synonyms:
eotk ob-restart projectname ...# or:-afor all, if applicable- synonyms:
eotk ob-stop- synonyms:
eotk ob-status- synonyms:
eotk-workers.conf- if not present, only
localhostwill be used - if present, contains one hostname per line, no comments
- the label
localhostis a hardcoded synonym for local activity - other (remote) systems are accessed via
ssh,scp&rsync
- the label
- if not present, only
eotk ob-remote-nuke-and-push- synonyms:
eotk ob-nxpush- synonyms:
eotk ob-torpush- synonyms:
eotk ob-spotpush- synonyms:
- eotk
mirror- synonyms:
- eotk
backup- synonyms:
Please see How To Install guide
These videos are instructive, but slightly dated. Commands may have changed slightly, but not much, and I will try to help you understand what has changed rather than break the command entirely.
After installation, if you want to experiment with some prefabricated projects, try this:
./010-configure-demo.sh- creates working config files, and tor & nginx config files
- Follow the on-screen instructions to start your onions
- Connect to your onions
- Play exciting games of "SSL-Certificate-Acceptance-Whackamole"
Okay, there are two ways to create your own project:
Create a config file with a .tconf suffix - we'll pretend it's
foo.tconf - and use this kind of syntax:
set project myproject
hardmap %NEW_ONION% foo.com
hardmap %NEW_ONION% foo.co.uk
hardmap %NEW_ONION% foo.de
...and then run
eotk config foo.tconf
...which will create the onions for you and will populate a foo.conf
for you, and it will then configure EOTK from that. You should
probably delete foo.tconf afterwards, since forcibly reusing it
would trash your existing onions.
- Do
eotk genkey- it will print the name of the onion it generates- Do this as many times as you wish/need.
- Alternately get a tool like
scallionorshallotand use that to "mine" a desirable onion address.- https://github.com/katmagic/Shallot - in C, for CPUs
- Seems okay on Linux, not sure about other platforms
- https://github.com/lachesis/scallion - in C#, for CPUs & GPUs (GPU == very fast)
- Advertised as working on Windows, Linux; works well on OSX under "Mono"
- Be sure to store your mined private keys in
secrets.dwith a filename likea2s3c4d5e6f7g8h9.keywherea2s3c4d5e6f7g8h9is the corresponding onion address.
- https://github.com/katmagic/Shallot - in C, for CPUs
- Create a config file with a
.confsuffix - we'll pretend it'sfoo.conf- and use this kind of syntax, substitutinga2s3c4d5e6f7g8h9for the onion address that you generated.
set project myproject
hardmap secrets.d/a2s3c4d5e6f7g8h9.key foo.com
...and then (IMPORTANT) run:
eotk config foo.conf
...which will configure EOTK.
Like this:
eotk start myproject
When you are setting up the mappings in a config file, you may have to accomodate "subdomains"; the general form of a internet hostname is like this:
hostname.domain.tld# like: www.facebook.com or www.gov.uk- or:
hostname.domain.sld.tld# like: www.amazon.co.uk
- or:
hostname.subdom.domain.tld# like: www.prod.facebook.comhostname.subsubdom.subdom.domain.tld# cdn.lhr.eu.foo.nethostname.subsubsubdom.subsubdom.subdom.domain.tld# ...
...and so on, where:
- tld = top level domain
- sld = second level domain
- domain = generally the name of the organisation you are interested in
- subdomain = some kind of internal structure
- hostname = actual computer, or equivalent
When you are setting up mappings, generally the rules are:
- you will map one domain per onion
- you will ignore all hostnames
- you will append all possible subdomain stems
So if your browser tells you that you are fetching content from
cdn7.dublin.ireland.europe.foo.co.jp, you should add a line like:
hardmap %NEW_ONION% foo.co.jp europe ireland.europe dublin.ireland.europe
...and EOTK should do the rest. All this is necessary purely for correctness of the self-signed SSL-Certificates - which are going to be weird, anyway - and the rest of the HTML-rewriting code in EOTK will be blind to subdomains.
Subdomains are supported like this, for dev as an example:
set project myproject
hardmap secrets.d/a2s3c4d5e6f7g8h9.key foo.com dev
...and if you have multiple subdomains:
hardmap secrets.d/a2s3c4d5e6f7g8h9.key foo.com dev blogs dev.blogs [...]
Example:
www.foo.com.auwww.syd.foo.com.auwww.per.foo.com.au,www.cdn.foo.netwww.foo.aws.amazon.com- ...
Put them all in the same project as separate mappings, remembering to avoid the actual "hostnames" as described above:
set project fooproj
hardmap %NEW_ONION% foo.com.au syd per
hardmap %NEW_ONION% foo.net cdn
hardmap %NEW_ONION% foo.aws.amazon.com
Onion mapping/translations will be applied for all sites in the same project.
The logs for any given project will reside in
projects.d/<PROJECTNAME>.d/logs.d/
If something is problematic, first try:
git pulland...eotk config <filename>.confagain, and then...eotk bounce -a
This is probably an SSL/HTTPS thing.
Because of the nature of SSL self-signed certificates, you have to manually accept the certificate of each and every site for which a certificate has been created. See the second of the YouTube videos for some mention of this.
In short: this is normal and expected behaviour. You can temporarily fix this by:
- right-clicking on the image for
Open In New Tab, and accepting the certificate - or using
Inspect Element > Networkto find broken resources, and doing the same - or - if you know the list of domains in advance - visiting the
/hello-onion/URL for each of them, in advance, to accept certificates.
If you get an official SSL certificate for your onion site then the problem will vanish. Until then, I am afraid that you will be stuck playing certificate "whack-a-mole".
Generally this means that NGINX cannot connect to the remote website, which usually happens because:
- the site name in the config file, is wrong
- the nginx daemon tries to do a DNS resolution, which fails
Check the NGINX logfiles in the directory cited above, for confirmation.
If DNS resolution is failing, PROBABLY the cause is probably lack
of access to Google DNS / 8.8.8.8; therefore in your config file
you should add a line like this - to use localhost as an example:
set nginx_resolver 127.0.0.1
...and then do:
eotk stop -a
eotk config filename.conf
eotk start -a
If you need a local DNS resolver, I recommend dnsmasq.
If your onion project has just started, it can take up to a few
minutes to connect for the first time; also sometimes TorBrowser
caches stale descriptors for older onions. Try restarting TorBrowser
(or use the New Identity menu item) and have a cup of tea. If it
persists, check the logfiles.
Is the clock/time of day correct on all your machines? Are you running NTP? We are not sure but having an incorrect clock may be a contributory factor to this issue.
Ping @alecmuffett on Twitter, or log an Issue, above.
EOTK stands largely on the experience of work I led at Facebook to
create www.facebookcorewwwi.onion, but it owes a huge debt to
Mike Tigas's work at ProPublica to put
their site into Onionspace through using NGINX as a rewriting proxy --
and that
he wrote the whole experience up in great detail
including
sample config files.
Reading this prodded me to learn about NGINX and then aim to shrink & genericise the solution; so thanks, Mike!
Also, thanks go to Christopher Weatherhead for acting as a local NGINX sounding board :-)
And back in history: Michal Nánási, Matt Jones, Trevor Pottinger and the rest of the FB-over-Tor team. Hugs.
eotk (c) 2017 Alec Muffett