Static code analysis checker for golang. If there's an error, it also sends comments back to the current pull request (or the current commit if the action's trigger wasn't a PR).
A quick summary of the values you can give using with.
Execute comma-separated command(s). Valid options are any combination of cyclo, errcheck, fmt, imports, ineffassign, lint, misspell,
sec, shadow, staticcheck, and vet, or the shorthand option all. See below for more details.
The directory to run the check(s) within. Useful for monorepos to check subdirectories rather than the entire repository.
If set to true (the default), a comment will be sent to the PR/commit that triggered the action whenever a check fails. If you prefer to check the
action logs, go ahead and turn this off.
GitHub token (use ${{ secrets.GITHUB_TOKEN }} for this, since it's automatically provided for you). This is required when comment is true (so,
by default).
Add flags to pass to the check commands. For a single check, just use the raw flag(s) here, but for multiple checks (including all), this should be
a JSON object whose keys are the check names, and whose values are the flag(s) for each specific check. If you really want to pass a flag to every
check, the all key is available, but be careful, as most check commands will fail with unrecognized flags. You can safely omit keys for checks
with no flags. See the sample workflows below for an example.
By default, errcheck marks defer statements as problems. Of course, sometimes (usually?) you want to defer certain logic, say for cleaning up
resources that Go can't/won't clean automatically. Simply set this to true to ignore this error as a false positive.
The highest cyclomatic complexity to consider "ok" with the cyclo check. The default of 15 was chosen to match Go Report
Card's grading value.
Login username for getting Go dependencies from private repos.
Password (or GitHub personal access token) for getting Go dependencies from private repos.
Private organization URL, eg. github.com/my-org, for getting Go dependencies from private repos.
Runs all the checks below in a semi-sane order. Internally, it just translates all to
misspell,fmt,vet,cyclo,imports,ineffassign,errcheck,sec,shadow,staticcheck,lint - you can take advantage of this to leave certain checks out, or to
change the order they run in. (I personally recommend dropping lint, since it's deprecated anyway...)
Keep in mind that this doesn't fail-fast, so all the listed checks will be run even if one fails.
Also keep in mind that you'll get one comment on your PR/commit for each check that fails, which can add up a bit if your code fails more than one consistently. This is currently considered a feature rather than a bug, though, for two reasons. First, it's extra incentive to correct the code! Second, GitHub enforces a comment-length limit that might prevent your combined error comment from posting, which gets frustrating quickly when you're trying to avoid scouring logs.
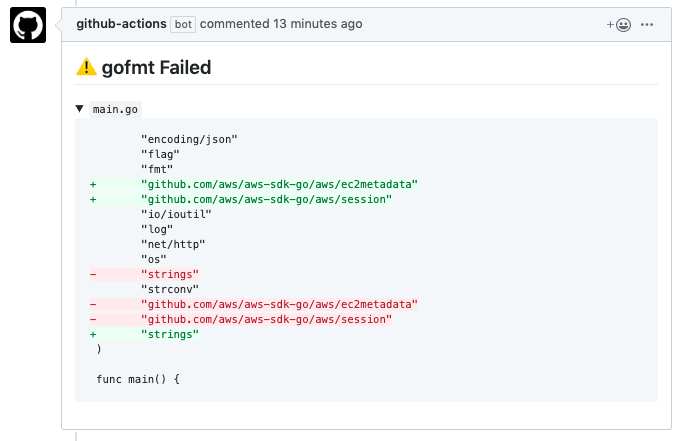
Runs gofmt (not to be confused with go fmt, which has fewer options) (and comments back on error).
Runs go vet (and comments back on error).
Runs go vet --vettool=$(which shadow) (and comments back on error).
See golang.org/x/tools/go/analysis/passes/shadow/cmd/shadow for more info.
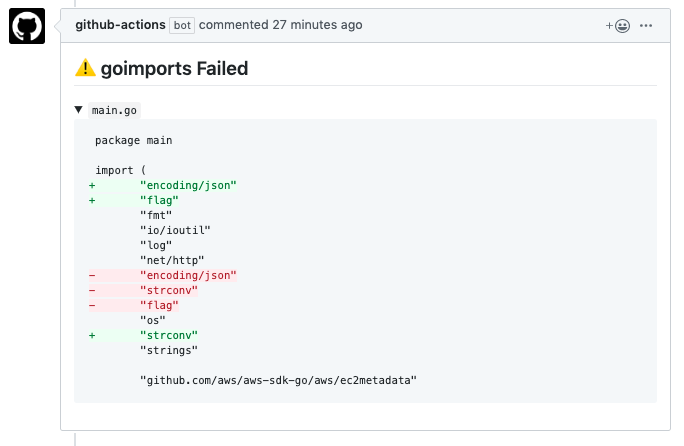
Runs goimports (and comments back on error).
See golang.org/x/tools/cmd/goimports for more info.
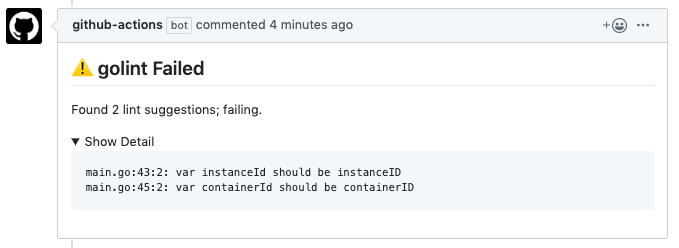
DEPRECATED
Runs golint (and comments back on error).
See golang.org/x/lint/golint for more info.
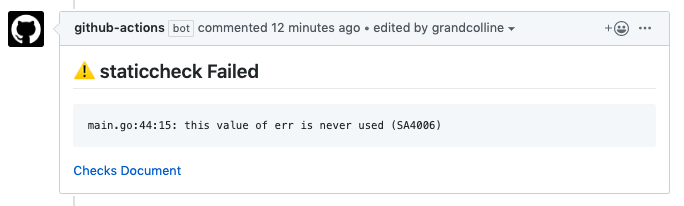
Runs staticcheck (and comments back on error).
See honnef.co/go/tools/cmd/staticcheck for more info.
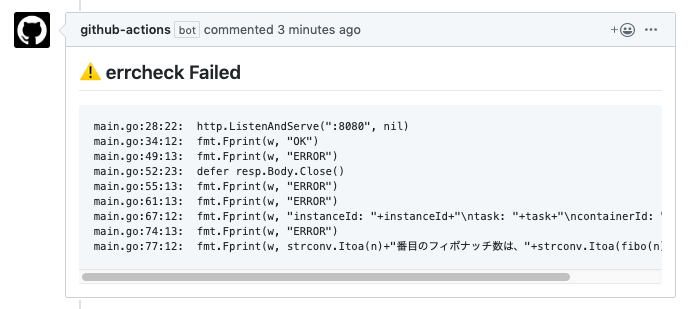
Runs errcheck (and comments back on error).
See github.com/kisielk/errcheck for more info.
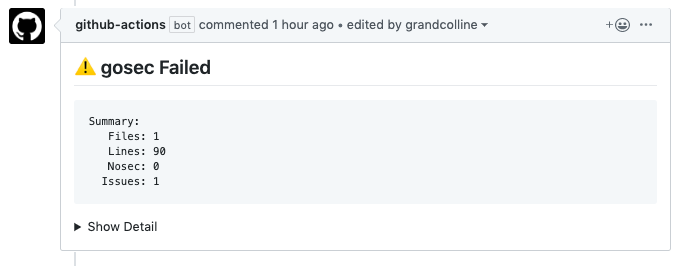
Runs gosec (and comments back on error).
See github.com/securego/gosec/cmd/gosec for more info.
Runs ineffassign (and comments back on error).
See github.com/gordonklaus/ineffassign for more info.
Runs misspell (and comments back on error).
See github.com/client9/misspell/cmd/misspell for more info.
Runs gocyclo (and comments back on error).
See github.com/fzipp/gocyclo/cmd/gocyclo for more info.
To run the imports, errcheck, lint, shadow, staticcheck, and sec checks in parallel:
.github/workflows/static.yml
name: static check
on: pull_request
jobs:
imports:
name: Imports
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@master
- name: check
uses: danhunsaker/golang-github-actions@v1.3.0
with:
run: imports
token: ${{ secrets.GITHUB_TOKEN }}
errcheck:
name: Errcheck
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@master
- name: check
uses: danhunsaker/golang-github-actions@v1.3.0
with:
run: errcheck
token: ${{ secrets.GITHUB_TOKEN }}
lint:
name: Lint
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@master
- name: check
uses: danhunsaker/golang-github-actions@v1.3.0
with:
run: lint
token: ${{ secrets.GITHUB_TOKEN }}
shadow:
name: Shadow
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@master
- name: check
uses: danhunsaker/golang-github-actions@v1.3.0
with:
run: shadow
token: ${{ secrets.GITHUB_TOKEN }}
staticcheck:
name: StaticCheck
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@master
- name: check
uses: danhunsaker/golang-github-actions@v1.3.0
with:
run: staticcheck
token: ${{ secrets.GITHUB_TOKEN }}
sec:
name: Sec
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@master
- name: check
uses: danhunsaker/golang-github-actions@v1.3.0
with:
run: sec
token: ${{ secrets.GITHUB_TOKEN }}
flags: "-exclude=G104"Or with the new multi-check feature (in serial):
.github/workflows/static-in-one.yml
name: static check in one go
on: pull_request
jobs:
in-one:
name: Imports
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@master
- name: check
uses: danhunsaker/golang-github-actions@v1.3.0
with:
run: imports,errcheck,lint,shadow,staticcheck,sec
token: ${{ secrets.GITHUB_TOKEN }}
flags: '{"sec": "-exclude=G104"}'