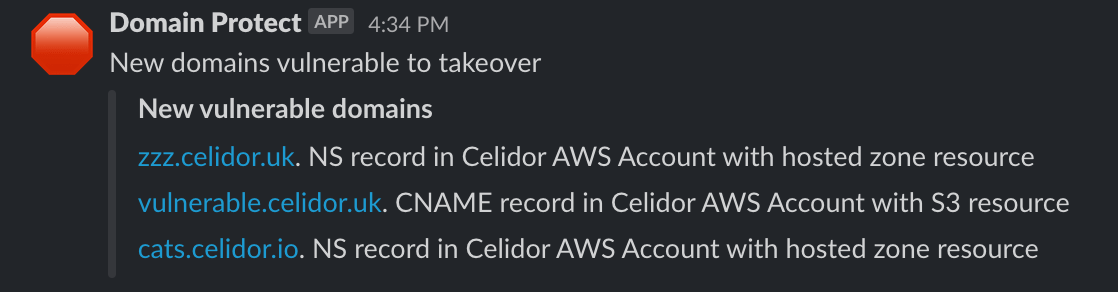
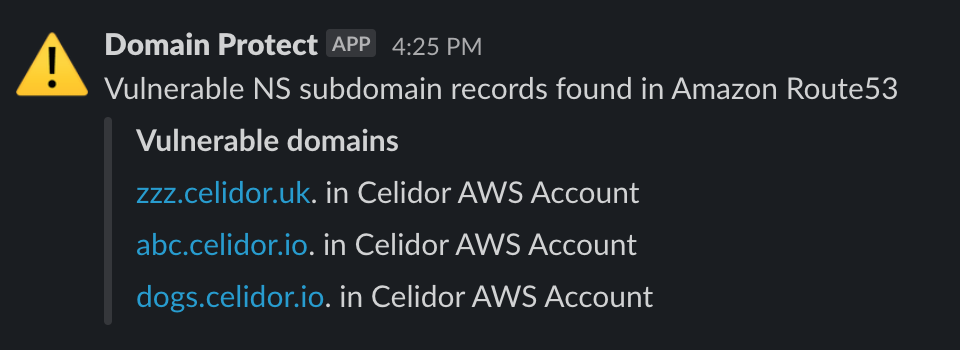
- scan Amazon Route53 across an AWS Organization for domain records vulnerable to takeover
- scan Cloudflare for vulnerable DNS records
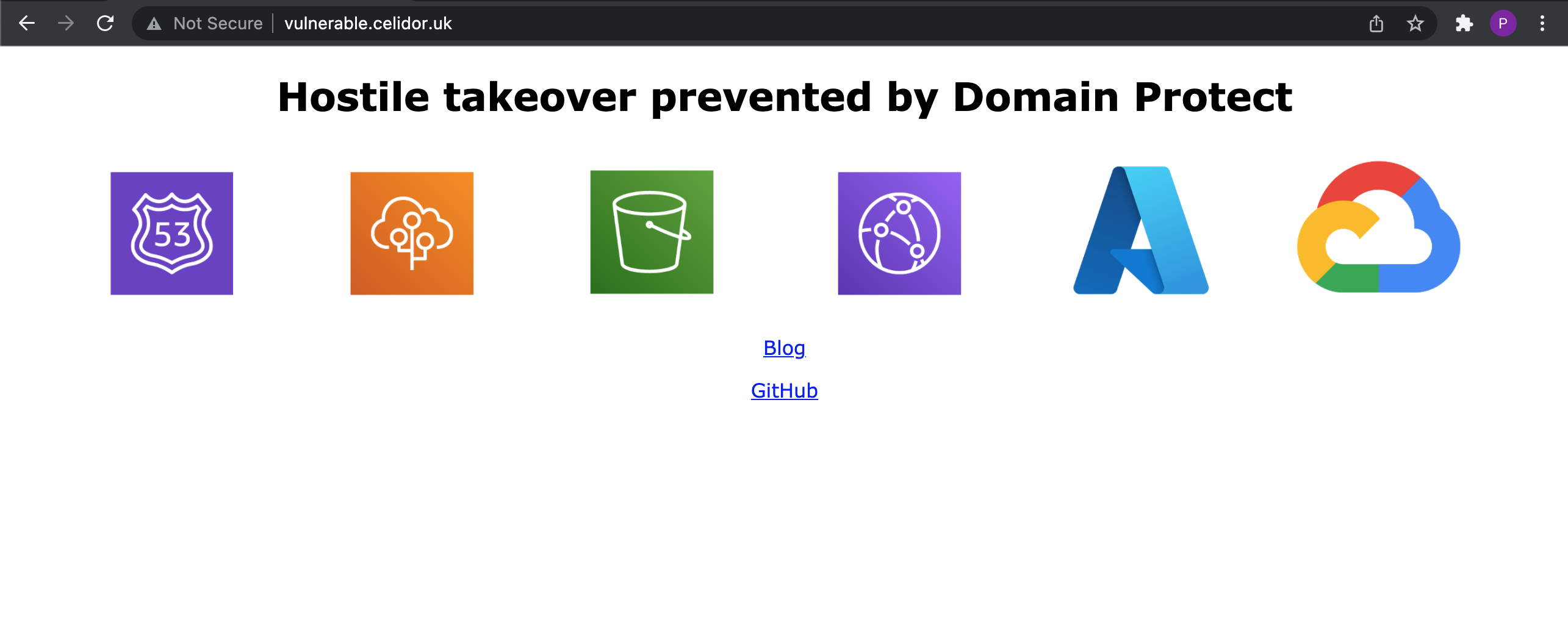
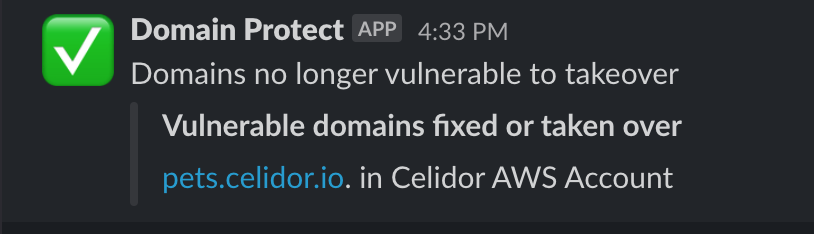
- take over vulnerable subdomains yourself before attackers and bug bounty researchers
- automatically create known issues in Bugcrowd
- vulnerable domains in Google Cloud DNS can be detected by Domain Protect for GCP
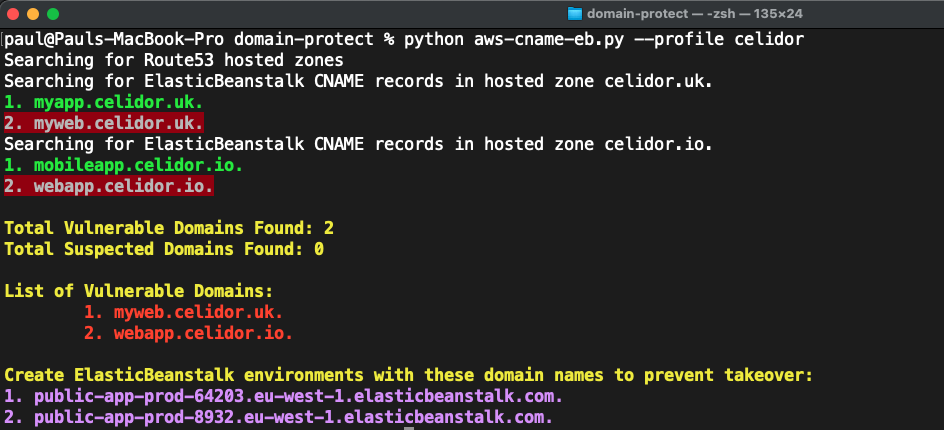
Manual scans - AWS
Manual scans - CloudFlare
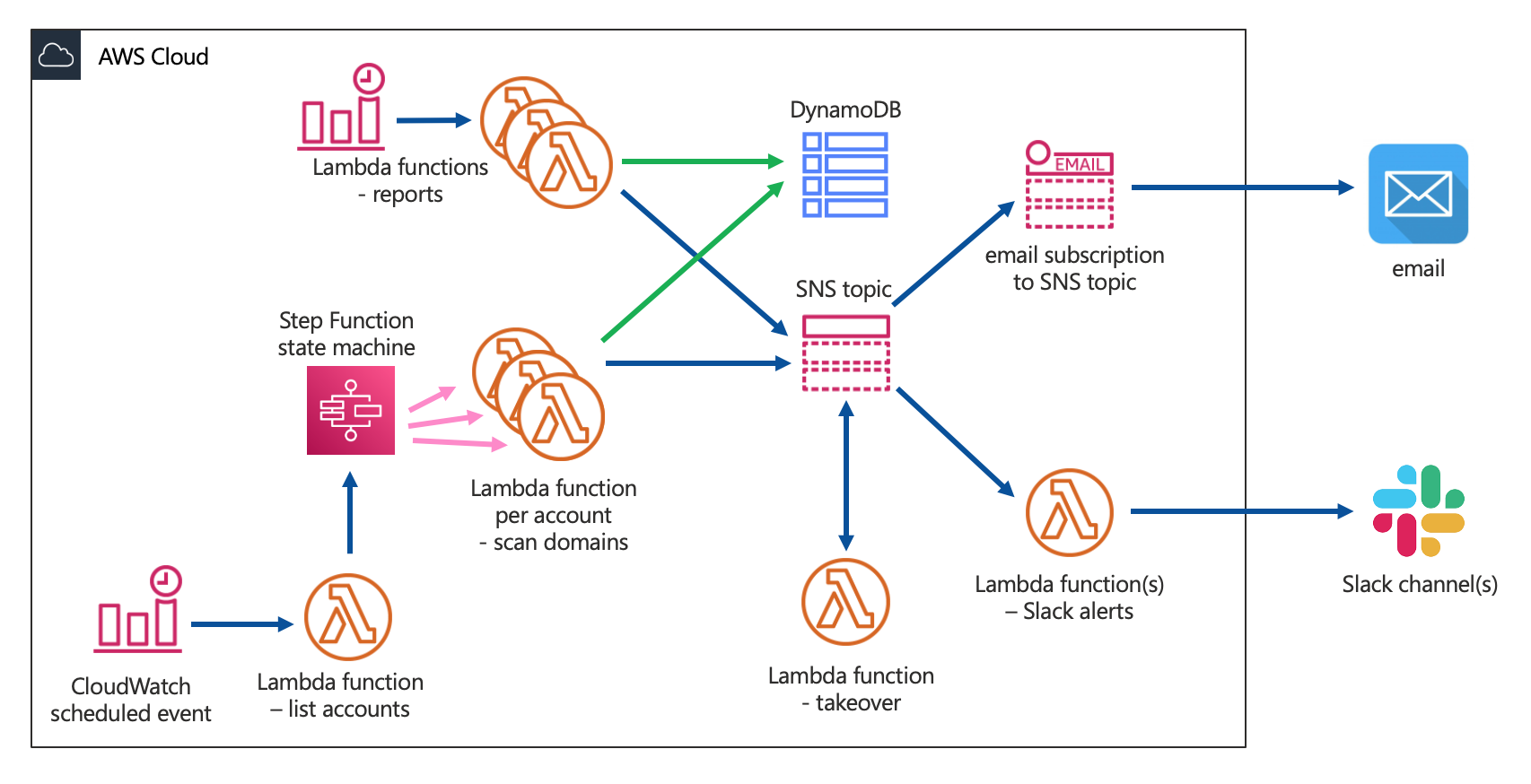
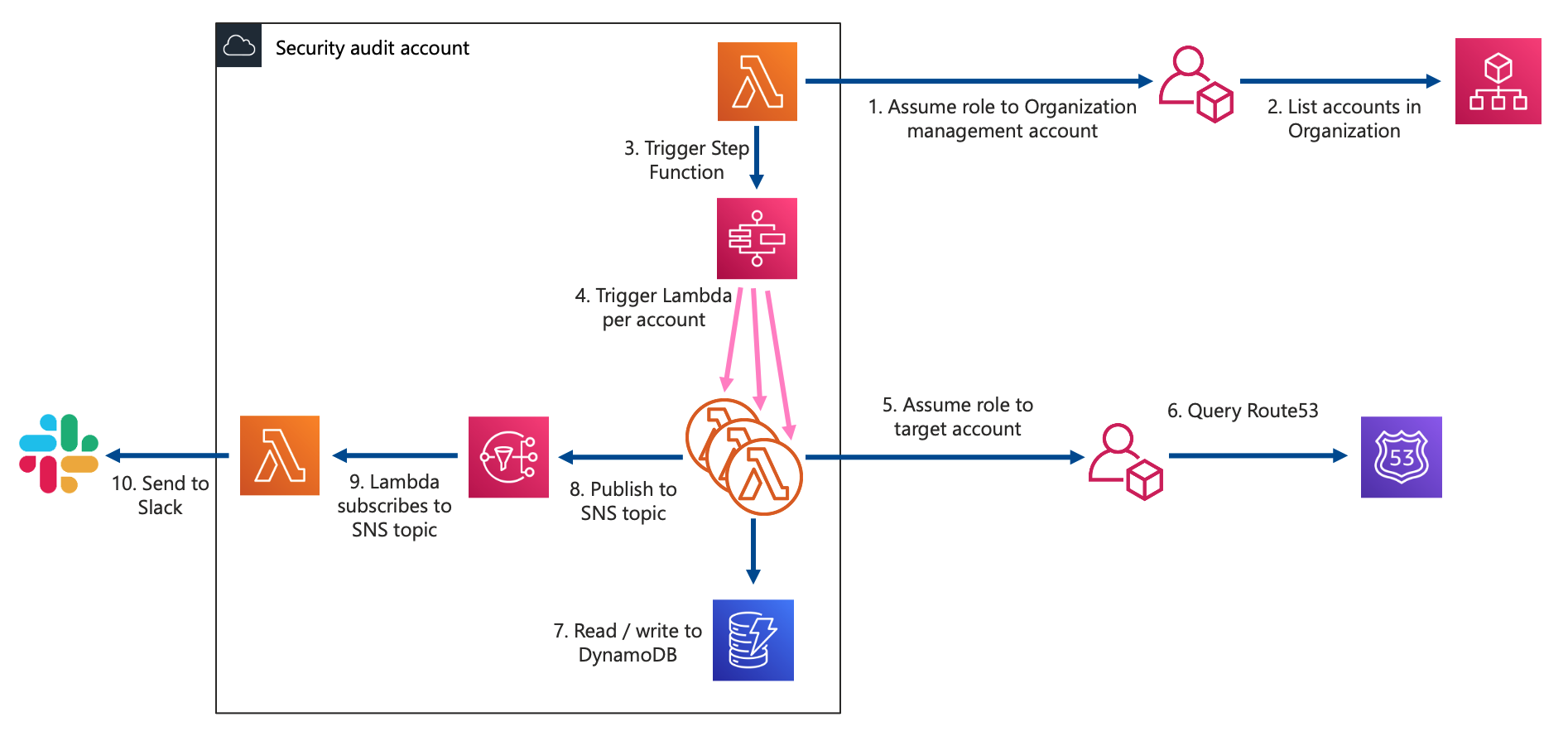
Architecture
Database
Reports
Automated takeover optional feature
Cloudflare optional feature
Bugcrowd optional feature
Vulnerability types
Vulnerable A records (IP addresses) optional feature
Requirements
Installation
AWS IAM policies
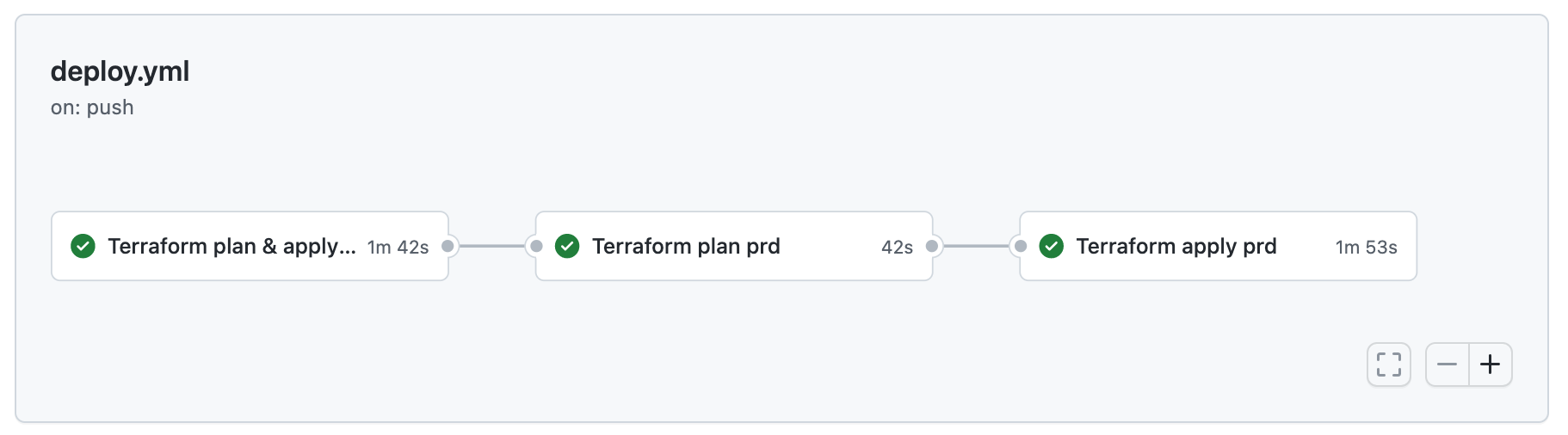
CI/CD
Development
Code Standards
Automated Tests
Manual Tests
- this tool cannot guarantee 100% protection against subdomain takeover
- it currently only scans Amazon Route53 and Cloudflare, and only checks a limited number of takeover types
- vulnerable domains in Google Cloud DNS can be detected by Domain Protect for GCP