HExHTTP is a tool designed to perform tests on HTTP headers and analyze the results to identify vulnerabilities and interesting behaviors.
pip install -r requirements.txt
./hexhttp.py -u 'https://target.tld/'docker build -t hexhttp:latest .
docker run --rm -it --net=host -v "$PWD:/hexhttp/" hexhttp:latest -u 'https://target.tld/'usage: hexhttp.py [-h] [-u URL] [-f URL_FILE] [-H CUSTOM_HEADER] [-A USER_AGENT] [-F] [-a AUTH] [-b]
HExHTTP is a tool designed to perform tests on HTTP headers.
options:
-h, --help show this help message and exit
-u URL, --url URL URL to test [required]
-f URL_FILE, --file URL_FILE
File of URLs
-H CUSTOM_HEADER, --header CUSTOM_HEADER
Add a custom HTTP Header
-A USER_AGENT, --user-agent USER_AGENT
Add a custom User Agent
-F, --full Display the full HTTP Header
-a AUTH, --auth AUTH Add an HTTP authentication. Ex: --auth admin:admin
-b, --behavior Activates a simplified version of verbose, highlighting interesting cache behaviors
-t THREADS, --threads THREADS
Threads numbers for multiple URLs. Default: 10# Scan only one domain
» ./hexhttp.py -u 'https://target.tld/'
# Scan a list of domains with behavior feature
» ./hexhttp.py -b -f domains.lst
# Add custom User-Agent
» ./hexhttp.py -u 'https://target.tld/' --user-agent "User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64) Firefox/123.0-BugBounty"
# Use a custom Header and authentication
» ./hexhttp.py --header 'Foo: bar' --auth 'user:passwd' -u 'https://target.tld/'
# Loop on domains, grep for vulnerabilities only and send result with notify (from projectdiscovery)
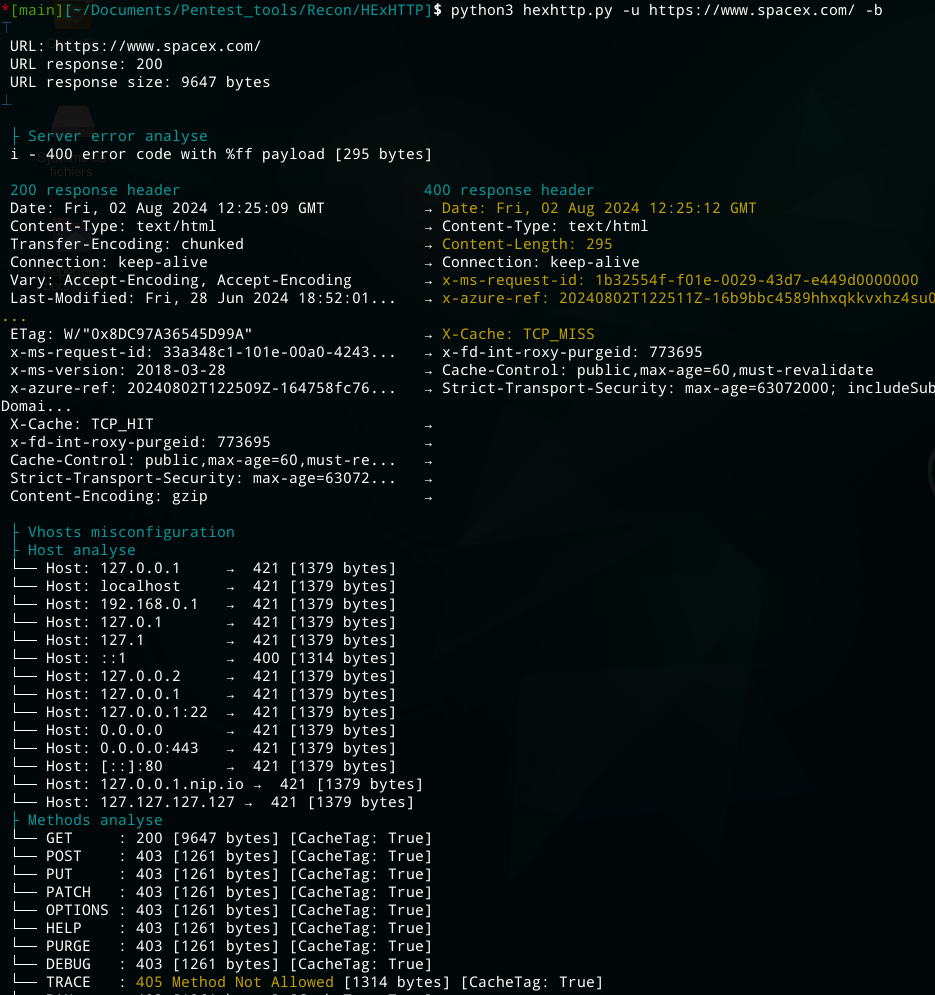
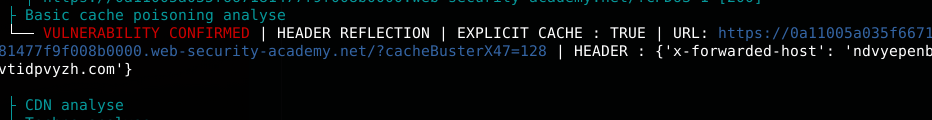
» for domain in $(cat domains.lst); do ./hexhttp.py -u "$domain" | grep -Eio "(INTERESTING|CONFIRMED)(.*)PAYLOAD.?:(.*){5,20}$" | notify -silent; doneYou can test this tool on the Web Security Academy's vulnerable labs, like this one. The expected result should be the same as above.
- Server Error response checking
- Localhost header response analysis
- Vhosts checking
- Methods response analysis
- HTTP version analysis [Experimental]
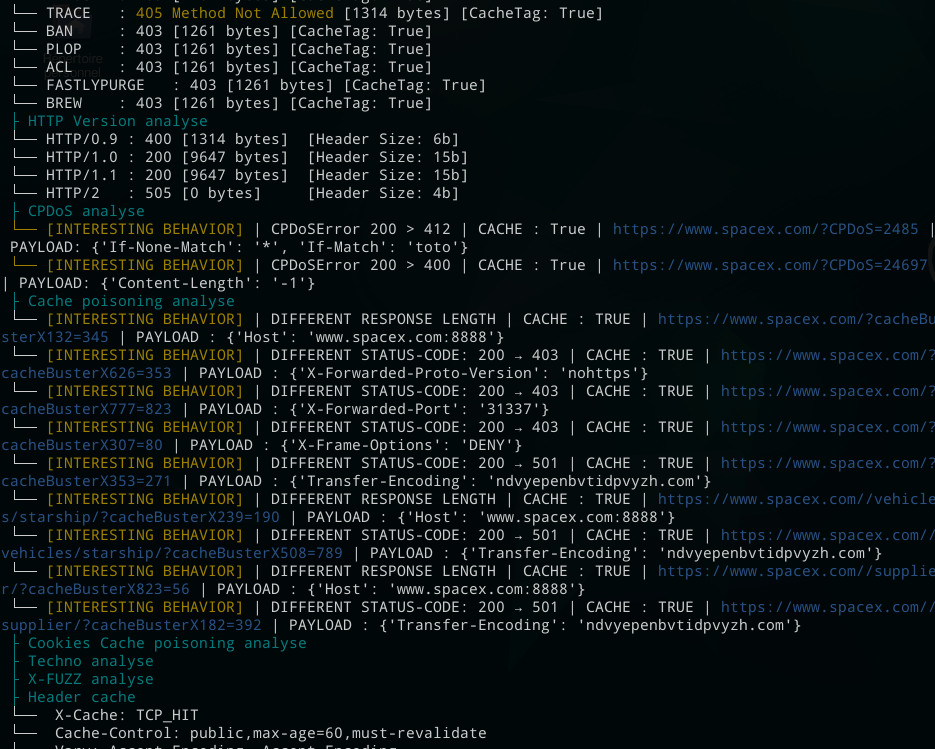
- CPDoS techniques
- Web cache poisoning
- Range poisoning/error (416 response error) [Experimental]
- Cookie Reflection
- CND/proxies Analysis (Envoy/Apache/Akamai/Nginx) [IP]
- Try with mobile user-agent [IP]
- Transfert-encoding tests (https://http.dev/transfer-encoding)
- Filter False Positive on WAF blocking [IP]
- Pypi package
- YWH HTTP Header Exploitation
- Cache Poisoning at Scale
- abusing http hop-by-hop request headers
- Web Cache Entanglement: Novel Pathways to Poisoning
- Practical Web Cache Poisoning
- Exploiting cache design flaws
- Responsible denial of service with web cache poisoning
- CPDoS.org
- Autopoisoner
- [Rachid.A research] (https://zhero-web-sec.github.io/research-and-things/nextjs-and-cache-poisoning-a-quest-for-the-black-hole)
Pull requests are welcome. Feel free to contribute to this tool and make improvements!