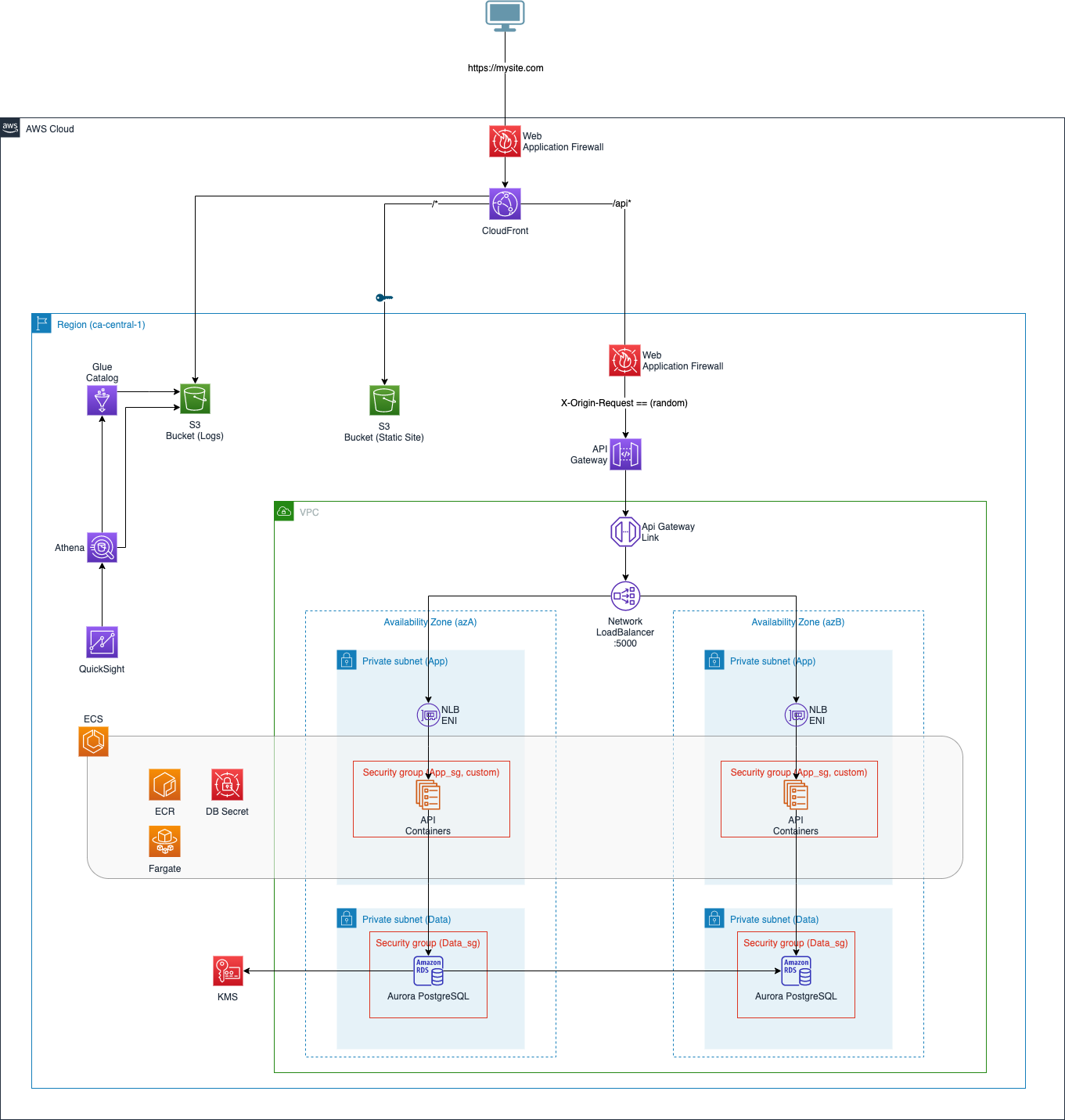
This CDK sample application deploys the following architecture that is compatible with the default configuration of the ASEA.
-
Update the
applicationPrefixNamein .\cdk.json -
Review the parameters in the bin\aws.ts folder:
new SEASampleAppStack(app, `${Prefix}+Stack`, {
env: {
account: "", //The AWS Account ID where this stack will be deployed
region: "ca-central-1", //Primary region
},
vpcId: "vpc-", //The VPC ID
appSubnetIds: ["subnet-", "subnet-"], //App Subnet IDs (default SEA architecture)
appSecurityGroup: "sg-", //App Security Group ID (default SEA architecture)
dataSubnetIds: ["subnet-", "subnet-"], //Data Subnet IDs (default SEA architecture)
dataSecurityGroup: "sg-", //Data Security Group ID (default SEA architecture)
tags: {
"Application": "Sample Demo"
},
prefix: Prefix,
dbName: "", //DBName to be used for initial Aurora PostgreSQL database
staticSiteBuildPath: "", //Path to the /dist folder of a static site
apiContainerPath: "" //Path to the folder to the containerized API. The dockerfile should exist at this location.
});
- Install project dependencies
This project requires node > 14 and Docker.
npm install
- Build the project
npm run build
- Bootstrap your SEA account
cdk bootstrap --toolkit-stack-name devcdktoolkit
- Deploy the stack
cdk deploy --toolkit-stack-name devcdktoolkit
- CloudFront WAF The CloudFront WAF is not configured as part of this automation because of SCP restrictions on CloudFormation in us-east-1. The CloudFront WAF must be configured in us-east-1
npm run buildcompile typescript to jscdk deploydeploy this stack to your default AWS account/regioncdk diffcompare deployed stack with current statecdk synthemits the synthesized CloudFormation template
Follow the instructions here for one option to securely access the RDS databse.