Using the Application API, you can rotate your APS applications' secrets automatically.
Typically, code you adapt from this sample would be deployed to an environment that can run jobs on a regular schedule, such as AWS Lambda, Azure Functions, or a server with cron.
- APS credentials
- Node.js (Long Term Support version is recommended)
- Command-line terminal such as PowerShell or bash (should already be available on your system)
We recommend using Visual Studio Code which, among other benefits, provides an integrated terminal as well.
- Clone this repository:
git clone https://github.com/autodesk-platform-services/application-management-api-sample - Go to the project folder:
cd application-management-api-sample - Install Node.js dependencies:
npm install - Open the project folder in a code editor of your choice (Visual Studio Code)
- Replace
<client-id>and<client-secret>with your APS Client ID and Client Secret in secrets.json
"CLIENT_ID": "<YOUR CLIENT_ID>",
"CLIENT_SECRET": "<YOUR CLIENT_SECRET>"- run
npm start
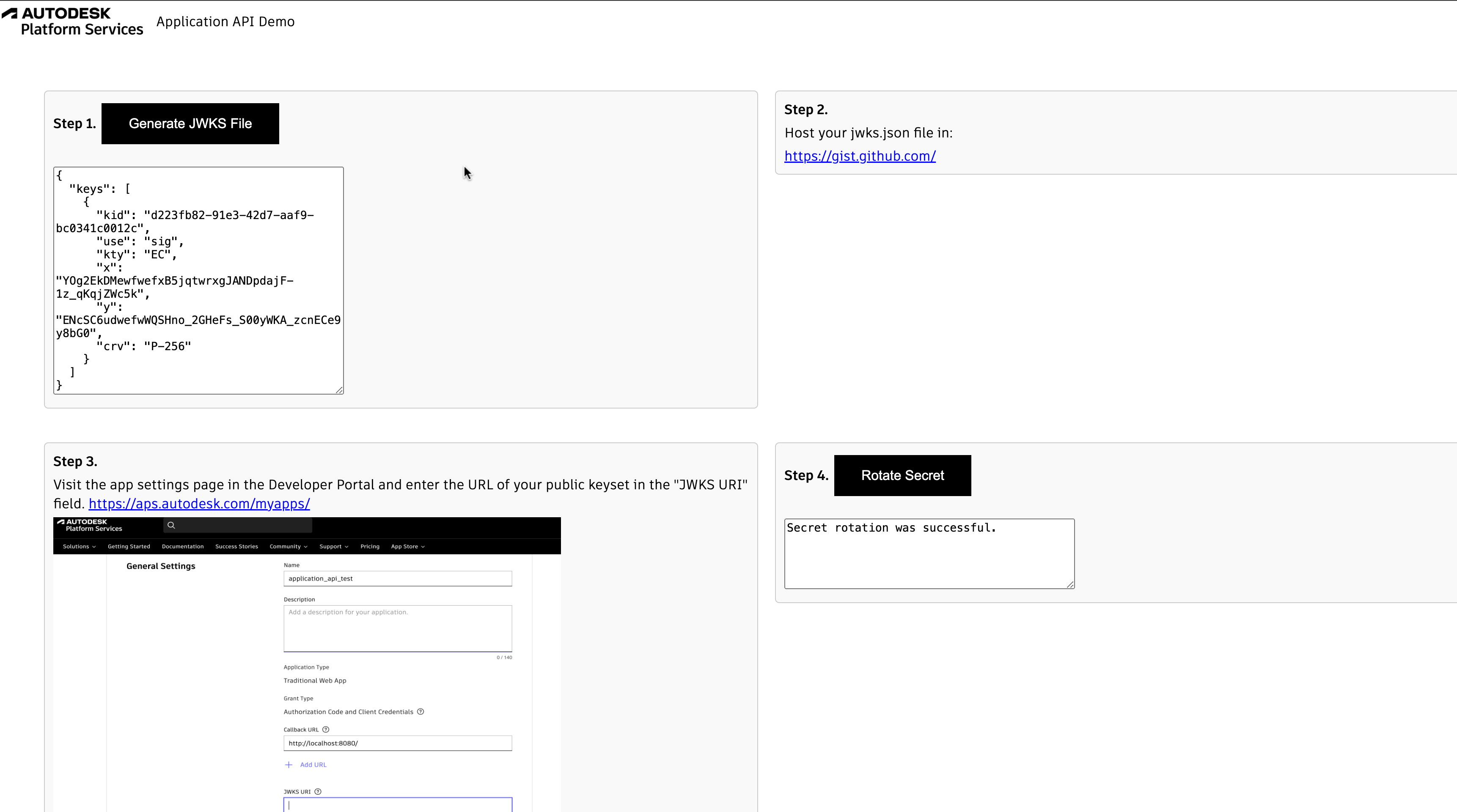
- Click on create keypair.js button to create a new key pair.
- The previous step will create a
jwks.jsonfile. Upload this file to your server (for testing purposes, a simple way to host a text file is on gist.github.com). How you choose to host your public keyset is up to you, but the keyset must be publicly accessible on the internet and your server must respond with raw JSON. Copy the raw json. - Visit the app settings page in the Developer Portal and enter the URL of your public keyset(raw json) in the "JWKS URI" field. Note:- Please make sure that you select Application Management API from the list of APIs dropdown list.
- Add your application's
client_idandclient_secretto the secret manager (if you have not yet customized the mock secrets manager, you will do this by editingsecrets.json).
Click on rotate secret buttonThis will rotate the secret and store the new value.
This code is intended as a simplified example; it will need modification to integrate smoothly with your deployments and avoid downtime.
In a production environment, it's strongly recommended that you do not use the mock secrets manager provided in this sample.
You can customize the file lib/secrets-manager.js to make calls to a real secrets manager, such as AWS Secrets Manager, Azure Key Vault, or comparable device.
In order to avoid downtime during rotation, your application will need several additional features:
- Logic to handle two client_secret values during the switchover. When requesting access_tokens, the app should try one value, and if that fails, try the second.
- Prior to committing the rotation, the rotation script needs to wait for the application to become aware of the new secret. This could be done by sending a webhook, or a simple time delay if the application is regularly polling the secrets manager.
The sample includes code to generate keypairs and signatures using the node.js jose library. This is sufficient for many uses, however The file lib/key-management.js can be customized to use an external key management service if desired. Products such as AWS KMS, Azure Key Vault, or a hardware security module (HSM) have the additional advantage that private keys cannot be exported.
Please contact us via https://forge.autodesk.com/en/support/get-help.
This sample is licensed under the terms of the MIT License. Please see the LICENSE file for more details.