oc new-app --name guise-cmline https://github.com/arslankhanali/GuiseAI-Openshift
oc expose svc guise-cmlin
oc delete all -l app=guise-cmline
- Install pipeline operator
- Create pipeline instance
- Create workspace
- workspace = edge-workspace
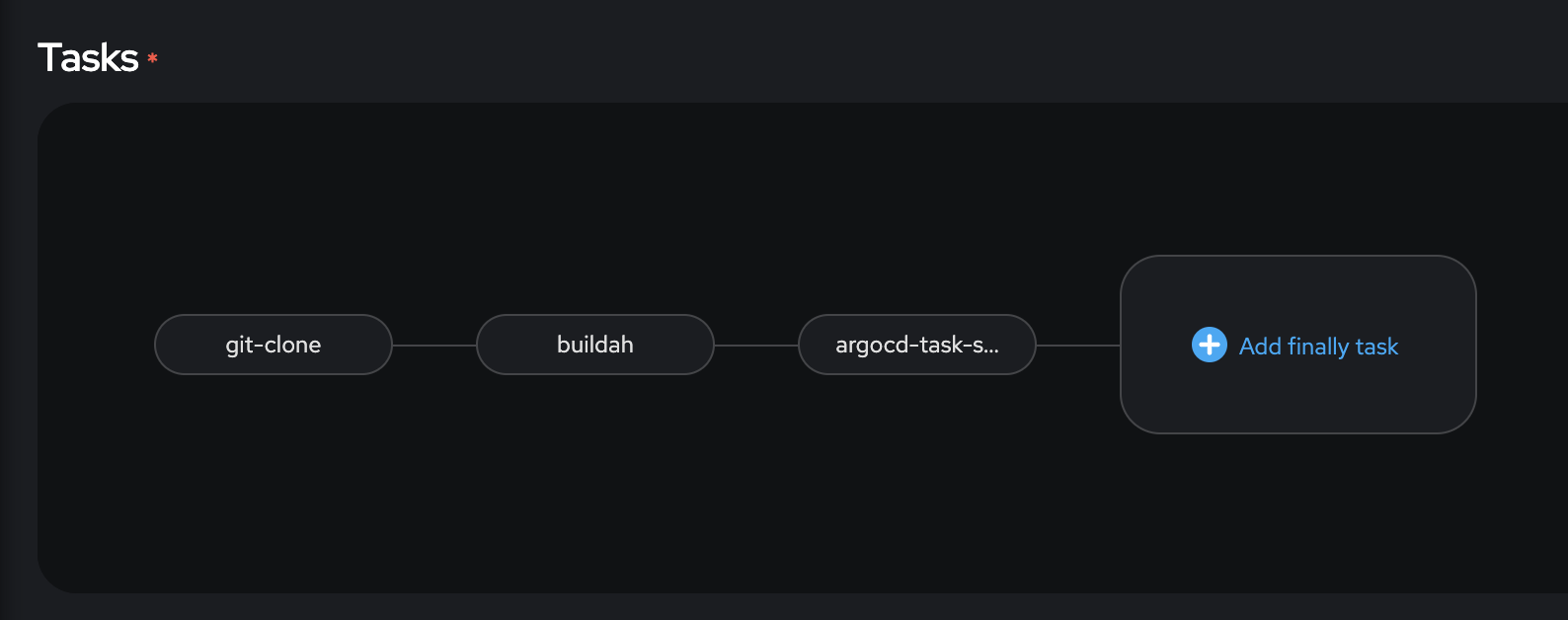
- git clone
- display name = git-clone
- url = https://github.com/arslankhanali/GuiseAI-Openshift
- workspace = edge-workspace
- buildah
- display name = buildah
- IMAGE = quay.io/arslankhanali/guise
- workspace = edge-workspace
- Create a secret to access quay.io to push to it
- https://tekton.dev/docs/pipelines/auth/#configuring-basic-auth-authentication-for-docker
-
apiVersion: v1 kind: Secret metadata: name: basic-user-pass annotations: tekton.dev/docker-0: https://quay.io # Described below type: kubernetes.io/basic-auth stringData: username: arslankhanali password: <pass>
- Give service account 'pipeline' access to the secret
- edit yaml
-
secrets: - name: pipeline-dockercfg-fgppj - name: basic-user-pass
- Start
- Choose VolumeClaimTemplate
- Build using manifest folder
- Install gitops operator
- Create argocd instance
- edit yaml. In line 209
-
rbac: - defaultPolicy: 'role:admin'
- Login to argo cd using the route
- Create a project
- App name = <>
- project = default
- repo url = https://github.com/arslankhanali/GuiseAI-Openshift
- path = manifest
- Sync policy = automatic
- destination url = https://kubernetes.default.svc
- namespace =
- Test
- Delete the app
- oc delete all -l app=guiseai
- See in Argo cd UI that the components are redeployed immediatly
- Try with both self heal enabled and disabled.
- With disabled, since service is not deployed, the route deployment will break
- With enabled, route will be exposed automatically once the service is up
- Delete the app
curl -sSL -o argocd-linux-amd64 https://github.com/argoproj/argo-cd/releases/latest/download/argocd-linux-amd64
sudo install -m 555 argocd-linux-amd64 /usr/local/bin/argocd
rm argocd-linux-amd64- Login to cluster with Argocd installed and get the password for argo cd
-
export ARGOCD_PASSWORD=$(oc get secret <argocd-cluster> -n <user2> -o jsonpath='{.data.admin\.password}' | base64 -d) echo $ARGOCD_PASSWORD # Another way to get password is by UI. Go to Developer->Secrets. Look for: # Name= argocd-cluster (name might be different for you) # Type= Opaque # Size= 1 # Reveal values -> copy admin.password #Test password by logging in like:- #argocd login argocd-server-user2.apps.anomaly-cluster.rqdu.p1.openshiftapps.com #username: admin #password: $ARGOCD_PASSWORD
- Login 'as admin' to remote cluster where you want to deploy argocd service account
When getting certificate error for RHPDS use '--insecure-skip-tls-verify=true' flag while logging in
-
argocd login <argocd-server-user2.apps.anomaly-cluster.rqdu.p1.openshiftapps.com> username: admin password: $ARGOCD_PASSWORD kubectl config get-contexts -o name argocd cluster add <context-name-from-previous-cmd>
- Confirm in argo cd UI settings/clusters that a new cluster has been added
- Choose "argocd-task-sync-and-wait" task in pipeline
- application-name = guiseai
- revision = HEAD
- flags = --insecure
- Apply 'usage' from https://hub.tekton.dev/tekton/Task/argocd-task-connect-repo/0.1
- I manually added Secret named 'argocd-env-secret'. Give it your argo username and password for admin account.
- Make sure 'argocd-env-configmap' Configmap is created
- It will also create a test 'argocd-pipeline-test' Pipeline. You don't have to use it. Use it to test