This guide explains how to provision an IoT Edge 1.2 via DPS, using an Identity Certificate dynamically issued by a CA via EST, with all the keys securely stored in an HSM implemented with a TPM and PKCS11.
All the required components (including a simulated TPM if needed) are installed running few scripts included in this repo.
Samples in this repo are for demonstration purposes only! This is not a guidance or best practices on IoT Edge security.
Install git if you haven't it:
sudo apt-get install git -yGrab the scripts from this repo:
cd ~
git clone https://github.com/arlotito/iot-edge-1.2-tpm.git
cd iot-edge-1.2-tpm/scripts
chmod +x *.shOnce you have the scripts:
- install using either a one-click or step-by-step approach:
- one-click deployment on Azure: you will get an Ubuntu 18.04 VM ready to go
- step-by-step installation on your own environment (physical or virtual machine, either x86 or ARM)
- troubleshoot if needed
- experiment
If everything went fine, you should now have an IoT Edge provisioned via DPS, using an Identity Certificate dynamically issued by a CA via EST, with private keys securely stored in the TPM/PKCS11.
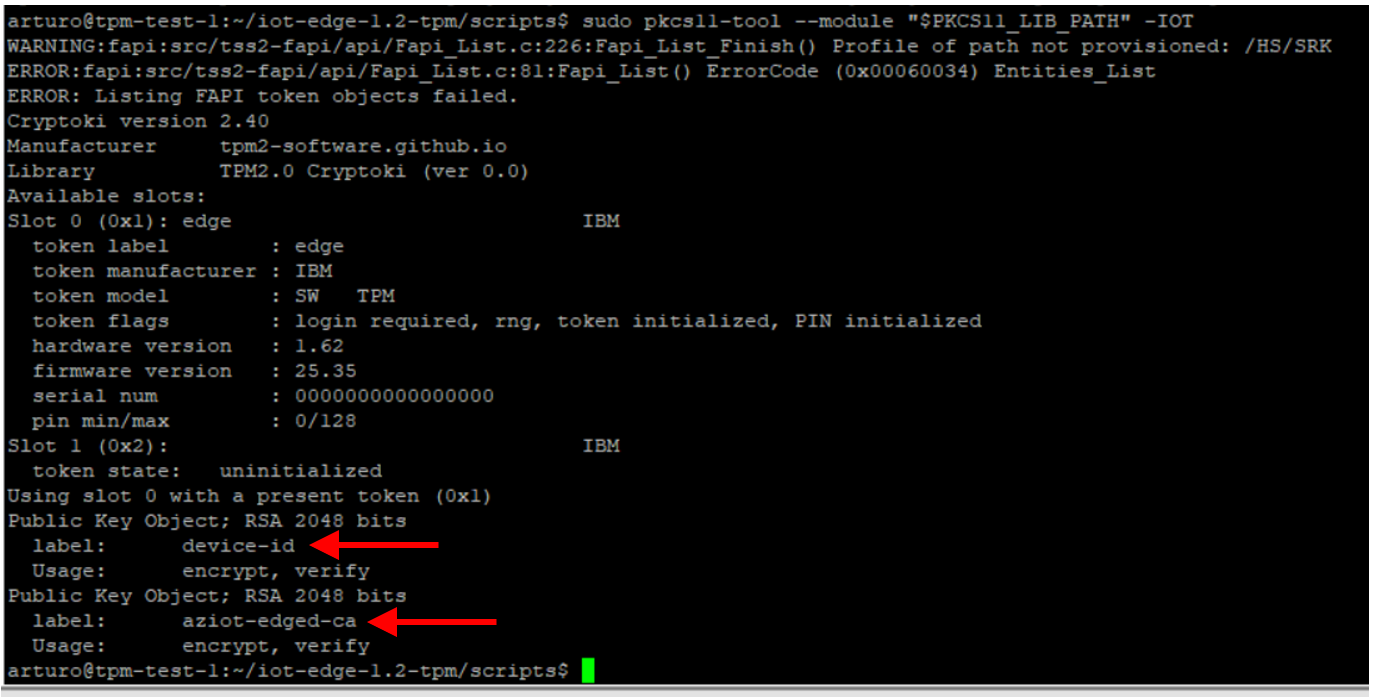
If you want, you can now inspect the content of the PKCS11 store and see the private keys generated by IoT Edge:
export TPM2_PKCS11_STORE='/opt/tpm2-pkcs11'
export PKCS11_LIB_PATH='/usr/local/lib/libtpm2_pkcs11.so'
sudo pkcs11-tool --module "$PKCS11_LIB_PATH" -IOTNOTE: the 'pkcs11-tool' is installed by script 3-install-pkcs11-tool.sh
...and make sure you have 'device-id' and 'aziot-edged-ca':
If you don't see any key or just the 'device-id', try with:
sudo iotedge system reprovisionLook at this for additional troubleshooting.
This guide has been tested on:
- x86:
- Ubuntu 18.04, both a physical x86 machine and virtual machine, using a simulated TPM
- ARM:
- raspberry pi 4 with Raspberry OS 32bit (which is based on Debian 10 Buster)
- with a simulated TPM
- with an HW Infineon Optiga SLB9670 TPM 2.0
- raspberry pi 4 with Raspberry OS 32bit (which is based on Debian 10 Buster)