A POC ransomware detector for CMPT733 project
- Python3.5+
and some other requirements here:
sudo apt install iotop python3-pip python3-tk python3-pil python3-pil.imagetk libgeoip1 libgeoip-dev geoip-binSetting up the environment:
# Creating the virtual environment
python3 -m venv .env
# Activating the virtual environment
source .env/bin/activateInstalling dependencies:
(.env) pip install -r requirements.txtSetting up pre-commit hooks:
(.env) pre-commit installUsing the program to run detectors can be done like so:
python3 main.py -d <DetectorName>and for a full menu of command line options, run:
python3 main.py -h- io-detector: Detects ranosmware by looking at high file I/O
- sensory-detector: Detects ransomware by creating sensor files
- detectors: Where all the detector classes are kept as a single point of control
- tests: Test scripts. Can be invoked via the
tester.pyin the root directory
- First, make a new folder if there are utilities for this detector in the root directory.
- Afterwards, create a
<NameHere>Detector.pyfile indetectors/and define therun(self, ...)function! - Lastly, add the detector class name in
detectors/__init__.pyto allow the detector to be called from the main program!
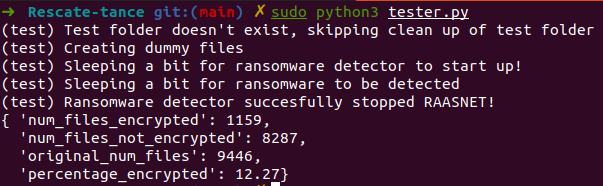
To run tests, make sure the path is in the correct location first for config.yml, then run:
sudo python3 tester.pyThis command will run the test in tests/raasnet_test.py. The test includes:
- Setting up dummy files recursively for testing
- Setting up the signature detector
- Running the signature detector
- Running the ransomware
- Stopping the ransomware
- Providing benchmarks
A sample run is shown below:
DO NOT RUN THE PAYLOADS IN tests/ransomware/ DIRECTLY ON YOUR LOCAL MACHINE!!. You will brick your computer and cause all your files to be encrypted! (We have provided a keys.txt file that will be output once the payload is run, but this is still too dangerous!!)