This project aims to simplify the creation and loading of policy factories. It includes a small set of Factories to serve as a starting point and as an example.
For a customer engagement, it's strongly suggested you clone this repository and use a customer specific branch. This will allow you to generate factories to meet customer specific needs.
- How To
- Reference
This project includes a number of pre-constructed factories. Default templates include the following:
- Authenticators
- AuthnJwt (using JWKS)
- AuthnJwt (using public keys)
- AuthnOIDC
- Connections
- Database
- Core
- Grant
- Group
- Host
- Policy
- User
- Variable
To load the default set of Factories into Conjur (running via Conjur Intro), run:
CONJUR_URL=https://localhost ACCOUNT=demo CONJUR_USERNAME=admin bin/load defaultTo load Factories into a local Conjur development environment:
API_KEY=<api-key> CONJUR_URL=<http://localhost:3000> ACCOUNT=cucumber CONJUR_USERNAME=admin bin/loadThis quickstart assumes you've cloned this repository locally, and are calling commands from inside this project directory.
As an example, let's create a Policy Factory that simplifies the process of storing API credentials for various services that offer APIs. Before starting, let's define what we want:
- include two variables,
url, andapi-key - create a group with permission to see and retrieve these variables
- create an admin group to administer these credentials
First, let's generate the necessary factory stubs:
bin/create api_credentialsThis command will create two files (config.json and policy.yml in lib/templates/default/api_credentials/v1).
Open the API Policy Factory config file: lib/templates/default/api_credentials/v1/config.json. It will look like the following:
{
"title": "",
"description": "",
"variables": {
"variable-1": {
"required": true,
"description": ""
},
"variable-2": {
"description": ""
}
}
}Update it to the following:
{
"title": "API Credentials Template",
"description": "Data related to external APIs",
"variables": {
"url": {
"required": true,
"description": "API URL"
},
"api-key": {
"required": true,
"description": "API authentication key"
}
}
}Save and close the config.json file.
Next, open the Policy Factory policy file: lib/templates/default/api_credentials/v1/policy.yml and update it to the following:
- !group consumers
- !group administrators
# consumers can read and execute
- !permit
resource: *variables
privileges: [ read, execute ]
role: !group consumers
# administrators can update (and read and execute, via role grant)
- !permit
resource: *variables
privileges: [ update ]
role: !group administrators
# administrators has role consumers
- !grant
member: !group administrators
role: !group consumersSave the changes to policy.yml.
Note: in the above policy *variables will refer to the variables defined in config.json.
*In order to load Policy Factories, your role needs permission to create policy in the root namespace. The following commands use a leader running via the Conjur Intro project.
*
Run the following command to load our API Policy Factory:
CONJUR_URL=https://localhost ACCOUNT=demo CONJUR_USERNAME=admin bin/loadNote: you'll be prompted for the admin user password.
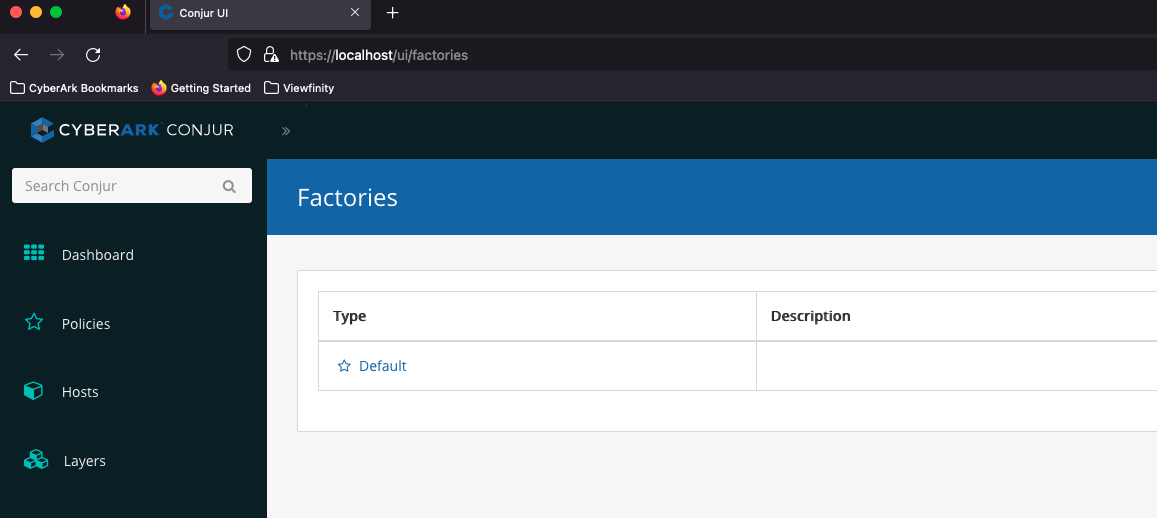
In the UI, navigate to the Policy Factories page: ex. https://localhost/ui/factories.
Note: this page is not accessable in the navigation. Once the feature reaches GA, it will be added.
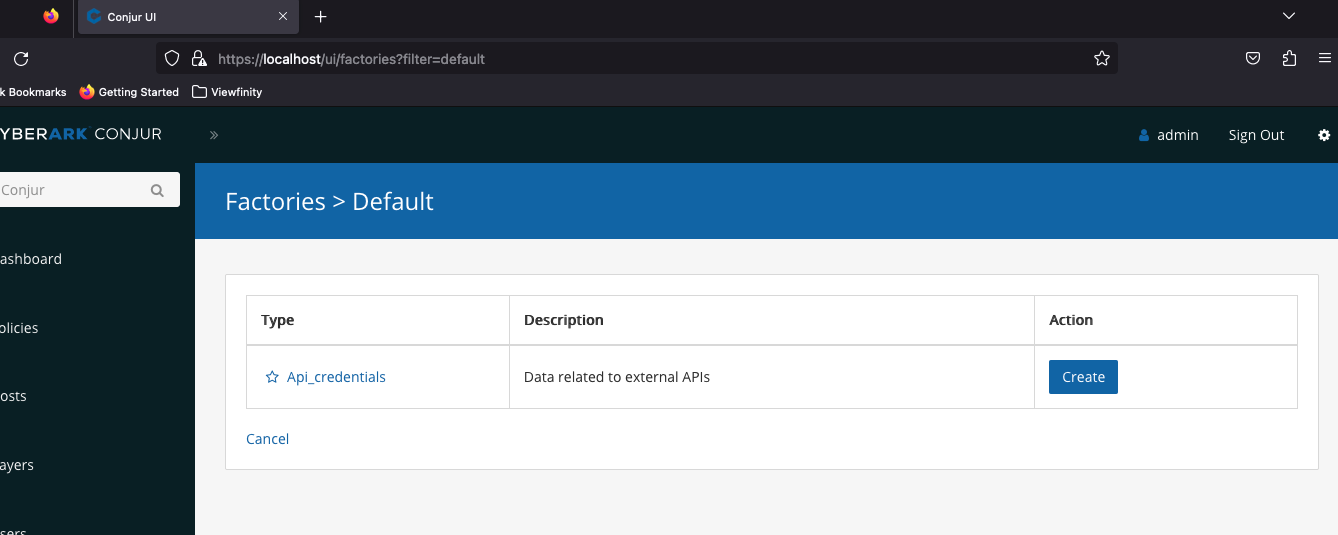
Click Default
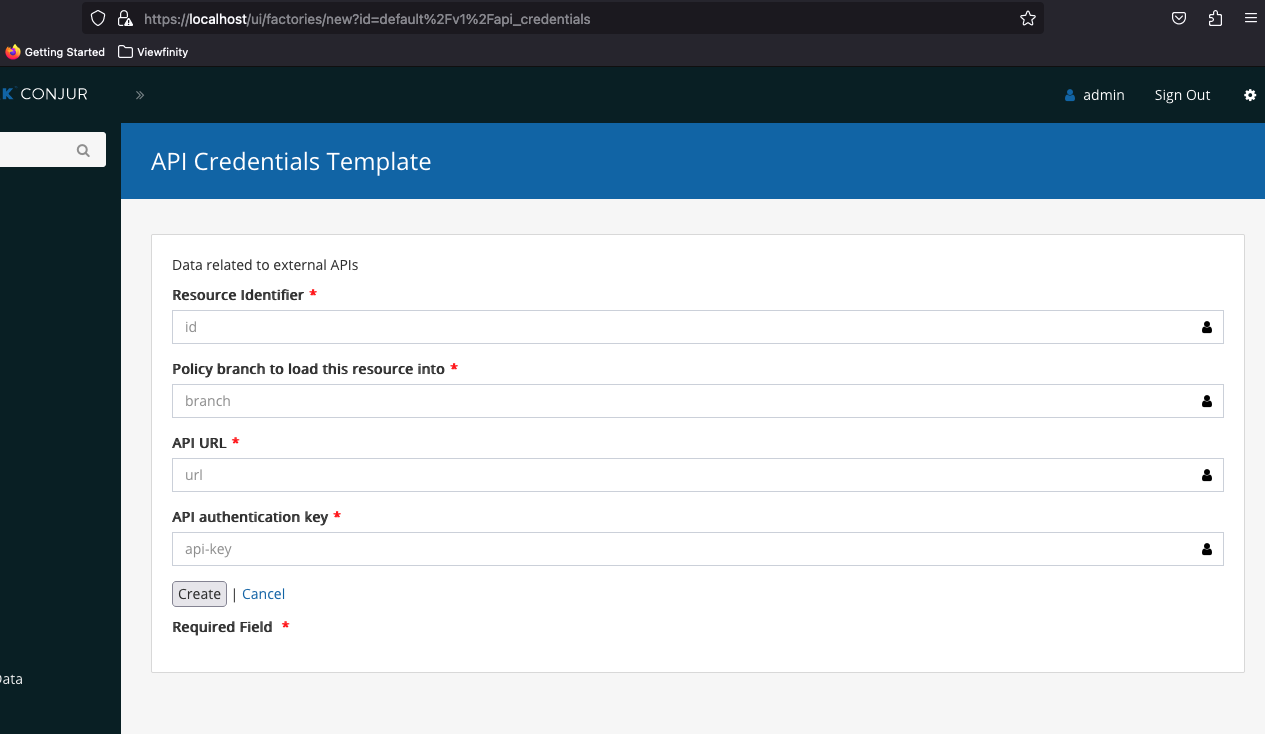
Click the blue Create button
To create a new set of API credentials with our factory, fill the fields in with the following:
Resource Identifier- GitLabPolicy Branch- rootAPI URL- https://mydomain.gitlab.comAPI Key- supersecret123-key
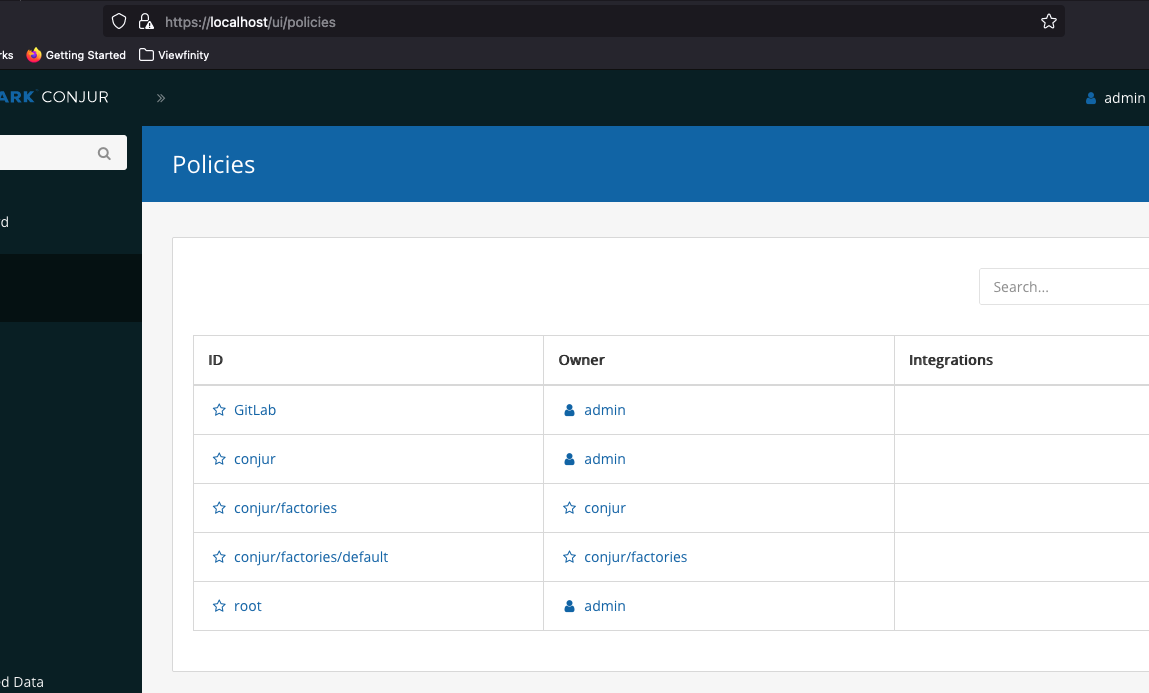
After clicking the Create button, navigate to the policies page: /ui/policies
Notice we now have a policy GitLab in our list:
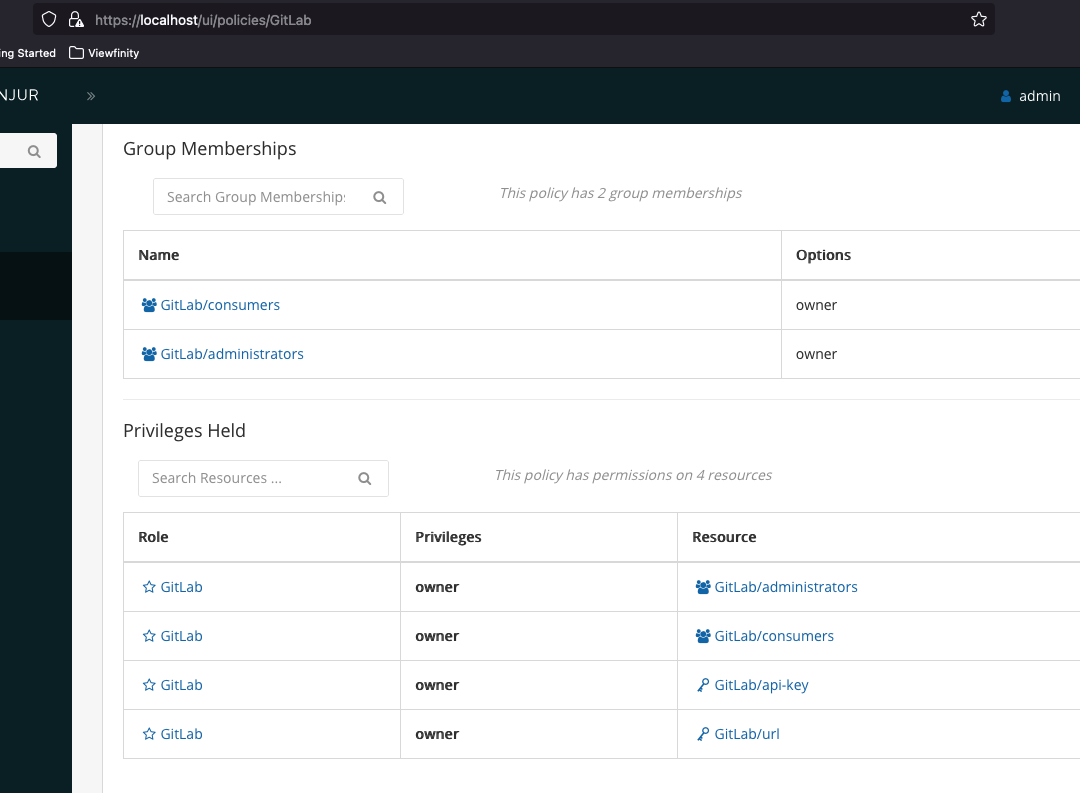
Clicking on the GitLab Policy, we can see the details, including our groups and variables.