Kubescape is a K8s open-source tool providing a multi-cloud K8s single pane of glass, including risk analysis, security compliance, RBAC visualizer and image vulnerabilities scanning. Kubescape scans K8s clusters, YAML files, and HELM charts, detecting misconfigurations according to multiple frameworks (such as the NSA-CISA , MITRE ATT&CK®), software vulnerabilities, and RBAC (role-based-access-control) violations at early stages of the CI/CD pipeline, calculates risk score instantly and shows risk trends over time. It became one of the fastest-growing Kubernetes tools among developers due to its easy-to-use CLI interface, flexible output formats, and automated scanning capabilities, saving Kubernetes users and admins’ precious time, effort, and resources. Kubescape integrates natively with other DevOps tools, including Jenkins, CircleCI, Github workflows, Prometheus, and Slack, and supports multi-cloud K8s deployments like EKS, GKE, and AKS.
curl -s https://raw.githubusercontent.com/armosec/kubescape/master/install.sh | /bin/bash
kubescape scan --submit --enable-host-scan
Kubescape is an open source project, we welcome your feedback and ideas for improvement. We’re also aiming to collaborate with the Kubernetes community to help make the tests themselves more robust and complete as Kubernetes develops.
Click 👍 if you want us to continue to develop and improve Kubescape 😀
We invite you to our team! We are excited about this project and want to return the love we get.
Want to contribute? Want to discuss something? Have an issue?
- Open a issue, we are trying to respond within 48 hours
- Join us in a discussion on our discord server!
- Overview
- How To Secure Kubernetes Clusters With Kubescape And Armo
- Scanning Kubernetes YAML files
- Scan Kubescape on an air-gapped environment (offline support)
- Managing exceptions in the Kubescape SaaS version
Requires powershell v5.0+
iwr -useb https://raw.githubusercontent.com/armosec/kubescape/master/install.ps1 | iexNote: if you get an error you might need to change the execution policy (i.e. enable Powershell) with
Set-ExecutionPolicy RemoteSigned -scope CurrentUser-
brew tap armosec/kubescape -
brew install kubescape
| flag | default | description | options |
|---|---|---|---|
-e/--exclude-namespaces |
Scan all namespaces | Namespaces to exclude from scanning. Recommended to exclude kube-system and kube-public namespaces |
|
--include-namespaces |
Scan all namespaces | Scan specific namespaces | |
-s/--silent |
Display progress messages | Silent progress messages | |
-t/--fail-threshold |
100 (do not fail) |
fail command (return exit code 1) if result is above threshold | 0 -> 100 |
-f/--format |
pretty-printer |
Output format | pretty-printer/json/junit/prometheus |
-o/--output |
print to stdout | Save scan result in file | |
--use-from |
Load local framework object from specified path. If not used will download latest | ||
--use-artifacts-from |
Load artifacts (frameworks, control-config, exceptions) from local directory. If not used will download them | ||
--use-default |
false |
Load local framework object from default path. If not used will download latest | true/false |
--exceptions |
Path to an exceptions obj. If not set will download exceptions from Armo management portal | ||
--controls-config |
Path to a controls-config obj. If not set will download controls-config from ARMO management portal | ||
--submit |
false |
If set, Kubescape will send the scan results to Armo management portal where you can see the results in a user-friendly UI, choose your preferred compliance framework, check risk results history and trends, manage exceptions, get remediation recommendations and much more. By default the results are not sent | true/false |
--keep-local |
false |
Kubescape will not send scan results to Armo management portal. Use this flag if you ran with the --submit flag in the past and you do not want to submit your current scan results |
true/false |
--account |
Armo portal account ID. Default will load account ID from configMap or config file | ||
--kube-context |
current-context | Cluster context to scan | |
--verbose |
false |
Display all of the input resources and not only failed resources | true/false |
Scan a running Kubernetes cluster with nsa framework and submit results to the Kubescape SaaS version
kubescape scan framework nsa --submit
Scan a running Kubernetes cluster with MITRE ATT&CK® framework and submit results to the Kubescape SaaS version
kubescape scan framework mitre --submit
Scan a running Kubernetes cluster with a specific control using the control name or control ID. List of controls
kubescape scan control "Privileged container"
kubescape scan framework nsa --include-namespaces development,staging,production
kubescape scan framework nsa --exclude-namespaces kube-system,kube-public
Scan local yaml/json files before deploying. Take a look at the demonstration
kubescape scan framework nsa *.yaml
kubescape scan framework nsa https://github.com/armosec/kubescape
kubescape scan framework nsa --verbose
kubescape scan framework nsa --format json --output results.json
kubescape scan framework nsa --format junit --output results.xml
Output in prometheus metrics format - Contributed by @Joibel
kubescape scan framework nsa --format prometheus
kubescape scan framework nsa --exceptions examples/exceptions/exclude-kube-namespaces.json
Scan Helm charts - Render the helm chart using helm template and pass to stdout
helm template [NAME] [CHART] [flags] --dry-run | kubescape scan framework nsa -
e.g.
helm template bitnami/mysql --generate-name --dry-run | kubescape scan framework nsa -
It is possible to run Kubescape offline!
First download the framework and then scan with --use-from flag
- Download and save in file, if file name not specified, will save in
~/.kubescape/<framework name>.json
kubescape download framework nsa --output nsa.json
- Scan using the downloaded framework
kubescape scan framework nsa --use-from nsa.json
You can also download all artifacts to a local path and then load them using --use-artifacts-from flag
- Download and save in local directory, if path not specified, will save all in
~/.kubescape
kubescape download artifacts --output path/to/local/dir
- Scan using the downloaded artifacts
kubescape scan framework nsa --use-artifacts-from path/to/local/dir
Scan Periodically using Helm - Contributed by @yonahd
You can scan your cluster periodically by adding a CronJob that will repeatedly trigger kubescape
helm install kubescape examples/helm_chart/
Official Docker image quay.io/armosec/kubescape
docker run -v "$(pwd)/example.yaml:/app/example.yaml quay.io/armosec/kubescape scan framework nsa /app/example.yaml
Use the submit command if you wish to submit data manually
First, scan your cluster using the json format flag: kubescape scan framework <name> --format json --output path/to/results.json.
Now you can submit the results to the Kubaescape SaaS version -
kubescape submit results path/to/results.json
Kubescape can be built using:
python build.pyNote: In order to built using the above script, one must set the environment variables in this script:
- RELEASE
- ArmoBEServer
- ArmoERServer
- ArmoWebsite
Note: development (and the release process) is done with Go 1.17
- Clone Project
git clone https://github.com/armosec/kubescape.git kubescape && cd "$_"
- Build
go build -o kubescape .
- Run
./kubescape scan --submit --enable-host-scan
- Enjoy 🤪
- Clone Project
git clone https://github.com/armosec/kubescape.git kubescape && cd "$_"
- Build
docker build -t kubescape -f build/Dockerfile .
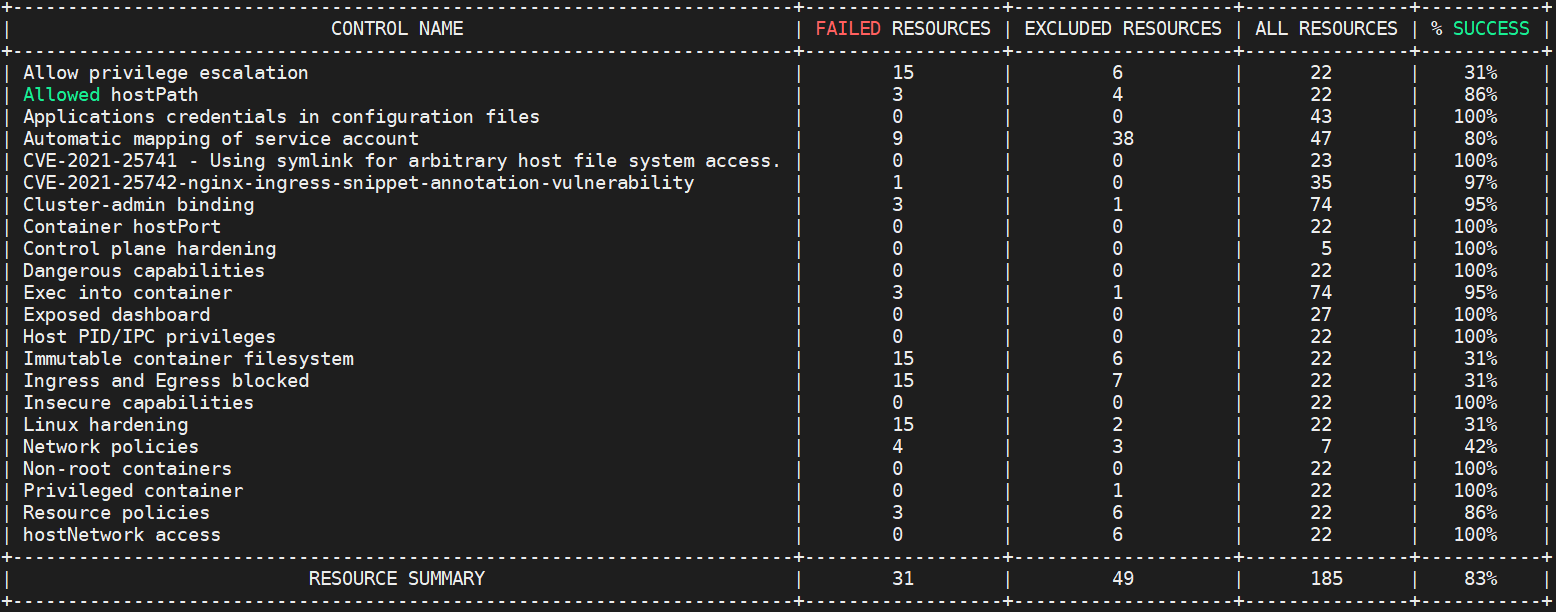
Kubescape is running the following tests according to what is defined by Kubernetes Hardening Guidance by NSA and CISA
- Non-root containers
- Immutable container filesystem
- Privileged containers
- hostPID, hostIPC privileges
- hostNetwork access
- allowedHostPaths field
- Protecting pod service account tokens
- Resource policies
- Control plane hardening
- Exposed dashboard
- Allow privilege escalation
- Applications credentials in configuration files
- Cluster-admin binding
- Exec into container
- Dangerous capabilities
- Insecure capabilities
- Linux hardening
- Ingress and Egress blocked
- Container hostPort
- Network policies
- Symlink Exchange Can Allow Host Filesystem Access (CVE-2021-25741)
Kubescape based on OPA engine: https://github.com/open-policy-agent/opa and ARMO's posture controls.
The tools retrieves Kubernetes objects from the API server and runs a set of regos snippets developed by ARMO.
The results by default printed in a pretty "console friendly" manner, but they can be retrieved in JSON format for further processing.
Kubescape is an open source project, we welcome your feedback and ideas for improvement. We’re also aiming to collaborate with the Kubernetes community to help make the tests themselves more robust and complete as Kubernetes develops.