Features • Supported commands • Installation • Usage • Documentation
secator is a task and workflow runner used for security assessments. It supports dozens of well-known security tools
and it is designed to improve productivity for pentesters and security researchers.
-
Curated list of commands
-
Unified input options
-
Unified output schema
-
CLI and library usage
-
Distributed options with Celery
-
Complexity from simple tasks to complex workflows
-
Customizable
secator integrates the following commands:
| Name | Description | Category |
|---|---|---|
| httpx | Fast HTTP prober. | http |
| cariddi | Fast crawler and endpoint secrets / api keys / tokens matcher. | http/crawler |
| gau | Offline URL crawler (Alien Vault, The Wayback Machine, Common Crawl, URLScan). | http/crawler |
| gospider | Fast web spider written in Go. | http/crawler |
| katana | Next-generation crawling and spidering framework. | http/crawler |
| dirsearch | Web path discovery. | http/fuzzer |
| feroxbuster | Simple, fast, recursive content discovery tool written in Rust. | http/fuzzer |
| ffuf | Fast web fuzzer written in Go. | http/fuzzer |
| h8mail | Email OSINT and breach hunting tool. | osint |
| dnsx | Fast and multi-purpose DNS toolkit designed for running DNS queries. | recon/dns |
| dnsxbrute | Fast and multi-purpose DNS toolkit designed for running DNS queries (bruteforce mode). | recon/dns |
| subfinder | Fast subdomain finder. | recon/dns |
| fping | Find alive hosts on local networks. | recon/ip |
| mapcidr | Expand CIDR ranges into IPs. | recon/ip |
| naabu | Fast port discovery tool. | recon/port |
| maigret | Hunt for user accounts across many websites. | recon/user |
| gf | A wrapper around grep to avoid typing common patterns. | tagger |
| grype | A vulnerability scanner for container images and filesystems. | vuln/code |
| dalfox | Powerful XSS scanning tool and parameter analyzer. | vuln/http |
| msfconsole | CLI to access and work with the Metasploit Framework. | vuln/http |
| wpscan | WordPress Security Scanner | vuln/multi |
| nmap | Vulnerability scanner using NSE scripts. | vuln/multi |
| nuclei | Fast and customisable vulnerability scanner based on simple YAML based DSL. | vuln/multi |
| searchsploit | Exploit searcher. | exploit/search |
Feel free to request new commands to be added by opening an issue, but please
check that the command complies with our selection criterias before doing so. If it doesn't but you still want to integrate it into secator, you can plug it in (see the dev guide).
Secator requires python >= 3.8 to install successfully. Run the following command to install the latest version:
pip3 install secatorBash one-liner
git clone https://github.com/freelabz/secator && sh ./secator/scripts/install.sh
Docker
docker pull freelabz/secator
Development build
git clone https://github.com/freelabz/secator
cd secator
python3 -m virtualenv -p python3 ~/.virtualenvs/secator
source ~/.virtualenvs/secator/bin/activate
pip3 install -e .
secator is designed to work with the latest version of all the tools it supports. Please make sure you are using the latest version of the tools you are using with secator.
A convenience utility is provided to install all tools:
secator u install... or to update specific tools:
secator u install <TASK_NAME>Please note that:
- this install method requires
aptso it will not work on distributions not supporting it. - this is tested merely on Ubuntu and some of these installs might not work on other distributions.
- ideally you update the tools yourself, and use
secatoras a convenient wrapper on top of them.
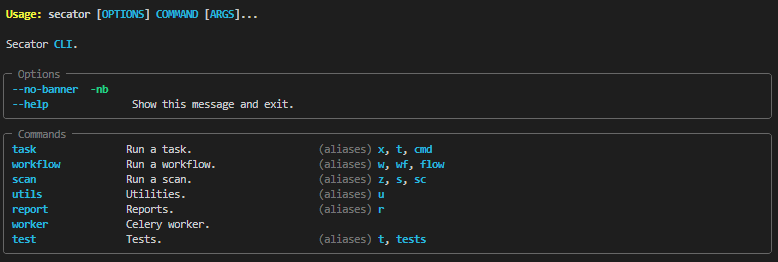
secator --helpRun a fuzzing task (ffuf):
secator x ffuf http://testphp.vulnweb.com/FUZZRun a url crawl workflow:
secator w url_crawl http://testphp.vulnweb.comRun a host scan:
secator s host mydomain.comand more... to list all tasks / workflows / scans that you can use:
secator x --help
secator w --help
secator s --helpTo go deeper with secator, check out:
- Our complete documentation
- Our getting started tutorial video
- Our Medium post
- Follow us on social media: @freelabz on Twitter and @FreeLabz on YouTube