A list of topics I speak about on the different conferences, including posts, videos, slides etc. I track resources on my own, so maybe I'm missing smth.
I'm working at @cossacklabs on security products that provide strong, usable cryptography for busy people. Many things are open source, i.e. Themis — the crypto library for storage and messaging in mobile, desktop, and web apps, or Acra — database proxy with intrusion detection.
I can assist you in protecting users data in your infrastructure, just drop me an email.
I share a lot about my engineering life on twitter as @vixentael, and on Medium.
Enjoy! 🔒
#mobile #security #crypto
Before we get really deep into protocols vulnerabilities: things you should remember designing your app flow from security point of view.
- UIKonf 18
Berlin, Germany, 13-16 May 2018
#mobile #security #ZKA
- Swift Aveiro
Aveiro, Portugal, 21-22 June 2018
#security #crypto #databases #notmobile #trust #infrastructures #separation-of-duties #echelonization
| slides | video gonna be soon |
|---|
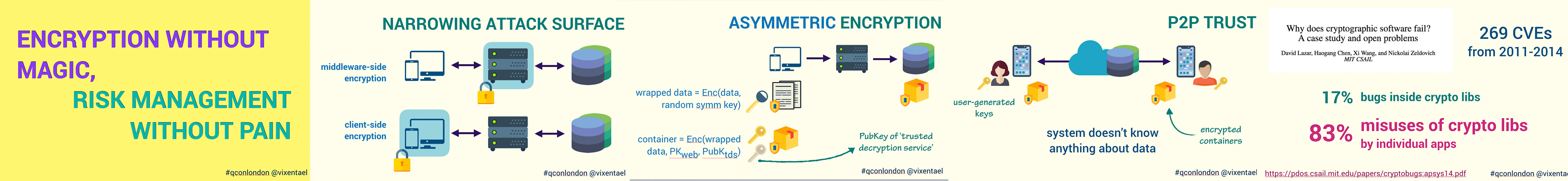
In-depth technical inquiry about cryptography in a wider context: how it helps to narrow more significant risks to controlled attack surfaces, enables managing the risk efficiently and elegantly, how tools and algorithms sit in a broader context of managing infrastructure-wide risks associated with handling sensitive data.
- What is attack surface, how cryptography helps to narrow it.
- Simple crypto-systems, but significant downsides.
- Middleware-side encryption: protecting data in web-based infrastructures.
- Client-side encryption: trust to mobile apps and code execution. E2EE. ZKA. ZKP.
- Echelonization, and traditional techniques.
Presented at:
- Security BSides Ukraine
Kyiv, Ukraine, 21 April 2018 - QCon London 18
London, UK, 5-7 March 2018
#security #crypto
| slides | video (ru) |
|---|
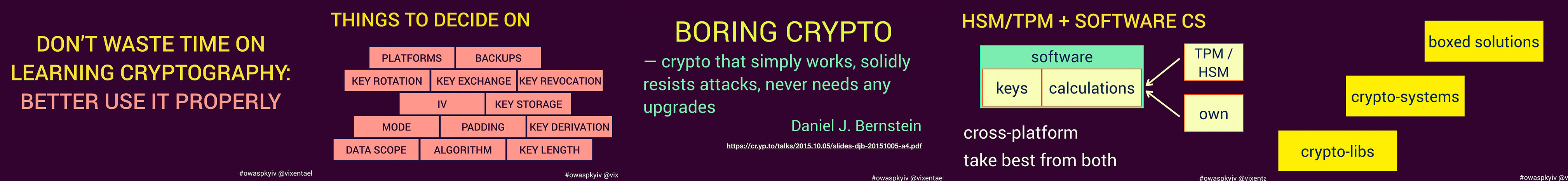
Crypto in our lives: why you shouldn’t spend time learning all the details of the crypto-algorithms. Typical mistakes you make using crypto in your products. How to avoid late night commits, but to code 'fast and boring' instead.
- The typical engineering workflow "we should protect the data, what shall we do", and possible mistakes.
- What is "boring crypto", what do we want from using crypto-products.
- Possible solutions: HSM / TPM / software crypto.
- How to select appropriate software crypto: libs, systems, containers.
- We want crypto to be similar to the Edison lamp: controllable and boring system.
Presented at:
-
Devexperience.ro
Iasi, Romania, 23 April 2018 -
OWASP Kyiv Meetup Winter 17
Kyiv, Ukraine, 2 December 2017
#security #blockchain
| slides | video (ru) |
|---|
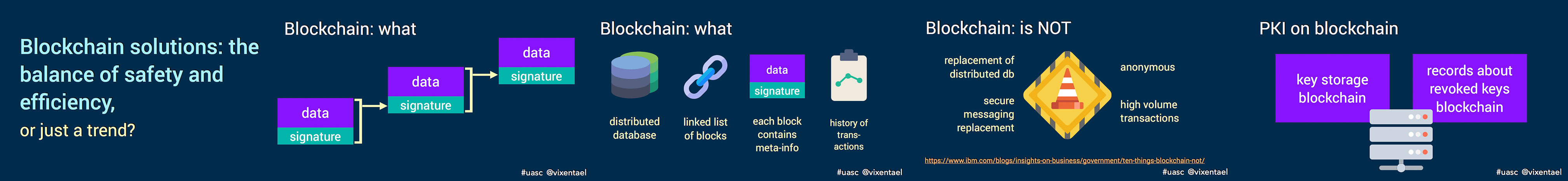
The security engineer's job is to choose the appropriate solutions for the problems and to apply them. Discussing blockchain regarding cryptography is rather boring: it is simple, and even some assumptions in high-level protocols do not cause protests.
I will talk about the other side - where blockchain looks like an optimal strategy, where it causes questions. We will walk through the risk&threats models, trust, and guarantees, to the experience of using blockchain in the real project (and what happened next).
Presented at:
- UA.SC 17
Kyiv, Ukraine, 18 October 2017
#security #mobile #zkp #zka
| slides | Mobiconf video (en) |
|---|
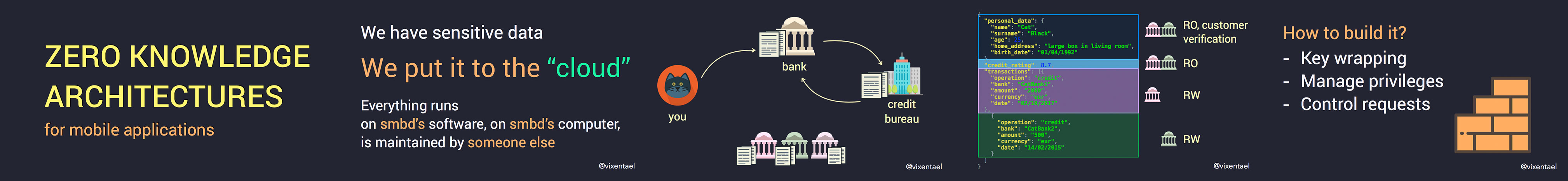
With intensifying threat access, snooping governments and insecure-internet-of-everything, the importance of zero-knowledge application architectures and end-to-end trust, for things more complicated than simple messaging, becomes more and more obvious for the app developers.
We will talk about real-world problems that ZKA fights against, learn typical cryptographic designs and progress in different spheres of ZKA. We will find out how to make data sharing, user collaboration on data in the cloud with your app provably secure.
Presented at:
-
DevFest Baltics 17
Riga, Latvia, 17 November 2017 -
SE Conf 17
Kyiv, Ukraine, 27-29 October 2017 -
MobiConf 17
Krakow, Poland, 5-6 October 2017
#ux #productdev #mobile #design
| slides | video |
|---|
This is a story from a designer @anatinge and a developer who worked together and built a product for people who really need it. It's all about working in a tight collaboration, conducting user research and user interviews, sharing tip & tricks about team working.
Presented at:
- ADDC 2017
Barcelona, 22-23 June 2017
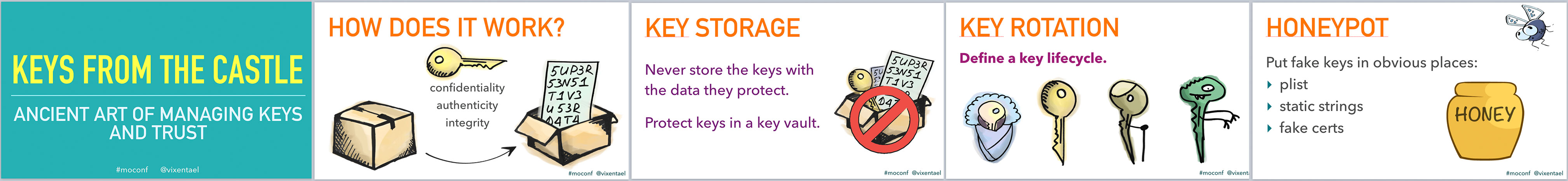
#security #keys #mobile #trust
| slides | AppBuilders video | CraftConf video |
|---|
We will talk about building trust. Trust is built around various trust tokens: keys, passwords, secrets, biometric properties, things you have and things you know. We will talk about what should you trust, how to establish and verify trust, how to share trustedly among different users. We will discuss technical aspects: key exchange, key trust, key derivation, channel trust, multi-factor authentications. I will try to make the audience understand how this huge universe of tools and algorithms serves just one purpose: letting the right guys in, keeping the wrong guys outside our magical castle. And fairies there should be!
>>> Read more in Medium post <<<
Presented at:
-
Mobile Optimized
Minsk, Belarus, July 14-15 2017 -
CraftConf 17
Budapest, Hungary, April 25-28, 2017 -
AppBuilders 17
Lausanne, Switzerland, April 24-25 2017
#security #mobile #kittens
| no slides | no video |
|---|
Summary talk for the newbies in security field.
Mobile platforms present both new threats and new opportunities for system security. This presentation will deal with modern approaches: how to protect data, which trusted relationships emerge with mobile phone, how they affect traditional security layouts. I will tell you how mobile phones dictate important client-server relationships.
Based on my other talks.
Presented at:
-
Tech meetup on Cactus Hackathon
Kyiv, Ukraine, May 2017 -
Women Who Code Kyiv meetup
Kyiv, Ukraine, March 2017
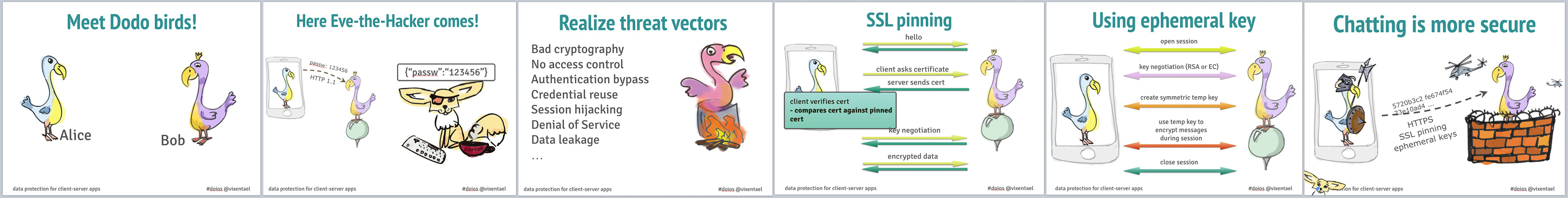
#security #workshop #mobile #ssl
| slides | no video | github repo |
|---|
The idea was to share some knowledges about making more secure apps. We talked about:
- why SSL is not enough
- strategies to implement SSL pinning
- how to understand basic risks and threats of common mobile client-server infrastructure
- protection methods against those threats
- what is symmetric encryption; why we need it. where to store data and key.
- what is transfer encryption; when we need it.
Presented at:
- The Swift Alps
Crans-Montana, Switzerland, 10-11 Nov 2016
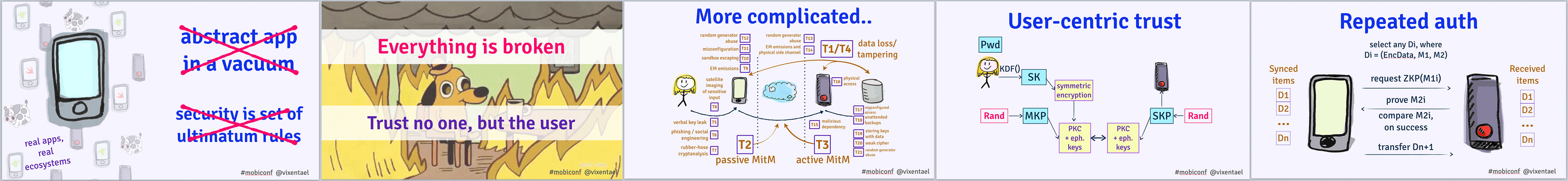
#security #keys #mobile #trust
| slides | EatDog video, 1h (ru) | MobiConf video, 40m (eng) |
|---|
We will talk about building security, that does not fail when application keys are exposed; when servers are hacked; security that lasts as long as unique user's crypto keys (or passwords) are safe. Putting secrets known by the user to be a source of trust is the ultimate way for an app to become "thin" in relation to the security model, thus lowering the risks and developer pain. We will learn about thin transparent security layers system and its applicability in client-server systems.
>>> Check for transcript and video on Realm (25m) <<<
Presented at:
-
MobiConf
Krakow, Poland, 6-8 Oct 2016 -
NSBarcelona
Barcelona, Spain, 21 Sept 2016 -
NSSpain
Logrono, Spain, 14-15 Sept 2016 -
try!swift
NYC, USA, 1-2 Sept 2016 -
EatDog
Kharkov, Ukraine, 18 August 2016
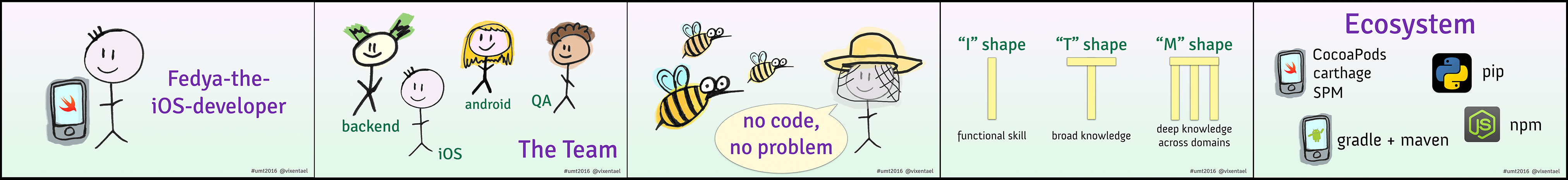
Multiskilled dev teams: unlock your hidden powers 🌩
#teammanagement #development
| slides | UMT video (ru) |
|---|
Everyone is talking about developers' specialization. 'Know you niche'. We have separate conferences for every dev area now: mobile, cloud, big data, iOT. In order to build a modern multiplatform mobile app you need to work with separate iOS and Android dev teams, separate backend dev team, designers and managers. Doesn't look too much?
I'll talk about another way of organization: multiskilled dev team, experience and benefits.
Presented at:
-
AgilePizza #49 meetup
Kyiv, Ukraine, 26 July 2016 -
UaMobiTech
Dnipro, Ukraine, 18-19 July 2016
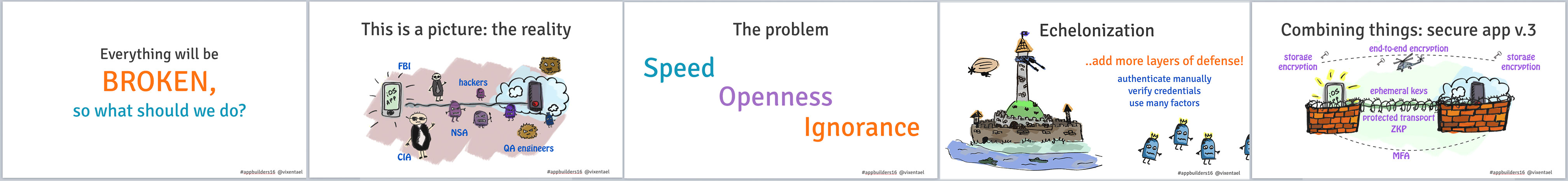
#security #trust #mobile #ZKP #KDF
| slides | CocoaHeads Video (ru) |
|---|
Mobile platforms present both new threats and new opportunities for system security. This presentation deals with modern approaches: how to protect data, which trust relationships emerge with mobile phone, how they affect traditional security layouts. How mobile phones dictate important client-server relationships.
But, what’s more important, we talk about making these things a consistent system: how to think to pick the right tools, which architectural patterns enforce security and minimize risks by design. We learn about ideas of echelonized defence, compartmentation and risk control. We finish with understanding where we stand right now: in security landscape that is rapidly changing, and mobile’s role in it is both dangerous and very important.
>>> Read more in Medium post <<<
Presented at:
-
AppBuilders 16
Zurich, Switzerland, 25-26 Apr 2016 -
CocoaHeads Kyiv #9
Kyiv, Ukraine, June 2016
#teammanagement #development #design #mobile
| slides | video (ru) |
|---|
As the developer, I don’t want to be frustrated when I need to convert designs into assets.
We will talk about:
- lots of tools and ways how to save own time
- how to communicate with designer, and
- if it’s okay to change designs on our own
Presented at:
- ITSubbota meetup
Kyiv, Ukraine, May 2016
#security #trust #mobile #architecture
| slides | Do iOS video (eng) |
|---|
- communication with server: security, reliability, ease of use, choose two
- applied cryptography: should you manually configure CommonCrypto or ...?
- practical example: protecting network transport without breaking the app
- storage security: how to prevent anyone reading your secret chat messages
>>> Read more in Medium post <<<
Presented at:
-
CocoaHeads Kyiv
Kyiv, Ukraine, December 2015 -
CocoaConfBy
Minsk, Belarus, December 2015 -
do{iOS}
Amsterdam, Netherlands, November 2015
#security #mobile #architecture
| slides | no video |
|---|
- Wise fish knows there ain’t enough talks about security
- Communication with server: security, reliability, ease of use, choose two
- Applied cryptography: should you manually configure CommonCrypto or …?
- Network security is piranha in risk and ruff in implementation
- Practical example: protecting network transport without breaking app
Presented at:
- Lviv Mobile Dev Day
Lviv, Ukraine, October 2015
#mobile #development #nlp
| slides | no video |
|---|
Short story about building app with profanity text filter inside.
- profanity filters: why we need them in mobile at all?
- handle tricky cases: what is wrong with word 'classic'
- how to filter fast (strings vs sets)
- gentle filtering not to scare users
Presented at:
- ITSubbota meetup
Kyiv, Ukraine, September 2015
#security #mobile #usersdata #commoncrypto
| slides | video (ru) |
|---|
-
Why should we think about security at all.
-
How to protect the users' data. Why shouldn't we store passwords. Encrypt database: it is necessary or too lazy to do that?
-
How to transfer data to the server in a safe way. What is MitM attack?
-
What is password protection? Why snapshots and pasteboard are dangerous?
Presented at:
- WebCamp
Odessa, Ukraine, July 2015
#backend #mobile #parse #development
| slides | video (ru) |
|---|
- How many developers are needed to write client-server mobile app? Fun and easy: set up a new app with Parse.com.
- Feeling confident enough to use own server? Check migration issues.
- Own experience: limitations and best practices
>>> Read more in Medium post <<<
Presented at:
- Stanfy MadCode Meetup #5
Kyiv, Ukraine, April 2015
#teammanagement #development #mobile
| slides | no video |
|---|
Nice and useful things to do if you feel too lazy to write code today.
Presented at:
- ITSubbota meetup
Kyiv, Ukraine, April 2015
#teammanagement #development #backend #mobile
| slides | no video |
|---|
This MadCode Webinar was dedicated to the effective interactions between mobile and backend developers to find the ways of productive communications with the latter not spending their time on finding who made errors, but rather building great products together.
>>> Read more in Medium post <<<
Presented at:
- Stanfy MadCode Meetup #1
Kyiv, Ukraine, November 2014