BLint is a Binary Linter to check the security properties, and capabilities in your executables. It is powered by lief
Supported binary formats:
- ELF (GNU, musl)
- PE (exe, dll)
- Mach-O (x64, arm64)
You can run blint on Linux, Windows and Mac against any of these binary formats.
Nowadays, vendors distribute statically linked binaries produced by golang or rust or dotnet tooling. Users are used to running antivirus and anti-malware scans while using these binaries in their local devices. Blint augments these scans by listing the technical capabilities of a binary. For example, whether the binary could use network connections, or can perform file system operations and so on.
The binary is first parsed using lief framework to identify the various properties such as functions, static, and dynamic symbols present. Thanks to YAML based annotations data, this information could be matched against capabilities and presented visually using a rich table.
NOTE: The presence of capabilities doesn't imply that the operations are always performed by the binary. Use the output of this tool to get an idea about a binary. Also, this tool is not suitable to review malware and other heavily obfuscated binaries for obvious reasons.
- Quickly identify malicious binaries by looking at their capabilities (Ability to manipulate networks or drivers or kernels etc)
- Add blint to CI/CD to inspect the final binaries to ensure code signing or authenticode is applied correctly
- Identify interesting functions and symbols for fuzzing
- Install python 3.8 or above
pip3 install blintYou can download single binary builds from the blint-bin releases. These executables should work with requiring python to be installed. The macOS .pkg file is signed with a valid developer account.
usage: blint [-h] [-i SRC_DIR_IMAGE] [-o REPORTS_DIR] [--no-error] [--no-banner] [--no-reviews]
Linting tool for binary files powered by lief.
optional arguments:
-h, --help show this help message and exit
-i SRC_DIR_IMAGE [SRC_DIR_IMAGE ...], --src SRC_DIR_IMAGE [SRC_DIR_IMAGE ...]
Source directories, container images or binary files. Defaults to current directory.
-o REPORTS_DIR, --reports REPORTS_DIR
Reports directory
--no-error Continue on error to prevent build from breaking
--no-banner Do not display banner
--no-reviews Do not perform method reviews
--suggest-fuzzable Suggest functions and symbols for fuzzing based on a dictionaryTo test any binary including default commands
blint -i /bin/netstat -o /tmp/blintUse -i to check any other binary. For eg: to check ngrok
blint -i ~/ngrok -o /tmp/blintPass --suggest-fuzzable to get suggestions for fuzzing. A dictionary containing "common verbs" is used to identify these functions.
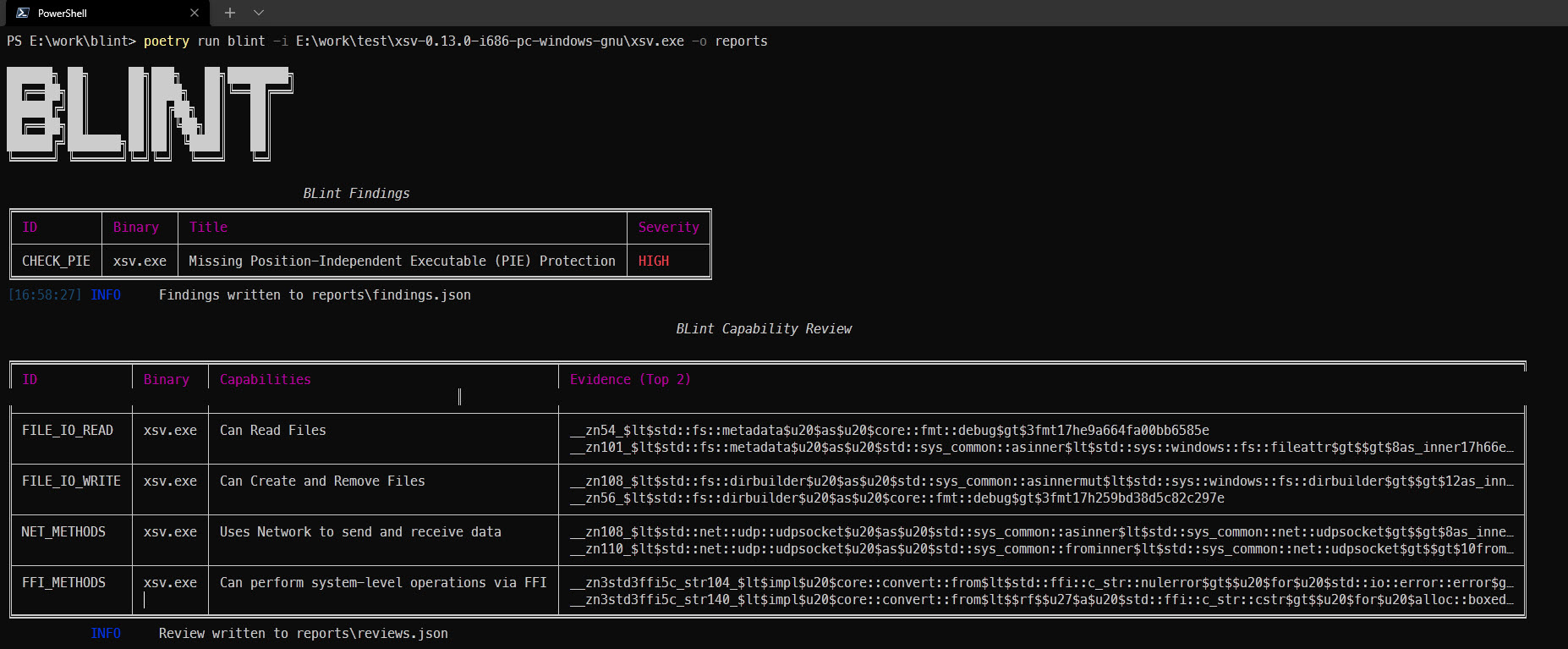
blint -i ~/ngrok -o /tmp/blint --suggest-fuzzablePowerShell example
Blint produces the following json artifacts in the reports directory:
- blint-output.html - HTML output from the console logs
- exename-metadata.json - Raw metadata about the parsed binary. Includes symbols, functions, and signature information
- findings.json - Contains information from the security properties audit. Useful for CI/CD based integration
- reviews.json - Contains information from the capability reviews. Useful for further analysis
- fuzzables.json - Contains a suggested list of methods for fuzzing
The developers could be reached via the discord channel.