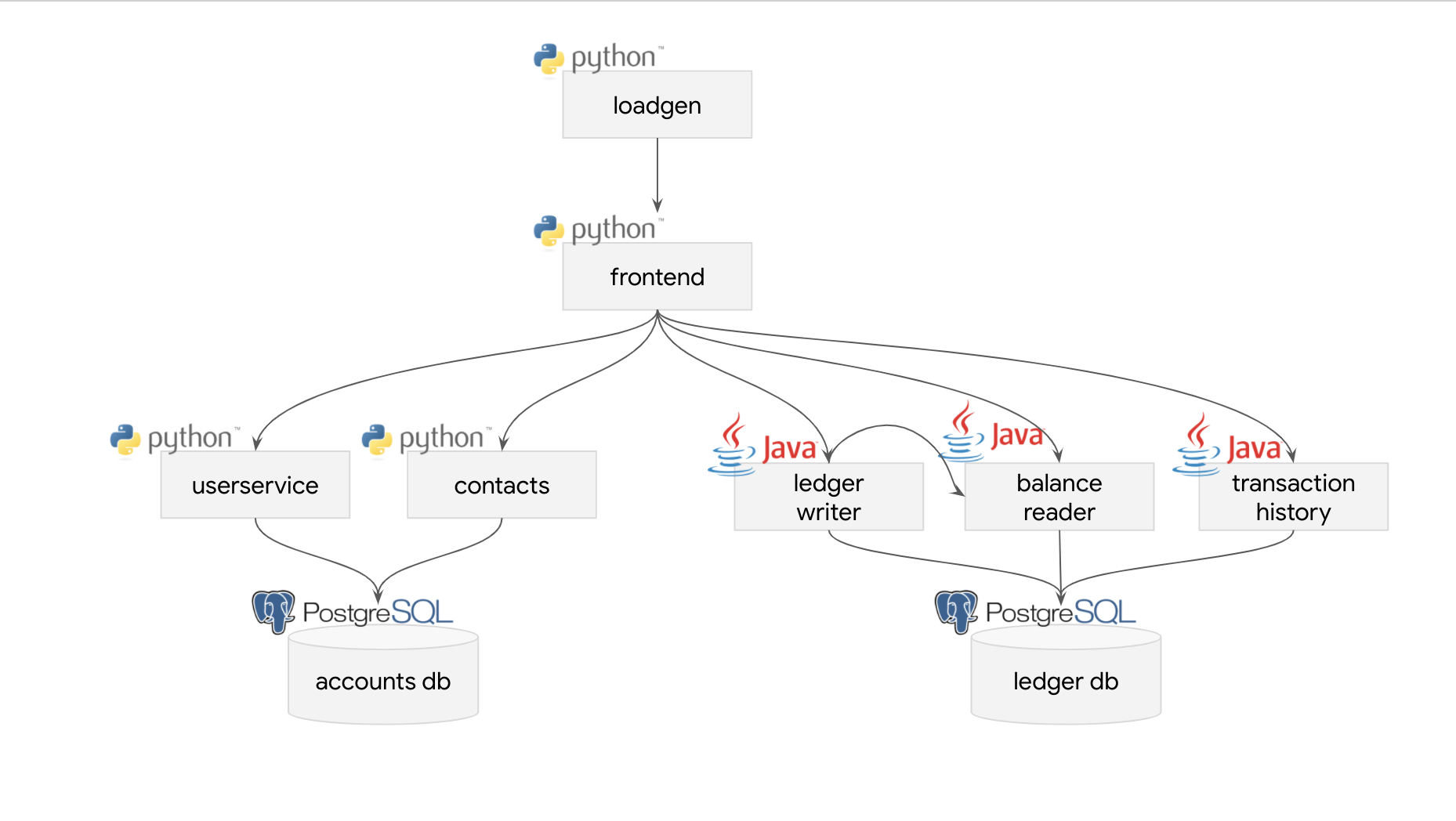
This project simulates a bank's payment processing network using Anthos. Bank of Anthos allows users to create artificial accounts and simulate transactions between accounts. Bank of Anthos was developed to create an end-to-end sample demonstrating Anthos best practices.
| Service | Language | Description |
|---|---|---|
| frontend | Python | Exposes an HTTP server to serve the website. Contains login page, signup page, and home page. |
| ledger-writer | Java | Accepts and validates incoming transactions before writing them to the ledger. |
| balance-reader | Java | Provides efficient readable cache of user balances, as read from ledger-db. |
| transaction-history | Java | Provides efficient readable cache of past transactions, as read from ledger-db. |
| ledger-db | PostgreSQL | Ledger of all transactions. Option to pre-populate with transactions for demo users. |
| user-service | Python | Manages user accounts and authentication. Signs JWTs used for authentication by other services. |
| contacts | Python | Stores list of other accounts associated with a user. Used for drop down in "Send Payment" and "Deposit" forms. |
| accounts-db | PostgreSQL | Database for user accounts and associated data. Option to pre-populate with demo users. |
| loadgenerator | Python/Locust | Continuously sends requests imitating users to the frontend. Periodically created new accounts and simulates transactions between them. |
Create a Google Cloud Platform project or use an existing project. Set the PROJECT_ID environment variable and ensure the Google Kubernetes Engine API is enabled.
PROJECT_ID=<your-project-id>
gcloud beta services enable container --project ${PROJECT_ID}
Clone this repository to your local environment and cd into the directory.
git clone https://github.com/GoogleCloudPlatform/bank-of-anthos.git
cd bank-of-anthos
ZONE=<your-zone>
gcloud beta container clusters create bank-of-anthos \
--project=${PROJECT_ID} --zone=${ZONE} \
--machine-type=n1-standard-2 --num-nodes=4
openssl genrsa -out jwtRS256.key 4096
openssl rsa -in jwtRS256.key -outform PEM -pubout -out jwtRS256.key.pub
kubectl create secret generic jwt-key --from-file=./jwtRS256.key --from-file=./jwtRS256.key.pub
kubectl apply -f ./kubernetes-manifests
After 1-2 minutes, you should see that all the pods are running:
kubectl get pods
Example output - do not copy
NAME READY STATUS RESTARTS AGE
accounts-db-6f589464bc-6r7b7 1/1 Running 0 99s
balancereader-797bf6d7c5-8xvp6 1/1 Running 0 99s
contacts-769c4fb556-25pg2 1/1 Running 0 98s
frontend-7c96b54f6b-zkdbz 1/1 Running 0 98s
ledger-db-5b78474d4f-p6xcb 1/1 Running 0 98s
ledgerwriter-84bf44b95d-65mqf 1/1 Running 0 97s
loadgenerator-559667b6ff-4zsvb 1/1 Running 0 97s
transactionhistory-5569754896-z94cn 1/1 Running 0 97s
userservice-78dc876bff-pdhtl 1/1 Running 0 96s
kubectl get svc frontend | awk '{print $4}'
Example output - do not copy
EXTERNAL-IP
35.223.69.29
Note: you may see a <pending> IP for a few minutes, while the GCP load balancer is provisioned.
Paste the frontend IP into a web browser. You should see a log-in screen:
Using the pre-populated username and password fields, log in as testuser. You should see a list of transactions, indicating that the frontend can successfully reach the backend transaction services.
If you have enabled Workload Identity on your GKE cluster (a requirement for Anthos Service Mesh), follow these instructions to ensure that Bank of Anthos pods can communicate with GCP APIs.
Note - These instructions have only been validated in GKE on GCP clusters. Workload Identity is not yet supported in Anthos GKE on Prem.
-
Set up Workload Identity on your GKE cluster using the instructions here. These instructions create the Kubernetes Service Account (KSA) and Google Service Account (GSA) that the Bank of Anthos pods will use to authenticate to GCP. Take note of what Kubernetes
namespaceyou use during setup. -
Add IAM Roles to your GSA. These roles allow workload identity-enabled Bank of Anthos pods to send traces and metrics to GCP.
PROJECT_ID=<your-gcp-project-id>
GSA_NAME=<your-gsa>
gcloud projects add-iam-policy-binding ${PROJECT_ID} \
--member "serviceAccount:${GSA_NAME}@${PROJECT_ID}.iam.gserviceaccount.com" \
--role roles/cloudtrace.agent
gcloud projects add-iam-policy-binding ${PROJECT_ID} \
--member "serviceAccount:${GSA_NAME}@${PROJECT_ID}.iam.gserviceaccount.com" \
--role roles/monitoring.metricWriter- Generate Bank of Anthos manifests using your KSA as the Pod service account. In
kubernetes-manifests/, replaceserviceAccountName: defaultwith the name of your KSA. (Note - sample below is Bash.)
KSA_NAME=<your-ksa>
mkdir -p wi-kubernetes-manifests
FILES="`pwd`/kubernetes-manifests/*"
for f in $FILES; do
echo "Processing $f..."
sed "s/serviceAccountName: default/serviceAccountName: ${KSA_NAME}/g" $f > wi-kubernetes-manifests/`basename $f`
done- Deploy Bank of Anthos to your GKE cluster using the install instructions above, except make sure that instead of the default namespace, you're deploying the manifests into your KSA namespace:
NAMESPACE=<your-ksa-namespace>
kubectl apply -n ${NAMESPACE} -f ./wi-kubernetes-manifests The default app deployment uses a microservices architecture on Kubernetes. The Ledger Monolith variant deploys part of the app as a monolith service on a separate VM hosted by Google Compute Engine.
Read more about the Ledger Monolith service under its subdirectory: src/ledgermonolith
Deploy the Ledger Monolith to a VM and update the banking app to use it to track the bank ledger.
make monolith
See the Development Guide for instructions on how to build and develop services locally, and the Contributing Guide for pull request and code review guidelines.
This is not an official Google project.