- SSL/TLS text context capture, support openssl\gnutls\nspr(nss) libraries.
- bash audit, capture bash command for Host Security Audit.
- mysql query SQL audit, support mysqld 5.6\5.7\8.0, and mariadDB.
Download ELF zip file release , unzip and use by command ./ecapture --help.
- Linux kernel version >= 4.18
- Enable BTF BPF Type Format (BTF)
cfc4n@vm-server:~$# uname -r
4.18.0-305.3.1.el8.x86_64
cfc4n@vm-server:~$# cat /boot/config-`uname -r` | grep CONFIG_DEBUG_INFO_BTF
CONFIG_DEBUG_INFO_BTF=ycapture tls text context. Step 1:
./ecapture tls --hexStep 2:
curl https://github.comcapture bash command.
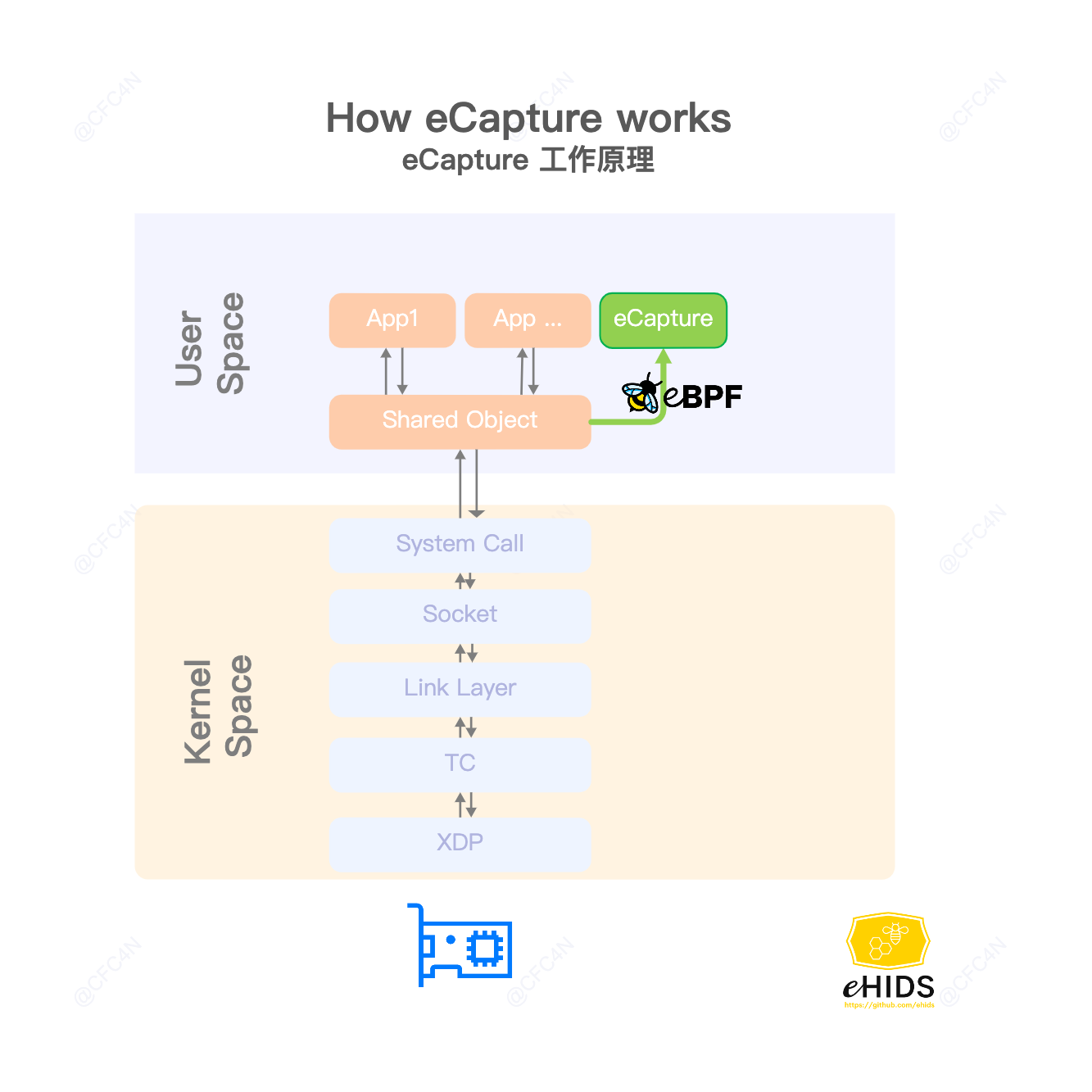
ps -ef | grep fooeCapture hookSSL_write \ SSL_read function of shared library /lib/x86_64-linux-gnu/libssl.so.1.1. get text context, and send message to user space by eBPM map.
Probes: []*manager.Probe{
{
Section: "uprobe/SSL_write",
EbpfFuncName: "probe_entry_SSL_write",
AttachToFuncName: "SSL_write",
//UprobeOffset: 0x386B0,
BinaryPath: "/lib/x86_64-linux-gnu/libssl.so.1.1",
},
{
Section: "uretprobe/SSL_write",
EbpfFuncName: "probe_ret_SSL_write",
AttachToFuncName: "SSL_write",
//UprobeOffset: 0x386B0,
BinaryPath: "/lib/x86_64-linux-gnu/libssl.so.1.1",
},
{
Section: "uprobe/SSL_read",
EbpfFuncName: "probe_entry_SSL_read",
AttachToFuncName: "SSL_read",
//UprobeOffset: 0x38380,
BinaryPath: "/lib/x86_64-linux-gnu/libssl.so.1.1",
},
{
Section: "uretprobe/SSL_read",
EbpfFuncName: "probe_ret_SSL_read",
AttachToFuncName: "SSL_read",
//UprobeOffset: 0x38380,
BinaryPath: "/lib/x86_64-linux-gnu/libssl.so.1.1",
},
/**/
},hook /bin/bash readline symbol name.
Linux Kernel: >= 4.18.
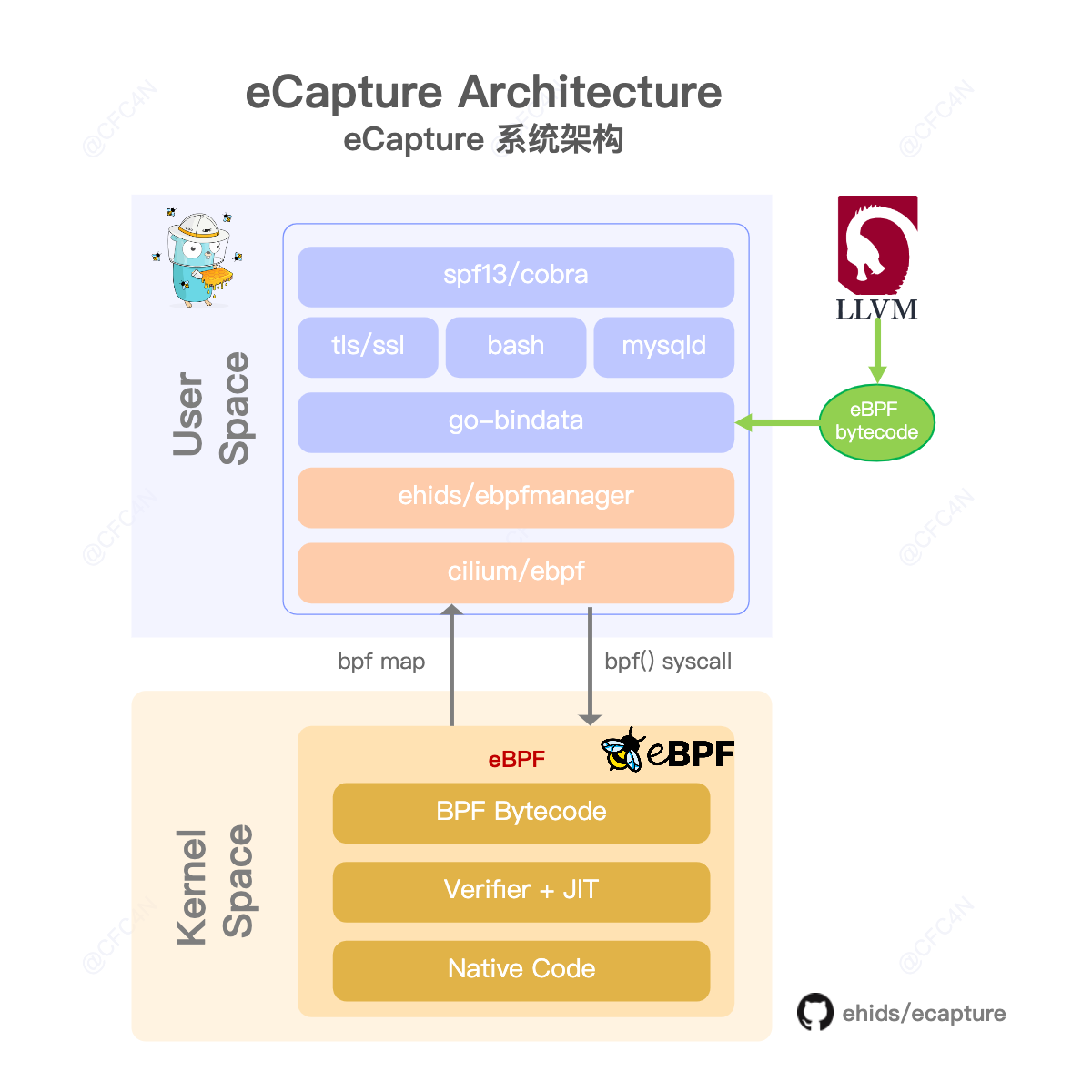
- golang 1.16
- gcc 10.3.0
- clang 12.0.0
- cmake 3.18.4
- clang backend: llvm 12.0.0
- pahole >= v1.13
- kernel config:CONFIG_DEBUG_INFO_BTF=y (Optional, 2022-04-17)
git clone git@github.com:ehids/ecapture.git
cd ecapture
make
bin/ecapture --helpeCapture support NO BTF with command make nocore to compile on 2022/04/17.
make nocore
bin/ecapture --helpSee CONTRIBUTING for details on submitting patches and the contribution workflow.